COM Surrogate is the friendly Task Manager name for dllhost.exe, a Windows host process used to run COM components outside the main application. It is often involved when File Explorer creates thumbnails, previews media files, or loads shell extensions. Seeing COM Surrogate is normal. Seeing it consume high CPU, disk, or memory for a long time means something it loaded needs attention.
What does COM Surrogate do?
Windows and third-party software use COM components for preview handlers, codecs, shell extensions, and other helper tasks. Running those components inside a surrogate process helps isolate crashes. If a bad codec or thumbnail handler fails, Explorer is less likely to crash directly; the surrogate process can fail instead.
This is why COM Surrogate often appears when opening folders with photos, videos, PDFs, or other preview-heavy files. The process may disappear after the preview work completes.
Common causes of high CPU or disk usage
| Trigger | What to check |
| Corrupted media file | Usage spikes only in one folder or when thumbnails are generated. |
| Broken codec pack | Issue started after installing video tools, players, or codec bundles. |
| Shell extension problem | Right-click menus, previews, or Explorer windows become slow. |
| Malware using a similar name | dllhost.exe runs outside System32 or launches from a strange path. |
Check whether dllhost.exe is legitimate
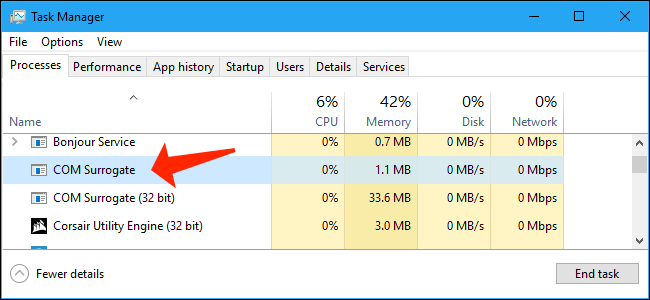
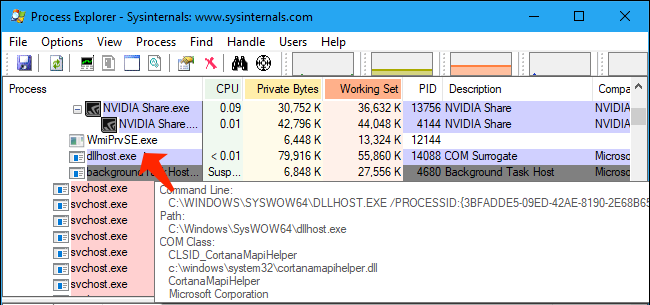
In Task Manager, right-click COM Surrogate and choose Open file location. The legitimate Windows file is normally C:\Windows\System32\dllhost.exe. You can also use Process Explorer to see which COM object or parent process is tied to a specific dllhost.exe instance.
Fix COM Surrogate high CPU or disk usage
- Notice what you were doing when usage spiked. If it happens in one folder, move suspicious media files out and test again.
- Disable thumbnail previews temporarily in File Explorer Options to confirm whether thumbnails are the trigger.
- Clear the thumbnail cache with Disk Cleanup or Windows Storage settings.
- Remove recently installed codec packs, video converters, shell extensions, or file preview tools.
- Update graphics drivers and media-related apps if the issue began after a Windows update.
- Run
sfc /scannowand DISM repair commands if Explorer or thumbnails remain unstable. - Run a full malware scan if dllhost.exe is not located in System32 or if usage appears at boot without Explorer activity.
When not to panic
A short COM Surrogate spike while opening a folder full of videos or images is normal. Windows may be creating thumbnails, reading metadata, or loading preview handlers. The red flag is repeated high usage in the same folder, repeated crashes, or a dllhost.exe copy outside the Windows folder.
How to find the file or extension causing it
If COM Surrogate spikes only in one folder, the trigger is often one file or one preview handler. Change File Explorer to Details view, disable Preview pane, and temporarily turn off thumbnails. Then move half the files to a test folder. If the spike follows one group of files, narrow it down until you find the damaged video, image, PDF, or archive.
If the spike happens everywhere, look beyond one file. Recently installed media players, codec packs, cloud storage shell extensions, archive tools, PDF preview handlers, and camera software can add Explorer extensions. Disable or uninstall the newest extension first. Microsoft Sysinternals Autoruns and ShellExView-style tools can help advanced users inspect shell extensions, but do not disable Microsoft entries blindly.
Security check without overreacting
The name “COM Surrogate” sounds suspicious, so many old SEO pages treat it as malware by default. That is misleading. The real process is a normal Windows host. Security review is needed when the file path is wrong, when multiple copies run from user-writable folders, or when usage appears at boot without any Explorer or preview activity. In that case, scan the file path and check scheduled tasks and startup entries.
What good looks like after repair
After clearing thumbnail cache, removing a bad codec, or isolating a corrupted file, COM Surrogate should still appear occasionally, but it should no longer sit at high CPU or disk usage for long periods. Opening media-heavy folders may still create short spikes; sustained idle usage is the part that should be gone.
Fast checklist
- Real Windows file:
C:\Windows\System32\dllhost.exe. - Most common harmless trigger: thumbnails or previews in a folder with media files.
- Most common fix: clear thumbnail cache and remove the bad codec, preview handler, or corrupted file.
- Most important warning sign: dllhost.exe running from outside the Windows folder.
Why old removal advice is risky
Deleting dllhost.exe or blocking COM Surrogate because it appears in Task Manager can break normal Windows behavior. Explorer previews, Control Panel items, and third-party shell features may rely on surrogate hosting. A careful guide should separate the host process from the component loaded inside it. The host can be legitimate while the loaded codec or extension is broken.
That distinction is the main SEO and usefulness gap in many older pages. People searching for COM Surrogate usually need a practical diagnosis: which folder triggers it, whether thumbnails are involved, whether the file path is real, and whether a recent codec or preview tool caused the issue.
FAQ
Can I end COM Surrogate?
Yes, but it is temporary. Explorer may recreate it as soon as thumbnails or previews are needed again.
Is COM Surrogate a virus?
The real dllhost.exe is a Windows component. A fake file with the same name in another folder can be malware, so always check the file path.
Why does it spike when opening videos?
Explorer may be generating thumbnails or reading metadata through codecs. A damaged file or broken codec can keep COM Surrogate busy.


Leave a Comment