Renowned console hacker and exploit developer SpecterDev has released a PoC exploit for the PlayStation 5 that can be used to gain root privileges and read/write access to large areas of system memory.
Needless to say, the exploit cannot be used to actually execute arbitrary code and is intended more for other enthusiasts, but SpecterDev explains that this is an important step towards hacking the PlayStation 5.Let me remind you that we also talked about one exploit for the PlayStation 4 that may be useful for the PS5.
The SpecterDev exploit uses a problem we’ve covered before. In essence, the operation is based on setting up a fake DNS server on the local network in such a way that accessing the PS5 on-screen manual (which is loaded through a hidden web browser) will lead to a page on the local PC.
After that, the exploit uses a bug in the implementation of the PS5 browser, which is associated with a memory lock when setting IPv6 socket headers. Essentially, the exploit induces a race condition to access open socket header memory before it is fully locked. This allows you to start the process of reading or writing arbitrary data to large areas of PS5 memory through an RPC server on the host machine.
Since the exploit is based on a race condition, SpecterDev warns that it only works 30% of the time and in the process can lead to multiple kernel crashes (and subsequent long system restarts).
Currently, the exploit will not help with writing to low-level kernel space (which is still protected by the intact hypervisor) and will not help execute arbitrary code that the user can write to user space.
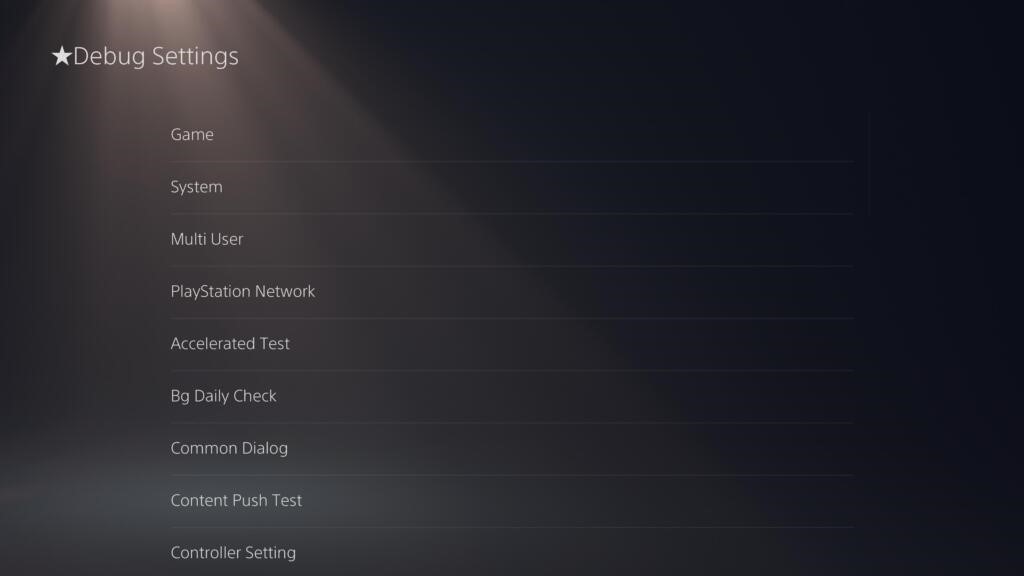
However, SpecterDev explains that the exploit provides access to the PS5’s debug menu and provides an entry point for hackers to learn more about the console’s memory and security systems in the future, as well as serve as a springboard for creating a full-fledged hack.
The exploit currently runs on firmware version 4.3 (released last October), and SpecterDev suggests that small changes will help it run on firmware 4.5 (released last December). In April this year, Sony marked the original issue as “fixed” on HackerOne, meaning the vulnerability will likely not work on firmware released since then.

