Kaspersky Lab specialists discovered a ransomware that is masked as a beta version of Cyberpunk 2077 for Android and was distributed via cyberpunk2077mobile[.]com.
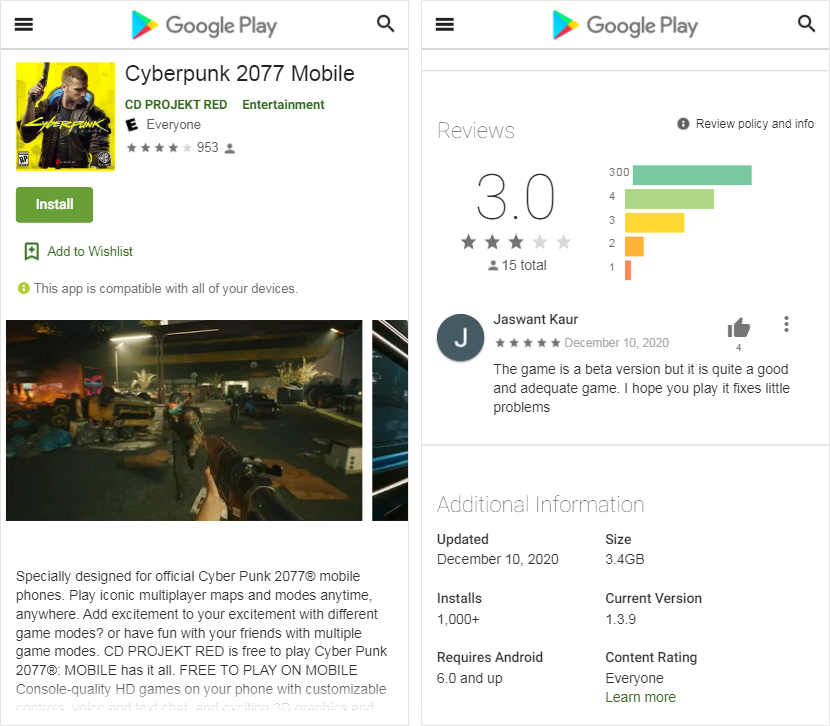
The site of the “mobile version” looked suspiciously like Google Play, and its creators claimed that the beta was released on the day the game was officially released. Allegedly, the “beta” has already been downloaded by about a thousand people, and some of them even left feedback, noting that the game is not bad for the beta version.Although the website states that the application weighs 3.4 GB, when downloading the file, the file does not even reach 3 MB.
When starting the application, first of all, it requires access to files on the device. In theory, the application may need these rights if the user wants to save or open something through it, but the game hardly needs photos and videos to start.
However, the application cannot run without this permission. Nevertheless, even if you give out all the rights to the fake version, you won’t be able to play either: instead of Cyberpunk 2077, the victim will only see a message demanding a ransom.
In a note in broken English, the user is warned that now all his photos and other important files are encrypted.
It is also impossible to get rid of the ransomware, according to the ransomware note: the files allegedly cannot be returned.
The researchers checked what actually happens to the files on the infected device. The threats were not empty: the files were indeed encrypted and assigned the .coderCrypt extension. In addition, the malware placed a README.txt file in each folder with the same note as in the application window.
In this case, the key was hardcoded into the application code. In all the samples that the experts came across, the key was: “21983453453435435738912738921“.
Experts also write that the authors of the fake beta Cyberpunk 2077 for Android are also distributing an encryptor for Windows, masked with the the same game.
The files encrypted by it can no longer be restored on their own, because the key is not hardcoded into the application code, but is randomly generated for each individual infection case. Perhaps this is precisely why they demand twice as much money from PC users as from victims of mobile malware.
Let me remind you that Hackers use PipeMon backdoor to attack game developers.


Leave a Comment