Another case of malware penetration into PyPI was discovered – 10 malicious packages were removed from the repository at once, as they could steal data from developers, including passwords and API tokens.
The problem is being reported by researchers at CheckPoint. Malicious packages have traditionally relied on typesquatting to spread, they said, meaning they were downloaded if a user misspelled the name of a genuinely popular package.Let me remind you that we also talked about The Student Makes a Joke and Placed the Ransomware in the PyPI Repository, and also that Malicious PyPI Packages Steal AWS Accounts.
In their report, the experts talk about the detection of the following malicious libraries.
- Ascii2text: Downloads a malicious script that collects passwords stored in browsers including Google Chrome, Microsoft Edge, Brave, Opera and Yandex Browser.
- Pyg-utils, Pymocks and PyProto2: Targeted at stealing credentials from AWS and very similar to another malware suite discovered by Sonatype in June. The first package even connects to the same domain (pygrata.com) and the other two use pymocks.com.
- Test-async and Zlibsrc: Download and execute malicious code from an external source during installation.
- Free-net-vpn, Free-net-vpn2 and WINRPCexploit: steal user credentials and environment variables.
- Browserdiv: Steals credentials and other information stored in the browser’s local storage folder. Uses Discord webhooks to steal data.
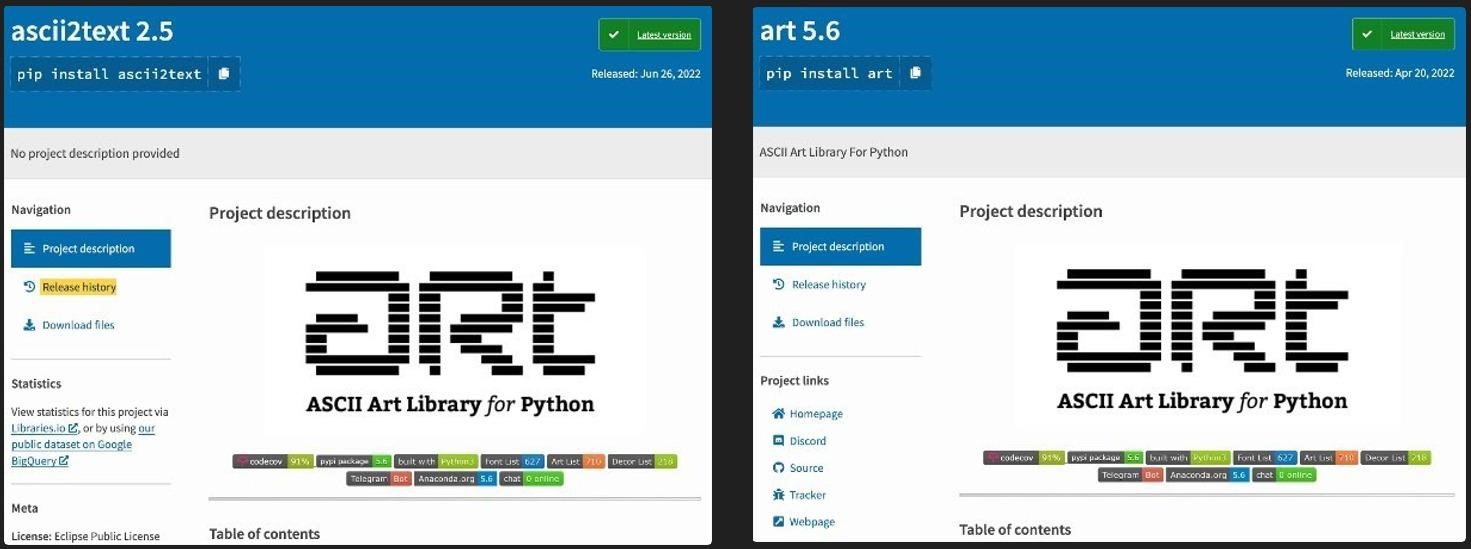
Fake / real library
The researchers do not know exactly how many times these malicious packages were downloaded, but they write that we are talking about at least hundreds of downloads.
While the malware has now been removed from PyPI, developers who download these packages may still be at risk. The researchers recommend victims to consider their machines completely compromised and take appropriate measures to “clean up” the system.


Leave a Comment