Microsoft released the April patch set and fixed a total of 97 bugs in its products, including a 0-day vulnerability in Windows that Nokoyawa ransomware operators actively abused.
Let me remind you that we also wrote that Microsoft Support ‘Hacks’ Users Windows Due to Activation Issues, and also that Microsoft Scans Windows PCs for Outdated Versions of Office.
Also, as the media wrote, Information Security Specialists Discovered a 0-day Vulnerability in Windows Search.
For the second month in a row, Microsoft has released patches that close vulnerabilities in Windows that are already under attack. This time, the problem was CVE-2023-28252, which was related to privilege escalation to SYSTEM in the Windows Common Log File System (CLFS) driver.
The issue affects all supported server and client versions of Windows and can be exploited by local attackers in attacks that do not require user interaction.
As usual, Microsoft did not provide any further details about the exploitation of the problem and did not release indicators of compromise to help defenders in finding infections.
Although Microsoft reports that Mandiant and DBAPPSecurity researchers discovered this bug, it is also reported that this 0-day vulnerability was exploited by Nokoyawa ransomware operators.
The Nokoyawa malware has been active since around June 2022, and its operators have previously used other exploits that target CLFS with similar characteristics.
This suggests that they were all created by the same developer.
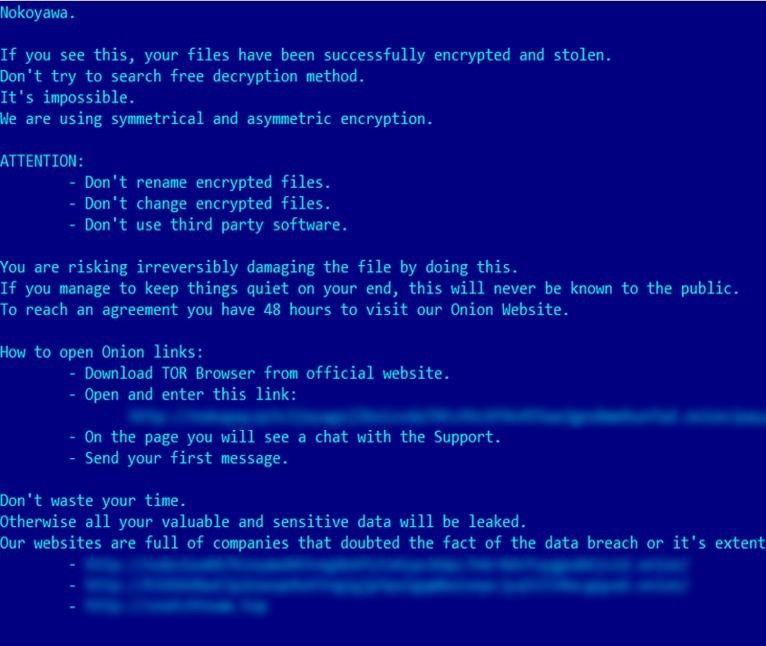
Ransom note
The researcher’s report states that the group used at least five CLFS exploits to attack a number of industries, including retail and wholesale, energy, manufacturing, healthcare and software development.
It should also be said that in addition to CVE-2023-28252, vulnerabilities in Microsoft Office, Word and Publisher were fixed this month that can be used for remote code execution when opening malicious documents. These bugs have been given the IDs CVE-2023-28285, CVE-2023-28295, CVE-2023-28287 and CVE-2023-28311.
Interestingly, according to the Trend Micro Zero Day Initiative (ZDI), organizer of the Pwn2Own hacking competition, none of the bugs found during last month’s Pwn2Own Vancouver have been fixed by Microsoft.
But in the blog, ZDI recommends that Windows users pay attention to the CVE-2023-21554 vulnerability associated with remote code execution in Microsoft Message Queuing (9.8 points out of 10 on the CVSS scale).
In addition to Microsoft, other companies have traditionally released updates for their products, including:
- Apple, which released updates to fix two actively exploited zero-day vulnerabilities in iOS and macOS;
- Adobe has released six security bulletins for 56 CVEs in Acrobat and Reader, Adobe Digital Editions, InCopy, Substance 3D Designer, Substance 3D Stager, and Adobe Dimension;
- SAP, which prepared the April patch set;
- Cisco has submitted 17 new and updated security bulletins, fixing 40 vulnerabilities;
- Fortinet has also published updates for a number of its products.


Leave a Comment