Cisco representatives confirmed that in May, Yanluowang extortionist group hacked the company’s corporate network.
Later, the attackers tried to extort money from Cisco, otherwise threatening to publish the data stolen during the attack in the public domain.The company emphasizes that the hackers managed to steal only non-confidential data from the Box folder associated with the hacked employee account.
Let me remind you that we also wrote that Cisco fixed critical vulnerability in Jabber for Windows.
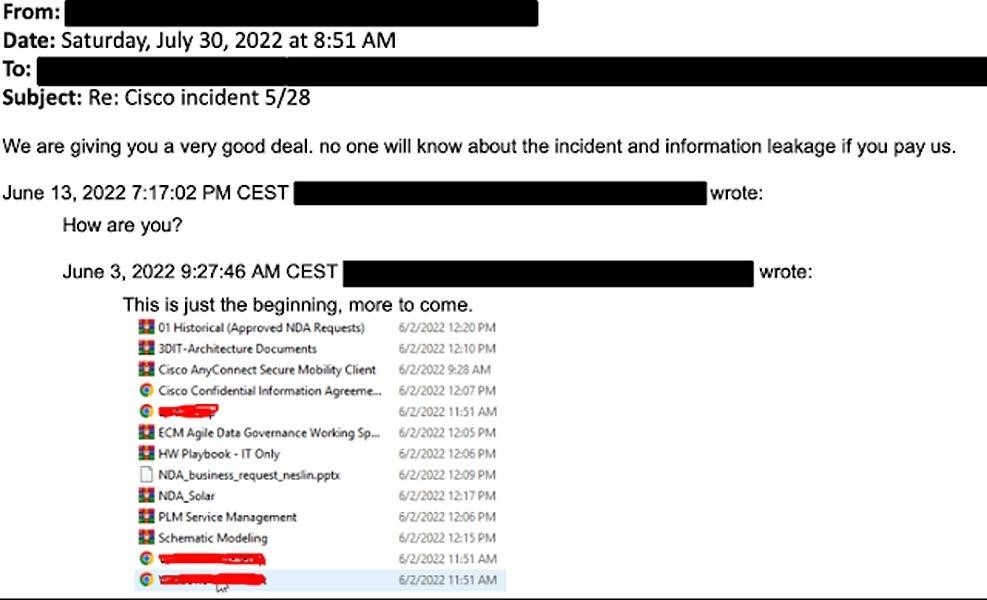
Hacker Threats
The company was prompted to publish an official statement by the fact that on August 10, data allegedly stolen from Cisco was made public on the darknet.
The investigation showed that Yanluowang members gained access to the Cisco network using credentials stolen from an employee after hacking into his personal Google account, which contained usernames and passwords synchronized with the browser.
During the attack on a Cisco employee, the attackers posed as support specialists and managed to force him to approve a multi-factor authentication push notification, including using “sophisticated voice phishing attacks.” When the victim finally approved one of the notifications, the hackers were able to access the VPN in the context of the target user.
Having infiltrated the corporate network, the Yanluowang operators extended their attack further to Citrix servers and domain controllers.
After gaining domain administrator rights, the hackers used tools such as ntdsutil, adfind, and secretsdump to collect additional information and installed a number of payloads, including a backdoor, on compromised systems. Also during the attack, the hackers used a variety of other tools, from remote access programs such as LogMeIn and TeamViewer to offensive solutions, including Cobalt Strike, PowerSploit, Mimikatz and Impacket, to maintain access.
Cisco eventually discovered the attack and blocked the hackers from accessing them, but they continued to try to regain access over the following weeks, although these attempts were unsuccessful.
Bleeping Computer journalists report that last week, Yanluowang operators contacted them by e-mail and sent a list of files allegedly stolen from Cisco during the attack.
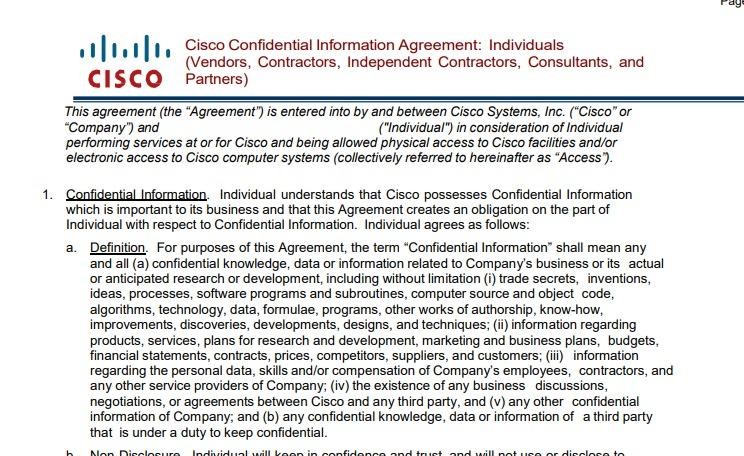
Then the hackers said they had stolen 2.75 GB of data (approximately 3100 files). According to the publication, many of these files are non-disclosure agreements, data dumps and technical documentation. The hackers also gave the publication an edited version of the non-disclosure agreement stolen during the attack as proof of their words.
Now, the ransomware has already announced the Cisco hack “officially” on its dark web site and has published the same list of files that Bleeping Computer has shown before.
Cisco says that Yanluowang usually encrypts the files of their victims, but the company’s specialists did not find any extortionate payloads on their network. At the same time, according to the Cisco report, the activity of the attackers was consistent with “ransomware activity commonly seen in victim company environments and leading to ransomware deployment.”


Leave a Comment