Rundll32.exe is a legitimate Windows process used to run functions stored inside DLL files. It is not automatically malware. The reason it causes confusion is simple: malware can also use rundll32.exe to launch a malicious DLL, or it can place a fake copy of rundll32.exe in the wrong folder.
What is Rundll32.exe?
Windows and many applications use DLL files as shared code libraries. Rundll32.exe provides a way to call exported functions inside those DLLs. This is normal Windows behavior, and seeing rundll32.exe in Task Manager does not prove infection.
The command line matters. A safe rundll32.exe process should usually point to a known Windows or trusted application DLL. A suspicious one may launch a DLL from AppData, Temp, Downloads, or a random folder.
Safe vs suspicious signs
| Usually legitimate | Suspicious |
| Executable is in System32 or SysWOW64. | Executable is in AppData, Temp, Downloads, or another random folder. |
| Command line loads a known Windows or trusted vendor DLL. | Command line loads a random DLL from a user profile folder. |
| Signed by Microsoft. | Unsigned fake copy or unknown publisher. |
| Short activity tied to Control Panel, settings, drivers, or apps. | Runs constantly, creates persistence, or returns after deletion. |
How to inspect Rundll32.exe properly
- Open Task Manager and add the Command line column, or use Process Explorer.
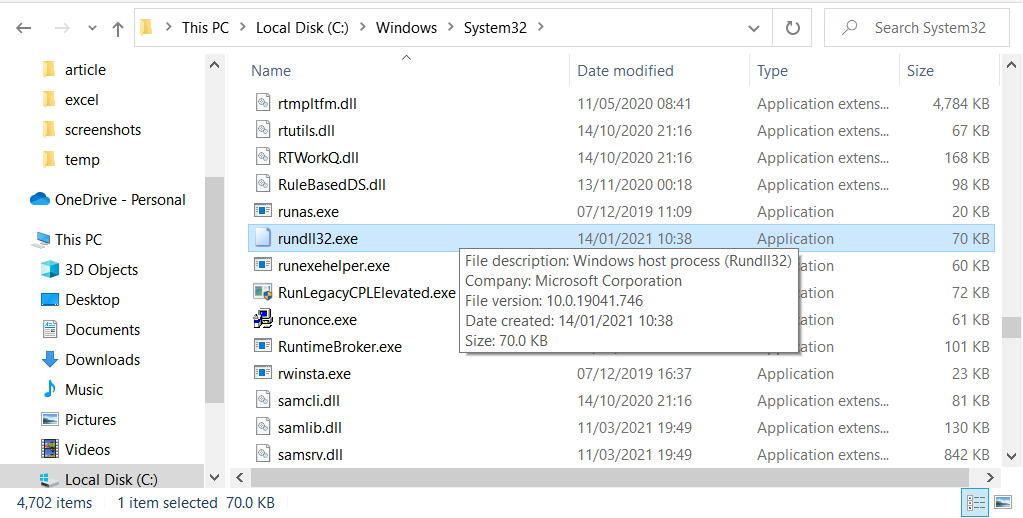
- Check the full path to rundll32.exe.
- Read the DLL path shown in the command line.
- If the DLL is in a user-writable folder, scan it and inspect startup entries.
- If the DLL belongs to a trusted application, update or repair that application.
Why malware uses Rundll32.exe
Rundll32.exe is trusted and common, so attackers may use it to run malicious DLLs while blending into normal Windows activity. This does not make rundll32.exe itself malicious. The suspicious part is usually the DLL, the path, or the persistence mechanism that launches it.
How to fix suspicious Rundll32 activity
If rundll32.exe points to a suspicious DLL, do not delete random Windows files. Remove the startup entry, scheduled task, service, or parent program that launches the DLL. Then scan the file and the whole system. If the command line points to a legitimate application DLL and the process crashes or uses CPU, repair or reinstall that application.
Common false alarms
Rundll32.exe may appear when opening display settings, audio drivers, printer tools, Control Panel items, graphics utilities, or vendor control panels. Temporary activity in those cases is normal. Constant activity from a strange user-folder DLL is not.
Decision tree: which file is suspicious?
There are two different things to verify: the rundll32.exe executable and the DLL it launches. If rundll32.exe itself is outside Windows folders, the executable is suspicious. If rundll32.exe is the real Microsoft file but the command line loads a DLL from a strange location, the DLL or its startup mechanism is suspicious.
This distinction matters because deleting the real rundll32.exe is a serious mistake. The fix is usually to remove the malicious DLL and the task, service, or registry entry that launches it.
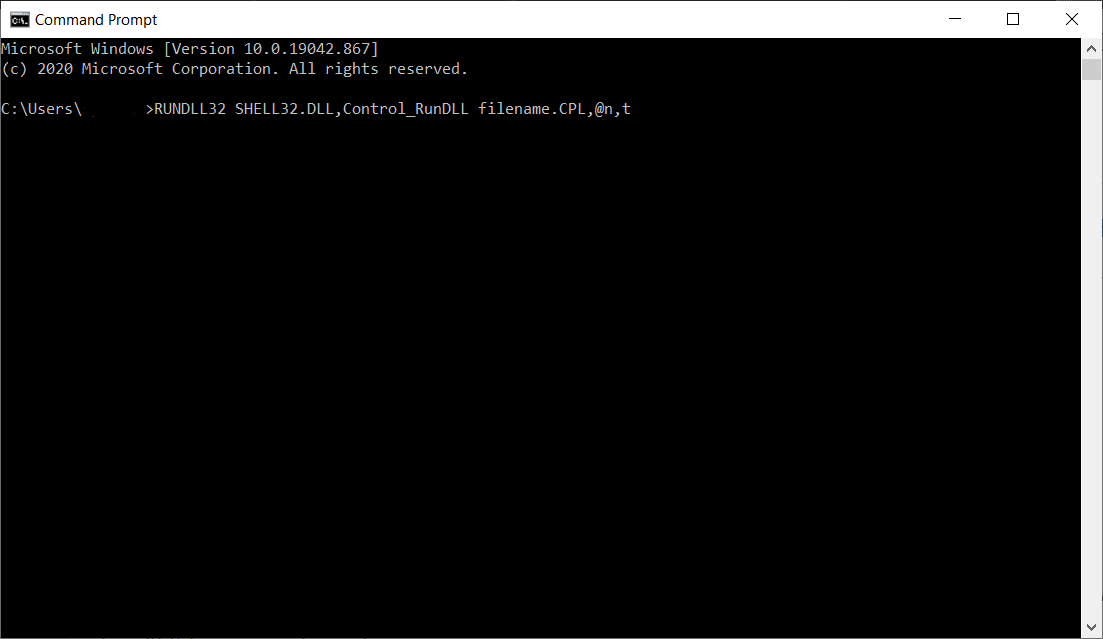
How to see the full command line
In Task Manager, open the Details tab, right-click the column header, choose Select columns, and enable Command line. You can also use Process Explorer for a clearer view. Look for the DLL path after rundll32.exe. A path under System32, SysWOW64, or a trusted application folder can be normal. A DLL under AppData, Temp, Downloads, or a random folder is a red flag.
Common legitimate uses
Display settings, audio drivers, printer utilities, Control Panel applets, graphics drivers, Bluetooth software, and vendor configuration tools may briefly use rundll32.exe. Short-lived activity after opening settings is normal. A rundll32.exe process that starts at boot and runs forever from a suspicious command line deserves investigation.
After cleanup
After removing a suspicious rundll32 launch, reboot and check Task Scheduler, Startup folders, Services, and browser extensions. If the suspicious DLL returns, the launcher was not removed. If a legitimate application DLL was causing crashes, update or reinstall that application instead of removing Windows components.
Extra checks for persistent Rundll32 launches
If the same rundll32.exe command returns after reboot, copy the full command line before changing anything. Search the registry Run keys, Startup folders, and Task Scheduler for the DLL path or the folder name. If the DLL belongs to a known vendor, repair that vendor software. If it belongs to an unknown folder, quarantine the DLL and remove the launcher together.
Also check whether the DLL was created recently. A new DLL in AppData that starts through rundll32.exe is much more suspicious than an old Microsoft-signed DLL in a Windows directory.
For business PCs, collect the command line and file hash before removal so the security team can trace where the DLL came from. That evidence is often more valuable than deleting the file immediately.
That record also helps avoid removing legitimate vendor software by mistake.
FAQ
Can I delete Rundll32.exe?
No. The real Windows file is needed. Investigate the DLL it is launching instead.
Why are there two locations?
64-bit Windows has System32 for 64-bit components and SysWOW64 for 32-bit compatibility components.
What is the fastest red flag?
A command line that loads a DLL from AppData, Temp, Downloads, or a random folder.


Leave a Comment