Windows is a very complex operating system, that contains a lot of internal mechanisms that are needed to make the system stable and fast. A lot of system processes are launched together with the system start, so when you open the Task Manager, your eyes will likely run because of dozens of different operations in it. Let’s figure out why they are needed, which problems may occur with them, and how these processes can be used by malware.
What are Windows processes?
Windows processes are a chain of mechanisms that are launched by the operating system at its start. These mechanisms have been evolving since the Windows NT appearance, and are adjusting constantly for the best performance of the operating system. System processes control the dynamic-link library behavior, allows the users to interact with the DLLs, animation effects you can see while using the OS, and a lot of other stuff that may be needed for some users.
Some of these processes are responsible for the functions that are demanded by a very little number of users. However, because of Microsoft’s attempt to make Windows 100% inclusive, these mechanisms are launched regardless of your needs. In our articles, you will get full information about the service purpose, and the guide of its disabling if you don’t need this feature to be on.
Can system processes be used in malevolent ways?
Some of the services offered by Windows by default may be used as a vulnerability. Another case when the system process may be recognized as malicious is when malware mimics them, creating the processes named the same as system ones. However, such counterfeits may easily be distinguished from the legit processes: viruses can only launch themselves as a user’s process, not as the process of Windows. Hence, the duplicates launched as a user’s task is likely a malicious item.
But don’t be confused! There are also a lot of processes of different applications that may look like system ones but launched as the process of the current user(s). Intel, nVidia, AMD, Realtek, and a lot of other hardware producers include the application for the interaction with their devices into the initial distribution package, and these apps are running in the background together with other user’s programs. To check the program the process belongs to, click it with a right mouse button, and choose the “Open file location” option.
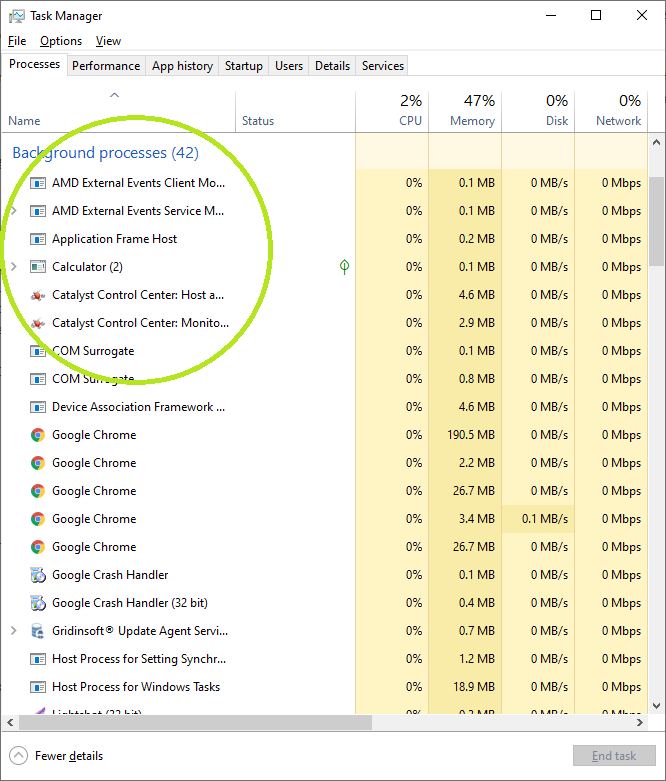
All these processes belong to AMD GPU-related software
Here is the list of the processes that you can see in the Task Manager. Check them out to see the complete information about each of them:
