In the summer of 2020, researcher Sreeram K.L. earned $ 3133.70 as a bug bounty after finding a bug in Google Docs.
The point is that a vulnerability in Google’s feedback tool could be used to steal sensitive information.Many Google products (including Google Docs) are equipped with Send feedback and Help Docs improve features, which allow users to submit feedback, as well as attach screenshots to demonstrate a specific issue they encountered.
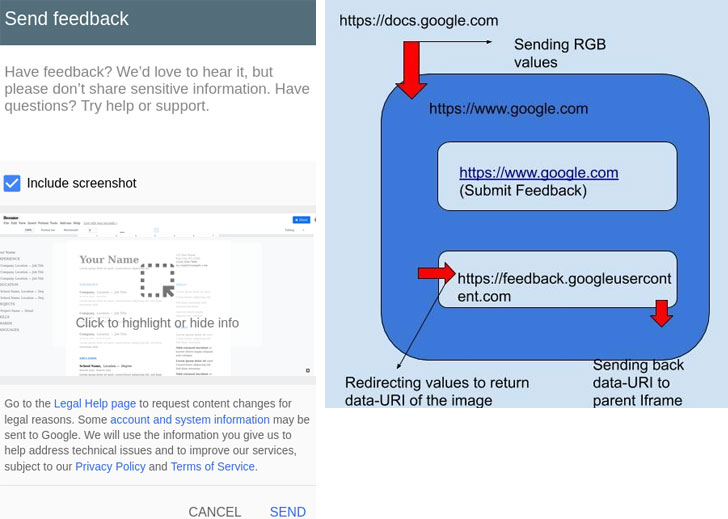
These features are not duplicated across services, instead the feedback is deployed around the main Google site (google.com) and integrated elsewhere through an iframe that loads the popup content from feedback.googleusercontent.com.
The researcher found a bug in the way these messages are sent to feedback.googleusercontent.com.
The bug made it possible to make changes to the frame, directing content to an arbitrary external site, steal or intercept screenshots intended for uploading to Google servers. The problem was related to the missing X-Frame-Options header in the Google Docs domain.
A demonstration of the attack can be seen below.
The attack required some interaction with the user (for example, clicking the “Send feedback” button), then the exploit could exploit the vulnerability, intercept the URL of the uploaded screenshot and transmit it to a malicious site.
The expert says the attack could have been carried out by embedding a Google Docs file in an iFrame on a malicious site, then intercepting the feedback pop-up and redirecting its contents to the attacker’s chosen domain.
Let me remind you the Thousands of Google Calendars Disclose Confidential Information.


Leave a Comment