SapphireStealer is a versatile information-stealing malware, emerged in December 2022. Analysts discovered multiple variants since then, which is possible because of its open source code, available on GitHub.
This malware targets corporate credentials, gathering a range of device data, capturing screenshots, and exfiltrating files. Its adaptable nature and potential use by various threat actors make it a concerning cyber threat, capable of facilitating cyber-espionage, ransomware attacks, and other malicious activities through compromised entities.
SapphireStealer Overview
SapphireStealer is an open-source information stealing malware, that was published on GitHub back in December 2022. Further, various versions with distinct capabilities have emerged, suggesting its adoption by multiple threat actors.
Having the code available for anyone opens the gates for infinite modifications to the code. This makes SapphireStealer potentially the most flexible malware, that can be adjusted for every specific attack. Of particular concern is its involvement in attacks aimed at corporate credentials. Such data is often sought by cybercriminals for resale, facilitating cyber-espionage, ransomware, and further assaults against the compromised corporate entities. SapphireStealer underscores the ever-evolving landscape of digital threats and the importance of robust cybersecurity measures.
| Name | SapphireStealer |
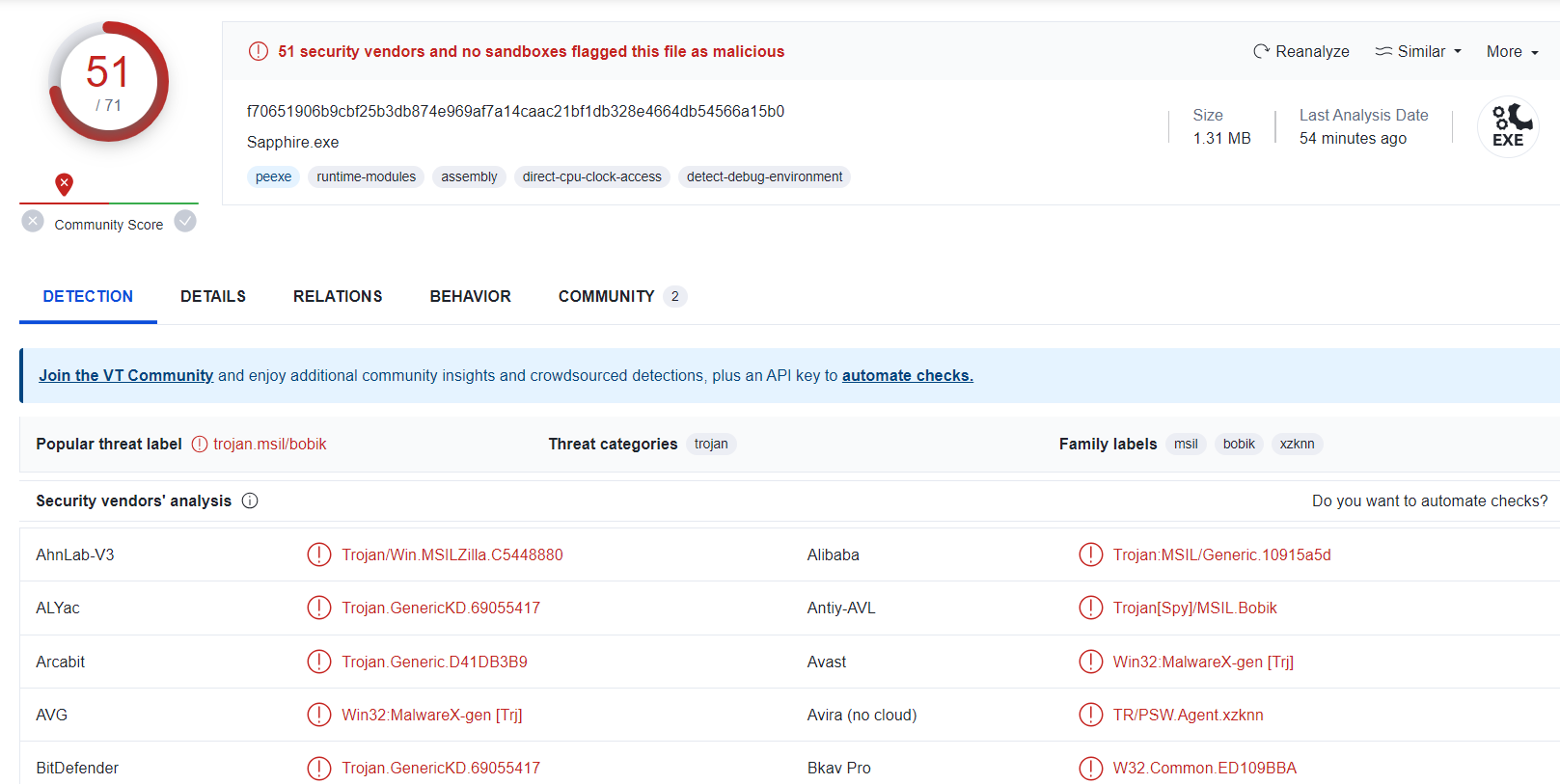
| Detection | Trojan:MSIL/FormBook.CD!MTB |
| Damage | Data stealing, potential malware delivery |
| Similar behavior | S1deload, Luca, StealDeal |
| Fix Tool | See If Your System Has Been Affected by SapphireStealer Virus |
SapphireStealer Infection Stages
The initial stages of SapphireStealer’s infection process can vary among its different versions, with some employing multi-stage approaches. Likewise, these variants differ in their methods of data exfiltration, functionalities, and the scope of targeted information. SapphireStealer initiates by collecting device-specific data, such as device name, CPU architecture, GPU, screen resolution, operating system version, and IP address.
The primary focus of this malware is to target credentials stored within web browsers (full list of browsers targeted). Across its versions, the specific information of interest may vary, but generally includes visited URLs, viewed webpages, search queries, Internet cookies, login credentials (usernames/passwords), and even credit card numbers.
List of browsers targeted by SapphireStealer
- Google Chrome
- Microsoft Edge
- Opera
- Yandex
- Elements
- Epic Privacy Browser
- Kometa
- Orbitum
- CocCoc
- Comodo Dragon
- Torch
- 360 Browser
- Amigo
- Atom Browser
- Brave
- CentBrowser
SapphireStealer also possesses the capability to capture screenshots and terminate running processes. Moreover, it can exfiltrate victims’ files, with some variants targeting a limited set of file types, while others encompass a wide range. For instance, one version collected text files (.txt), Microsoft Office documents (.doc, .docx), PDFs (.pdf), and various image formats (.img, .jpg, .png).
As mentioned earlier, multiple versions of SapphireStealer exist, with the potential for further iterations featuring diverse functionalities. We expect this malware to use a different way of storing collected data, as well as aim at more specific file formats (CAD projects, blueprints, PDF reports, etc.).
How does this malware spread?
Cybercriminals typically employ phishing and social engineering tactics to distribute malware, with commonly used methods including:
- Drive-By Downloads. Deceptive and stealthy downloads that occur without user consent commonly contain unwanted content. More often, you will see unwanted programs installed in such a way. Though, malware does not disdain such a spreading way either.
- Malicious Attachments and Links. Often found in spam emails, private messages and texts, they can deliver malware to the target system in one click. Usually, the message itself tries to force the victim to open the attachment or follow the link.
- Online Scams. Tricking users into downloading malware through fraudulent schemes is an old-timer of malware spreading. Nowadays, it just obtained a new form – hackers reach their victims on phone, pretending to be tech support specialists. They push malware to the victim’s device under the guise of “fix tool” for the problem they made up.
- Malvertising. Malicious advertisements that lead to malware downloads. Existed since online ads exist.
- Untrustworthy Download Sources. Obtaining software from sources like freeware websites, third-party platforms, or Peer-to-Peer networks is risky, as there is no way to make sure that the software package is clear.
- Illegal Program Activation Tools. Using cracks or keygens is illegal itself. However, hackers boost that risk even more by using such applications as shells for malware injection.
- Fake Updates. Downloading updates from unverified sources that can introduce malware. It is especially risky since malware under this disguise can easily request admin privileges.
- Some malicious programs can also spread through local networks and removable storage devices like USB drives.
How to remove SapphireStealer?
Fortunately, flexibility of malware does not equal to its invulnerability to anti-malware software. Programs which feature heuristic protection along with frequent database updates are effective against SapphireStealer. I’d recommend you GridinSoft Anti-Malware as a program that fits both of these requirements.
Remove SapphireStealer with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Stealers as shown from our tests with the software, and we assure you that it can remove SapphireStealer as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “SapphireStealer” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing SapphireStealer and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Frequently Asked Questions (FAQ)
Reformatting your storage device should only be considered as a last resort for removing SapphireStealer malware. Prior to taking such drastic action, it is advisable to perform a comprehensive scan using trustworthy antivirus or anti-malware software.
Malware poses a significant risk to the security and privacy of sensitive information, potentially leading to identity theft, financial loss, and unauthorized access to personal accounts. Furthermore, it can disrupt the normal operation of a system, causing performance issues, system crashes, and data corruption.
The purpose of SapphireStealer is to enable remote access and control of compromised devices. It allows threat actors to perform various malicious activities, such as unauthorized access, data theft, system manipulation, and disabling security measures, potentially causing significant harm to individuals and organizations.
Gridinsoft Anti-Malware has the ability to identify and eliminate most malware infections. Nevertheless, it is crucial to recognize that sophisticated malware can remain hidden deep within the system. Consequently, conducting a complete system scan is imperative to detect and eradicate malware.
How to Remove SapphireStealer Malware
Name: SapphireStealer
Description: SapphireStealer, introduced in December 2022, is a formidable information-stealing malware, manifesting in numerous variants. This insidious threat specializes in pilfering corporate credentials, acquiring diverse device data, taking screenshots, and exfiltrating files. Its adaptability and appeal to multiple threat actors underscore its prominence in facilitating cyber-espionage, ransomware attacks, and other malicious activities through compromised corporate entities. With the potential for continued evolution, SapphireStealer stands as a significant and ever-evolving cybersecurity challenge. Vigilance and robust security measures are essential defenses against this versatile malware.
Operating System: Windows
Application Category: Malware