The US government said that from January 2020 to February 2022, Russian government hackers regularly attacked and compromised several of the country’s defense contractors.
A joint official statement was issued by representatives of the NSA, CISA and the FBI. The document says: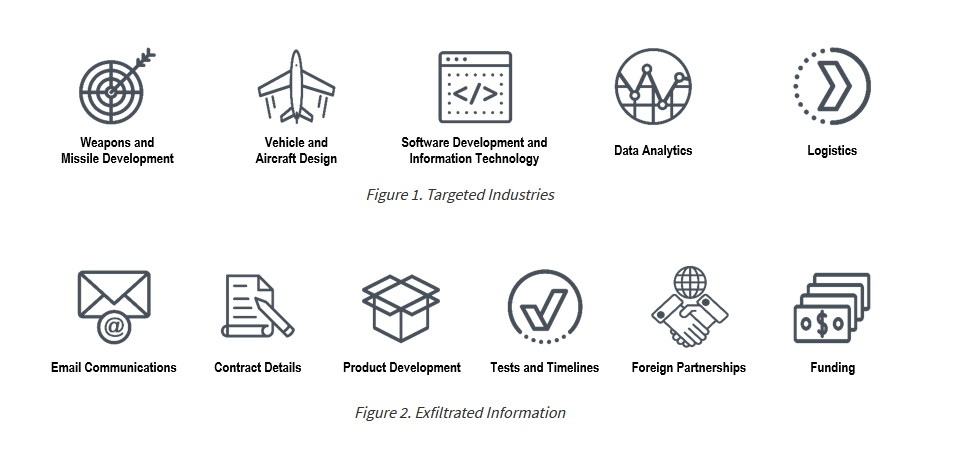
The hackers reportedly relied on “common but effective” hacking tactics in their attacks, including spear-phishing, credential pre-harvesting, brute force, password spraying, and exploiting known vulnerabilities. For example, the attackers used the following bugs:
- CVE-2018-13379 (CVSS 9.8) – Path traversal vulnerability in Fortinet FortiGate SSL VPN.
- CVE-2020-0688 (CVSS 8.8) – RCE vulnerability in Microsoft Exchange.
- CVE-2020-17144 (CVSS 8.4 points) – RCE vulnerability in Microsoft Exchange.
In the case of a successful compromise, the attackers stole emails and confidential (unclassified) data, including proprietary and export-controlled information.
It is emphasized that the theft of this information provided the attackers with very detailed, albeit unclassified, information about the timing of the development and deployment of US weapons platforms, the technical characteristics of vehicles, and plans in the field of communication infrastructure and information technology.
Actions to Help Protect Against Russian State-Sponsored Malicious Cyber Activity:
- Enforce multifactor authentication.
- Enforce strong, unique passwords.
- Enable M365 Unified Audit Logs.
- Implement endpoint detection and response tools.
You may also be interested in the following information: Microsoft: Russian hackers attack anti-doping organizations, and Russian hackers tried to steal COVID-19 research data.


Leave a Comment