Bleeping Computer reported that Clop ransomware operators leaked stolen data from two universities: Colorado and Miami.
In particular, screenshots of student progress and social security numbers, University of Colorado financial records, student enrollment and biographical information, medical records, demographic records, and a spreadsheet with email addresses and phone numbers of University of Miami students have been posted on the site.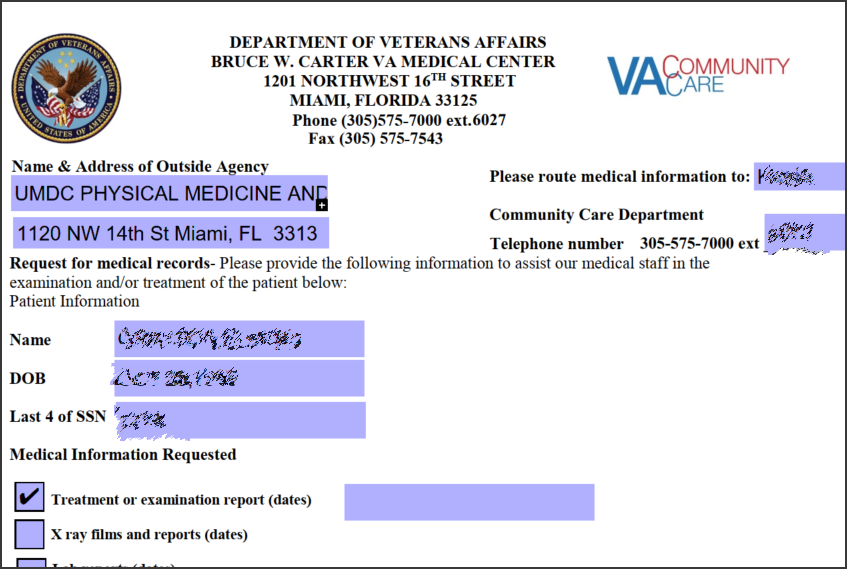
Attacks on educational institutions were associated with the use of the outdated file-sharing solution Accellion FTA (File Transfer Application). We have already written about this problem many times: last month, information security specialists linked attacks on vulnerable Accellion FTA installations with the FIN11 hack group. The company’s analysts wrote that more than 100 companies had fallen victim to cybercriminals at that time.
According to the Accellion developers, among about 300 FTA clients, “less than 100” were victims of attacks, and among them less than 25 were affected by data theft. FireEye clarified that some of these 25 clients are being blackmailed, and hackers are demanding a ransom from them.
As part of this campaign, hackers exploit four vulnerabilities in the FTA (CVE-2021-27101, CVE-2021-27102, CVE-2021-27103, CVE-2021-27104) and then install the DEWMODE web shell and use it to steal files stored on victims’ FTA devices. After that, attackers often blackmail the victims, demanding a ransom and threatening to leak the stolen information into the public domain.
It is noteworthy that the stolen data is published on a website owned by the operators of the Clop ransomware, but not a single machine has been encrypted in the networks of the affected companies and institutions. That is, they all became victims of hacking and classic extortion, not ransomware attacks.
Let me remind you that other victims include: the Reserve Bank of New Zealand, the Australian Securities and Investments Commission (ASIC), the Kroger retail chain, Singapore’s largest telecommunications company Singtel, the oil and gas giant Shell, the information security company Qualys and many others.
Back in February, representatives from the University of Colorado confirmed that the university was affected by a cyberattack through the Accellion FTA.
While the University of Miami had previously reported no attacks or data breaches, the institution used a file-sharing service called SecureSend that recently shut down. Based on the URLs found by Bleeping Computer, this service was also powered by the Accellion FTA.
University officials told reporters that they were already investigating the incident, notified law enforcement and “hired leading cybersecurity experts to assist in the investigation.” To date, an investigation has shown that the attack was limited to the Accellion server, but did not affect other systems at the university.
Let me remind you that The Clop ransomware attacked the German Software AG company.

