The Rajah virus belongs to the Makop ransomware family. Ransomware of such sort encrypts all the data on your computer (photos, text files, excel sheets, music, videos, etc) and appends its own extension to every file, creating the +README-WARNING+.txt text files in each directory with the encrypted files.
Rajah virus: what is known so far?
☝️ A strictly correct denomination for the Rajah is “a Makop family ransomware infection”.
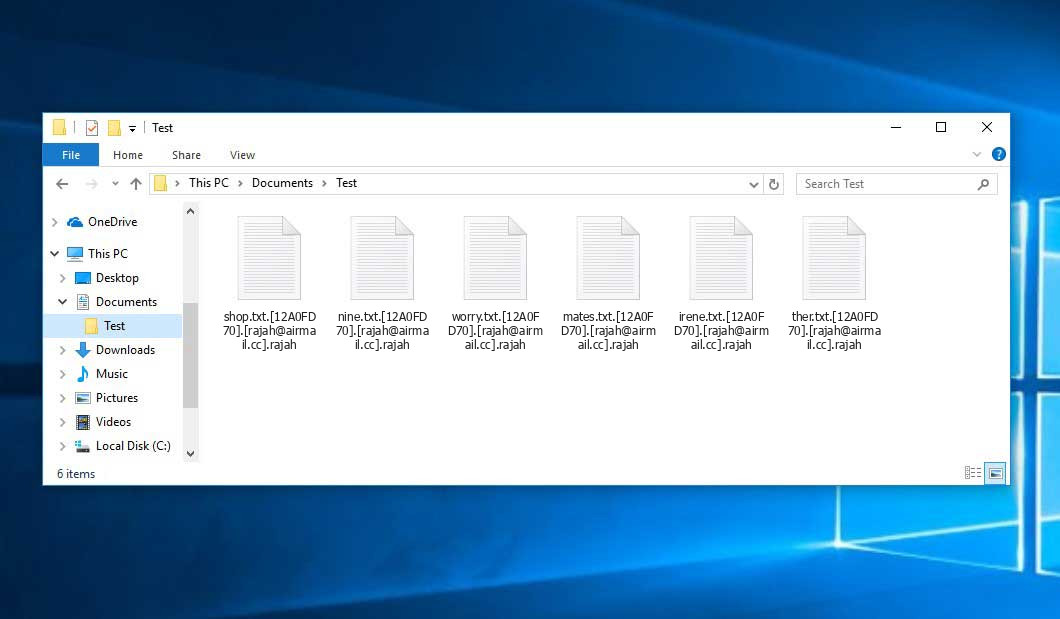
The renaming will be done by the following pattern: .rajah. In the process of encryption, a file named, for instance, “report.docx” will be turned into “report.docx.[12A0FD70].[[email protected]].rajah”.
In each directory that contains the encoded files, a +README-WARNING+.txt text file will be found. It is a ransom money memo. Therein you can find information about the ways of contacting the racketeers and some other remarks. The ransom note most probably contains a description of how to purchase the decryption tool from the ransomware developers. You can obtain this tool after contacting [email protected] by email. That is basically the scheme of the malefaction.
Rajah Overview:
| Name | Rajah Virus |
| Ransomware family1 | Makop ransomware |
| Extension | .rajah |
| Ransomware note | +README-WARNING+.txt |
| Contact | [email protected] |
| Detection | Trojan.Win32.VB, Win32/Adware_AGen.G, Win32/Sality.NDH |
| Symptoms | Your files (photos, videos, documents) get a .rajah extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Rajah virus |
The +README-WARNING+.txt document coming in package with the Rajah malware provides the following frustrating information:
XXX Your data has been encrypted XXX To restore your data, write to [email protected] PLEASE READ THE TEXT BELOW VERY CAREFULLY!!! 1. No one will return your data except us (do not trust third parties) 2. Antivirus and recovery programs will permanently corrupt your data (Even we can't restore it to you!) 3. Payment for the recovery of your data is made in BITCOIN (BTC) !!! BITCOIN ONLY!!! 4. You can buy BITCOIN (BTC) on the website hxxps://www.binance.com/en (Pass a simple registration following the instructions on the site and then purchase BITCOIN (BTC) If you have read the text above and you need your data, it's time to write to us
In the screenshot below, you can see what a directory with files encrypted by the Rajah looks like. Each filename has the “.rajah” extension appended to it.
How did my PC catch Rajah ransomware?
There are many possible ways of ransomware infiltration.
There are currently three most exploited ways for evil-doers to have ransomware planted in your system. These are email spam, Trojan injection and peer file transfer.
If you open your mailbox and see letters that look like familiar notifications from utility services providers, delivery agencies like FedEx, web-access providers, and whatnot, but whose mailer is strange to you, beware of opening those emails. They are very likely to have a harmful item enclosed in them. So it is even more dangerous to open any attachments that come with letters like these.
Another option for ransom hunters is a Trojan file model. A Trojan is an object that infiltrates into your computer disguised as something legal. For example, you download an installer for some program you need or an update for some program. However, what is unpacked turns out to be a harmful agent that compromises your data. Since the installation wizard can have any name and any icon, you have to make sure that you can trust the source of the files you’re downloading. The optimal way is to use the software developers’ official websites.
As for the peer file transfer protocols like torrents or eMule, the danger is that they are even more trust-based than the rest of the Internet. You can never guess what you download until you get it. So you’d better be using trustworthy resources. Also, it is reasonable to scan the folder containing the downloaded objects with the antivirus as soon as the downloading is complete.
How do I get rid of the Rajah virus?
It is crucial to note that besides encrypting your data, the Rajah virus will probably install Vidar Stealer on your machine to get access to credentials to different accounts (including cryptocurrency wallets). The mentioned program can extract your credentials from your browser’s auto-filling cardfile.
Often tamperers would unblock few of your files to prove that they indeed have the decryption tool. Since Rajah virus is a relatively new ransomware, security software engineers have not yet found a method to undo its work. Nevertheless, the decoding instruments are constantly updated, so the solution may soon arrive.
Sure thing, if the criminals do the job of encoding victim’s essential files, the desperate person will probably fulfill their demands. Nevertheless, paying to criminals does not necessarily mean that you’re getting your blocked information back. It is still risky. After receiving the money, the racketeers may send a wrong decryption key to the victim. There were reports of hackers simply disappearing after getting the money without even bothering to reply.
The optimal countermeasure to ransomware is to have aan OS restore point or the copies of your essential files in the cloud drive or at least on an external disk. Obviously, that might be not enough. Your most crucial thing could be that one you were working on when it all happened. But at least it is something. It is also wise to scan your PC for viruses with the anti-malware utility after the OS is rolled back.
There are other ransomware products, besides Rajah, that work similarly. Examples of those are Agpo, Tgvv, Bhgr, and some others. The two main differences between them and the Rajah are the ransom amount and the encoding method. The rest is the same: documents become blocked, their extensions changed, ransom notes are found in each directory containing encrypted files.
Some fortunate victims were able to decrypt the arrested files with the help of the free tools provided by anti-malware developers. Sometimes the hackers accidentally send the decryption code to the wronged in the ransom readme. Such an extraordinary fail allows the user to restore the files. But obviously, one should never expect such a chance. Make no mistake, ransomware is a tamperers’ tool to lay their hands on the money of their victims.
How to avert ransomware attack?
Rajah ransomware doesn’t have a superpower, neither does any similar malware.
You can protect your computer from its attack in several easy steps:
- Ignore any emails from unknown mailers with strange addresses, or with content that has likely no connection to something you are expecting (how can you win in a lottery without even taking part in it?). If the email subject is likely something you are expecting, check all elements of the dubious email with caution. A hoax letter will always have a mistake.
- Never use cracked or untrusted software. Trojans are often distributed as a part of cracked products, most likely as a “patch” to prevent the license check. But untrusted programs are difficult to tell from trustworthy ones, because trojans may also have the functionality you need. Try searching for information on this software product on the anti-malware forums, but the best solution is not to use such programs at all.
FAQ
🤔 Is it possible to open “.rajah” files?
There’s no way to do it, unless the files “.rajah” files are decrypted.
🤔 What should I do to make my files accessible as fast as possible?
If the “.rajah” files contain some really important information, then you probably have them backed up. In case you haven’t, there is still a chance that you do have a Restore Point from some time ago to roll back the whole system to the moment when it had no virus yet, but already had your files. All other solutions require time.


Leave a Comment