VMware, the largest developer of virtualization software, has released updates to fix a number of vulnerabilities in Workstation and Fusion.
Among other bugs, a 0-day issue was fixed, which was discovered by experts during the Pwn2Own Vancouver 2023 hacker competition and allowed a local attacker to execute arbitrary code.The most serious issue of all was CVE-2023-20869 (9.3 on the CVSS scale), first demonstrated on Pwn2Own. It is described as a stack buffer overflow vulnerability found in the Bluetooth host device sharing feature with a virtual machine.
VMware also fixed an out-of-bounds read vulnerability affecting the same function (CVE-2023-20870, 7.1 CVSS score) that could be used by a local attacker with administrator rights to read sensitive information contained in the hypervisor’s memory .
Both vulnerabilities were demonstrated by researchers from the STAR Labs team on the third day of the Pwn2Own hacking competition held in Vancouver last month. These bugs earned the researchers an $80,000 reward.
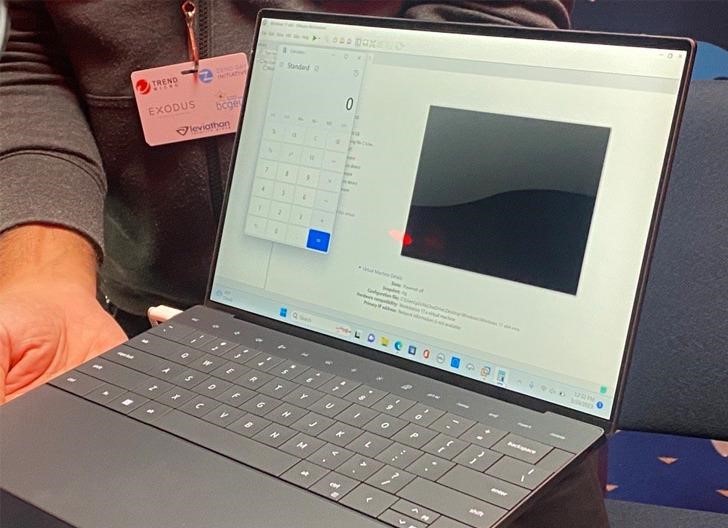
Hack on Pwn2Own
If, for some reason, patching is not possible, VMware has shared a workaround for exploitation protection CVE-2023-20869: You can disable Bluetooth support on the virtual machine by unchecking “Share Bluetooth devices with the virtual machine” on the affected devices.
Let me remind you that we also reported that VMware closes RCE vulnerability in ESXi and Horizon, and the media also reported that VMware Developers Fixed Serious Vulnerability In vSphere Replication.
In addition to these vulnerabilities, the company fixed two other issues affecting VMware Workstation and Fusion hypervisors. The first of these, CVE-2023-20871, is a local privilege escalation vulnerability in VMware Fusion Raw Disk. It could be abused by attackers with read/write access to the host operating system to elevate privileges and gain root access to the OS.
Another bug (CVE-2023-20872) is described as an out-of-bounds read/write vulnerability in the SCSI CD/DVD emulator. This bug affected both Workstation and Fusion products. It could be used by local attackers with access to a VM with a physical CD/DVD drive connected and configured to use SCSI, and would allow arbitrary code to be executed in the hypervisor.


Leave a Comment