Fortinet experts have warned that attackers are actively exploiting an unpatched authentication bypass vulnerability discovered in TBK DVR devices in 2018.
Let me remind you that we also wrote that Researchers Discover 22-Year-Old Vulnerability in SQLite, and also that The Researcher Found an Old Bug in the PlayStation 5, Leading to a Jailbreak.You might want to read: For old school lovers: WACUP has fixed many bugs in Winamp.
The TBK Vision website claims that the company’s products are used in banks, government organizations, retail, and so on. Since DVR servers are used to store sensitive video recordings, they are usually located on company intranets to prevent unauthorized access to data.
Unfortunately, they are also very attractive to attackers who can use the DVR as an initial access point.
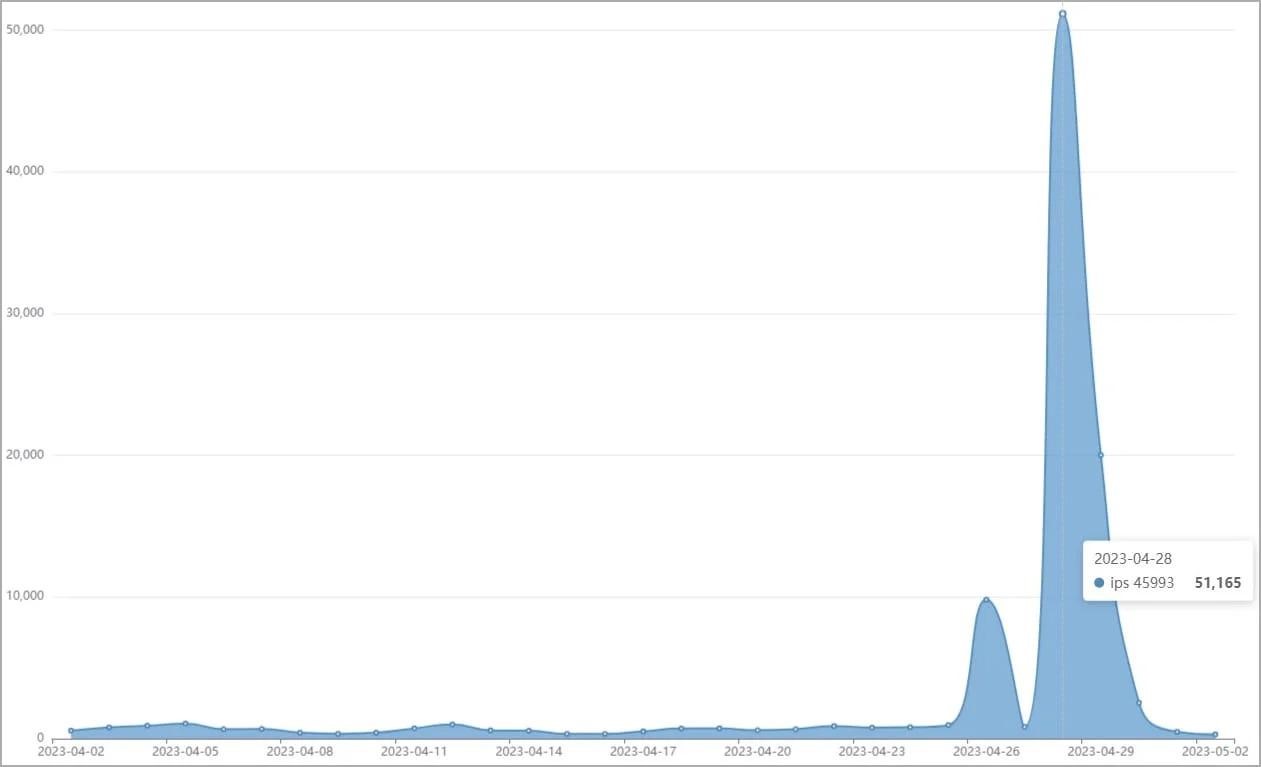
Fortinet experts write that recently there has been a surge in attacks on TBK DVR devices, with attackers using a critical vulnerability (9.8 points on the CVSS scale) CVE-2018-9995, discovered back in 2018, which allows bypassing authentication on the device. According to researchers, as of April 2023, there have been more than 50,000 attempts to compromise TBK devices using this vulnerability.
The fact is that a PoC exploit has long been available for this problem, using malicious HTTP cookies, to which vulnerable TBK devices respond with administrator credentials in JSON format.
The vulnerability affects the TBK DVR4104 and TBK DVR4216 devices, as well as the rebranding of these models, which are now sold as Novo, CeNova, QSee, Pulnix, XVR 5 in 1, Securus, Night OWL, DVR Login, HVR Login and MDVR.
Researchers report that they are not aware of any patches released to resolve CVE-2018-9995, so there are simply no fixes. Therefore, all owners of vulnerable devices are advised to replace their DVRs with new and supported devices as soon as possible.


Leave a Comment