What is Spyware?
Spyware is a malicious program that aims at collecting information about the target system
In today’s digital age, when we are used to using the Internet to communicate and conduct transactions, cybercrime has taken on alarming proportions. One of the common types of cyber threats is spyware. This malicious software infiltrates a computer system, typically without the user’s knowledge, and collects sensitive information from the device. Spyware can take various forms and shapes, and its primary purpose is to monitor and track the user’s online activities. Typically, the collected data include personal information, browsing history, login credentials, and financial information.
Data collected by spyware
Next, spyware sends this information to cybercriminals, who can use it for malicious purposes. Usually, it is a standard list: identity theft, financial fraud, or blackmail. However, one of the critical differences between spyware and other types of malware is that spyware does not usually cause direct damage to the infected system. Instead, its goal is to covertly gather as much data as possible without being noticed. As a result, it makes detecting and removing challenging them.
Spyware infection methods
Spyware distribution methods are generally similar to those of other malware. It can be installed on a system in various ways, including through infected email, software downloads, or even physical access to the device. Once successfully infected, spyware works in the background, collects data, and sends it to a predetermined attacker server.
Spyware vs. Stealers
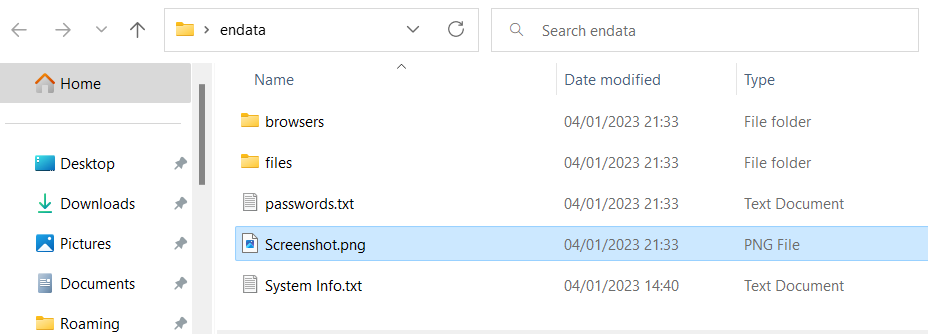
One of the most prevalent types of spyware is a stealer. Stealers is a specific type of spyware that focuses on stealing login credentials for online banking and payment systems. However, stealers differ from spyware because they are designed to steal information rather than monitor user activity. Once installed, they capture passwords, credit card numbers, and other sensitive data that users store or type into their devices. Next, it sends it to the hacker’s server, allowing them to access the victim’s financial accounts.
Keyloggers
Keyloggers are stealers that record every keystroke made on a device . An attacker can install them on a device or through phishing emails, social engineering, or warez content downloads. Once installed, the keylogger collects all entered information, including passwords, credit card details, and other personal information. Attackers use this information to commit identity theft, financial fraud, and other malicious activities.
Spyware and stealers are both dangerous forms of malware that can compromise the security of a user’s computer system. While spyware primarily monitors user activity, stealers are used to stealing sensitive information such as login credentials and financial data. By taking proactive measures to secure their devices, users can protect themselves against these cyber threats and prevent their personal information from falling into the wrong hands.


