Phylum, a supply chain security company, discovered 29 malicious packages in the PyPI repository (the list can be found below) that infected their victims with the W4SP data-stealing malware.
Let me remind you that we also said that 10 Malicious PyPI Packages Steal Credentials, and also that Popular PyPI ctx Package Stole Developer’s Data.According to the researchers, the malicious packages imitated real-life popular libraries (also borrowing their code), that is, they used typesquatting to attract victims. According to Pepy.tech statistics, these packages have been downloaded more than 5700 times in total.
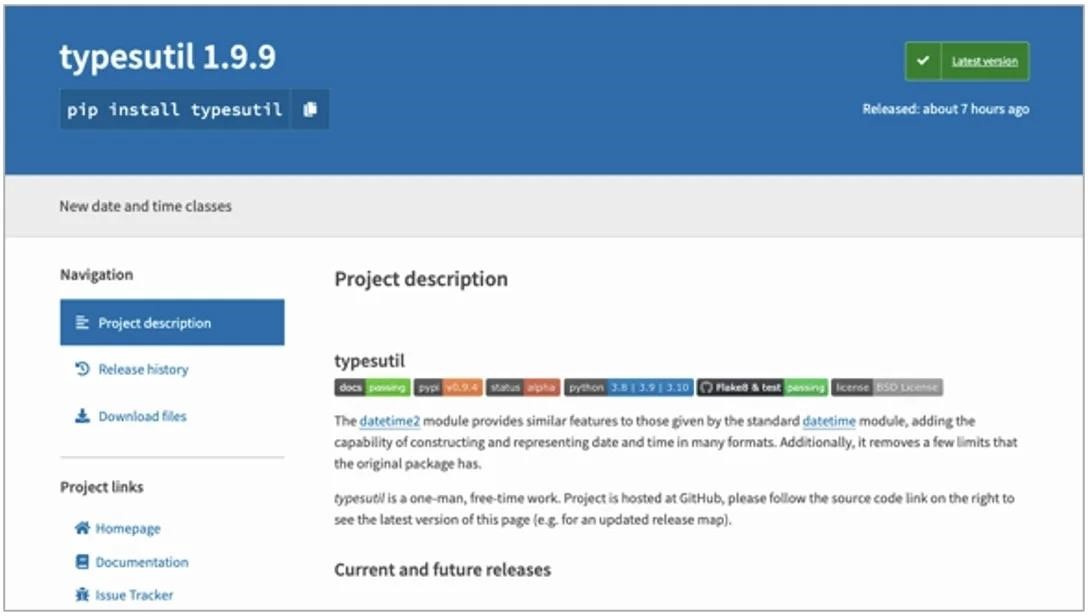
One of the fake packages
In their report, the analysts explain in detail what problems they had to face when studying the obfuscated code (over 71,000 characters), which turned out to be “rather dirty”, and through which they had to literally wade through.
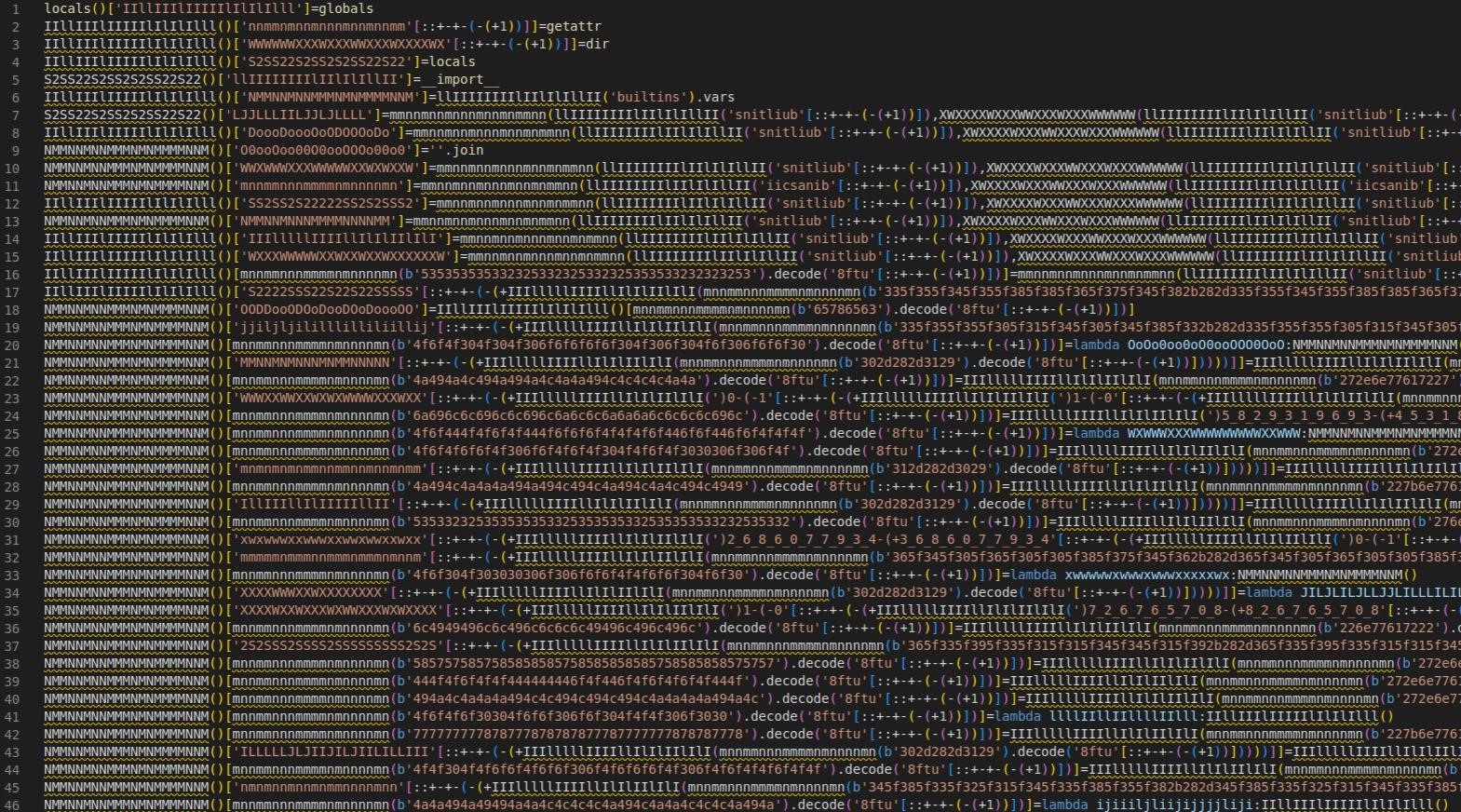
Obfuscated typosquats code
Ultimately, the researchers concluded that the malware distributed by these packages is the W4SP infostealer, which steals Discord tokens, cookies, and saves passwords from its victims.

Hauke Lübbers
The publication Bleeping Computer reports that this week independent information security specialist Hauke Lübbers also discovered the malware in PyPI. He managed to find the typesquatter pystile and threading packages containing the GyruzPIP malware.
According to the expert, this malware is based on the evil-pip open-source project, which is published online “for educational purposes only.” He also found two repositories on GitHub (1, 2), presumably owned by the authors of this malware, which he reported to the platform security team.
Lubbers has already reported the malicious packages to the PyPI administrators, although he thinks it is likely that the packages need to be used as dependencies in order for them to exhibit malicious behavior.
List of malicious packages found by Phylum researchers:
- algorithmic
- colorsama
- colorwin
- curlapi
- cypress
- duonet
- faq
- fatnoob
- felpesviadinho
- iao
- incrivelsim
- installpy
- oiu
- pydprotect
- pyhints
- pyptext
- pyslyte
- pystyle
- pystyte
- pyurllib
- requests-httpx
- shaasigma
- strinfer
- stringe
- sutiltype
- twyne
- type-color
- typestring
- typesutil


Leave a Comment