A team of five independent researchers spent three months and hundreds of man-hours and discovered 55 vulnerabilities on Apple products. However, the researchers received a reward for this with a scandal. This team included: Sam Curry, Brett Buerhaus, Ben Sadeghipour, Samuel Erb, and Tanner Barnes.
The head of the team, 20-year-old Sam Curry, announced this on the pages of his blog this week.He says that initially, the search for bugs was supposed to be a small side project that the researchers wanted to work on if they had free time.
Soon, the coronavirus pandemic made its own adjustments to these plans, the group had a lot of free time, and as a result, hundreds of man-hours were spent on research. Curry admits that.
As a result, the researchers were able to find 55 different vulnerabilities in Apple’s online services, including 11 critical ones. For example, one of the most serious mistakes allowed an attacker to create a worm that automatically steals all photos, videos, and documents from someone else’s iCloud account, and then doing the same with all of the victim’s contacts. A PoC demo of this attack can be seen below.
Moreover, the researchers write that they could also have access to Apple’s source code repository, “the holy grail,” where the company stores the source code for “hundreds of different applications for iOS and macOS.”
Here are 11 critical bugs found by researchers:
- remote execution of arbitrary code by bypassing authorization and authentication;
- Bypassing authentication using incorrectly configured permissions provides an attacker with global administrator access.
- command injection via an incorrectly cleared file name argument;
- remote execution of arbitrary code through the leak of a secret and a tool left open for administrators;
- a memory leak leading to the compromise of employee and user accounts, as well as opening access to various internal applications;
- SQL injection of Vertica through incorrect cleaning of input;
- Stored XSS with the potential of a worm to completely compromise the victim’s iCloud account;
- SSRF, which allows access to internal sources and protected resources;
- Blind XSS, allowing access to the internal support portal to track customer and employee issues;
- Server-side execution of PhantomJS to access internal AWS IAM resources and keys.
While considering the average cost of vulnerabilities in Apple products, one might think that the researchers hit the big jackpot, in reality things turned out differently. Curry wrote that the company quickly fixed all the discovered bugs, but paid the specialists only $55,100. That is, approximately $250 per vulnerability per person, or $17,171 per month for each researcher.
ViceMotherboard quotes Phobos CEO Dan Tentler as convinced that “it’s incredibly small”:
This view, however, does not share cybersecurity veteran Katie Moussouris. The founder of Luta Security is best known for coordinating bug bounty programs for Microsoft, Symantec and the Pentagon. According to her, the amount of payments could be fair.
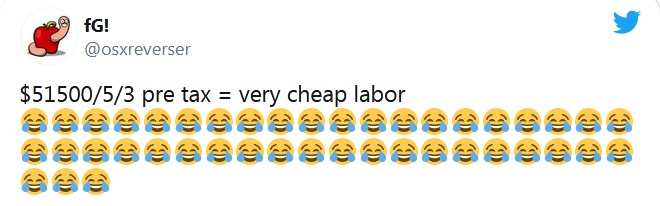
Meanwhile, former Apple employees joked on Twitter that bug bounty is just a way to attract cheap workforce.
I must say that from the beginning Curry emphasized on the blog that, most likely, his team will receive more payments in the coming months. He wrote that fixing 55 bugs and processing all these reports is definitely more difficult than fixing 1-2 vulnerabilities. The researcher complained only that he was upset because of the lack of information about this process, but overall he was pleased with the bug bounty.
Shortly after this story hit the pages of the Western media, Apple representatives reacted to the incident and commented on the situation. Thus, the company once again thanked the researchers for their work, and payments to Curry and his colleagues quickly increased to $288,500, and so far Apple has paid only 32 errors out of 55 found.
Let me remind you that we talked about bluetooth attack BIAS endangers devices with firmware from Apple, and also that recently Apple developers found third-party keyboard vulnerability in iOS.


Leave a Comment