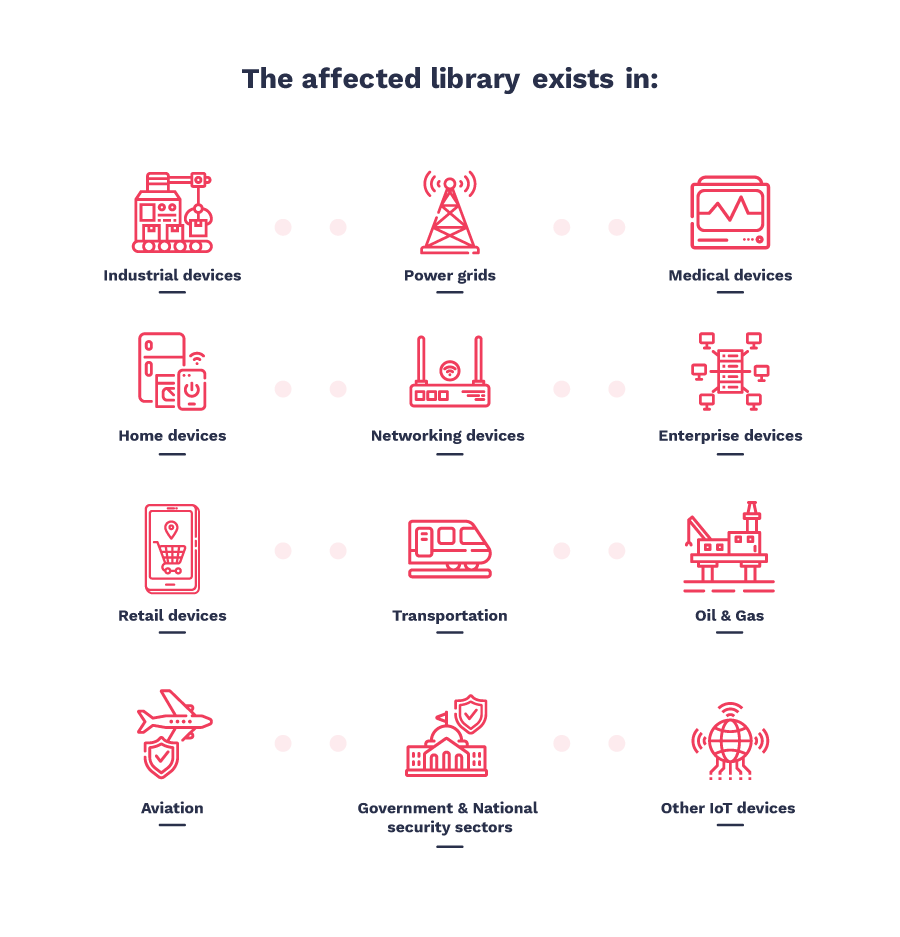
Specialists from the Israeli company JSOF discovered 19 vulnerabilities in a small library that was created back in the 90s and has been actively used in many different products all this time. As a result, hundreds of millions of IoT devices are at risk due to Ripple20 vulnerabilities.
Printers, routers, various solutions for smart homes, power supply, medical and industrial equipment, transportation systems, equipment for mobile and satellite communications, data centers and much, much more became vulnerable.Even worse, vulnerabilities in most products are unlikely to ever be fixed due to complex or opaque software supply chains.
The fact is that the problem library was used not only by equipment suppliers, but also integrated into other software packages, which means that many companies do not even know that they use this specific code, since the library is often not mentioned at all in the manifest”, — according to JSOF researchers.
The problems found by experts were overall called Ripple20 and were found in a small library developed by Treck. Released back in 1997, this library is a lightweight implementation of the TCP/IP stack. Companies have been using this solution for decades so their devices or software can connect to the Internet via TCP/IP.
JSOF experts decided to study the Treck stack due to its massive presence in the market of industrial, medical and smart devices. As a result, as was said above, were discovered 19 different vulnerabilities, and the JSOF has been working with CERT representatives for many months to fix them.
Treck representatives, who first decided that they were dealing with fraudsters and ransomware, realized their mistake and also got involved. Currently, patches are available for all vulnerabilities in Ripple20. However, unfortunately the work to identify all vulnerable devices is still far from complete”, – write JSOF analysts.
Fortunately, not all Ripple20 vulnerabilities are critical, although some of them are still very dangerous and allow attackers remotely take control of vulnerable systems.
Thus, the US Department of Homeland Security assigned a rating of 10 and 9.8 on a ten-point scale CVSSv3 to four Ripple 20 vulnerabilities:
- CVE-2020-11896 (CVSSv3 – 10): allows remote execution of arbitrary code;
- CVE-2020-11897 (CVSSv3 – 10): allows out-of-bounds recording;
- CVE-2020-11898 (CVSSv3 – 9.8): may lead to the disclosure of confidential information;
- CVE-2020-11899 (CVSSv3 – 9.8): may lead to the disclosure of confidential information.
Four of these issues can allow attackers easily take control over smart devices or industrial and medical equipment. Attacks are possible both through the Internet and from local networks. Demonstration of the attack can be seen in the video below.
Researchers believe that the upcoming impact of Ripple20 problems can be compared with another “set” of vulnerabilities, Urgent/11, information about which was released in the summer of 2019. Those problems are still being studied, and experts are constantly discovering more and more problematic devices.
This comparison is not accidental, since Urgent/11 vulnerabilities relate to the TCP/IP stack (IPnet), which is used in the VxWorks real-time operating system (RTOS), as well as OSE from ENEA, INTEGRITY from Green Hills, Microsoft ThreadX, ITRON from TRON Forum , Mentor Nucleus RTOS and ZebOS.
As in the case of Urgent/11, some products will obviously remain without fixes for Ripple20, since many of them are already outdated, and vendors have stopped working.
US-CERT, CERT/CC, and Treck also published bug reports on Ripple20. Mitigation recommendations are already available on GitHub.
READ ALSO: Our recent item on devices’ default passwords and basic rules of IoT security.