The Nerz virus belongs to the STOP/DJVU family of ransomware-type infections. This virus employs a robust encryption method to encrypt various file types (videos, photos, documents), which the “.nerz” extension can identify. The encryption used by this virus is so strong that it is practically impossible to calculate the decryption key.
I have compiled a comprehensive list of all the possible solutions, techniques, and strategies to counter the Nerz virus and recover encrypted files. Depending on the circumstances, restoring your files may be relatively easy or complicated.
📌 It is important!
The ransom payment does not assure you of getting your files back. The cybercriminals responsible for the Nerz virus are notoriously untrustworthy. There are instances when they have failed to supply the decryption key even after receiving the ransom.
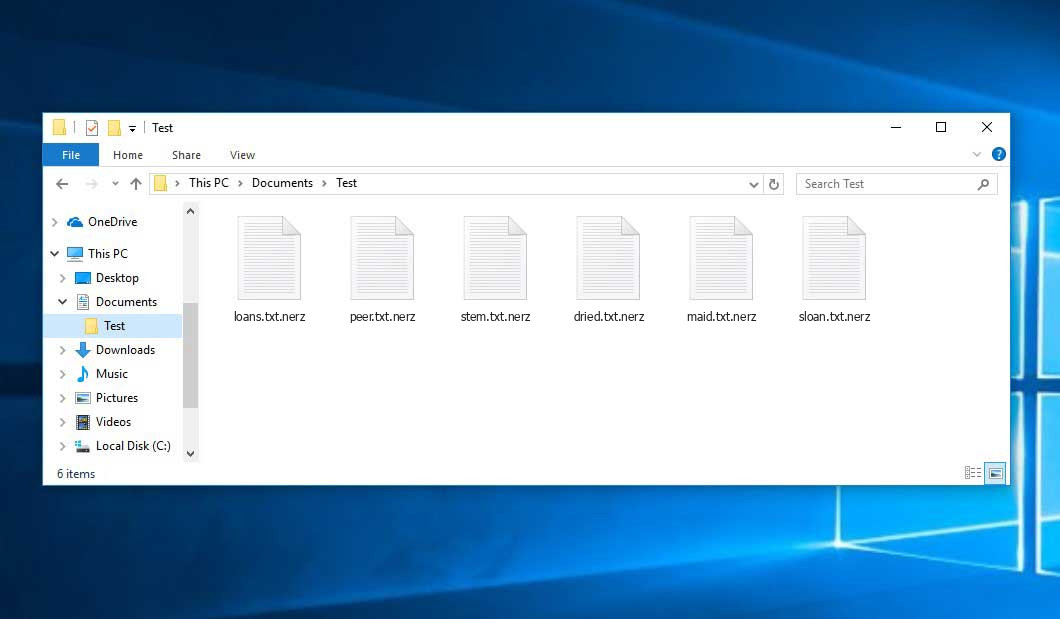
When the Nerz virus infects a computer’s operating system and initiates the file encryption process, it appends the “.nerz” extension to the encrypted files. The virus demands a ransom payment in exchange for a decryption code to regain access to the encrypted files. Typically, the ransom instructions are provided through a text file named “_readme.txt”.
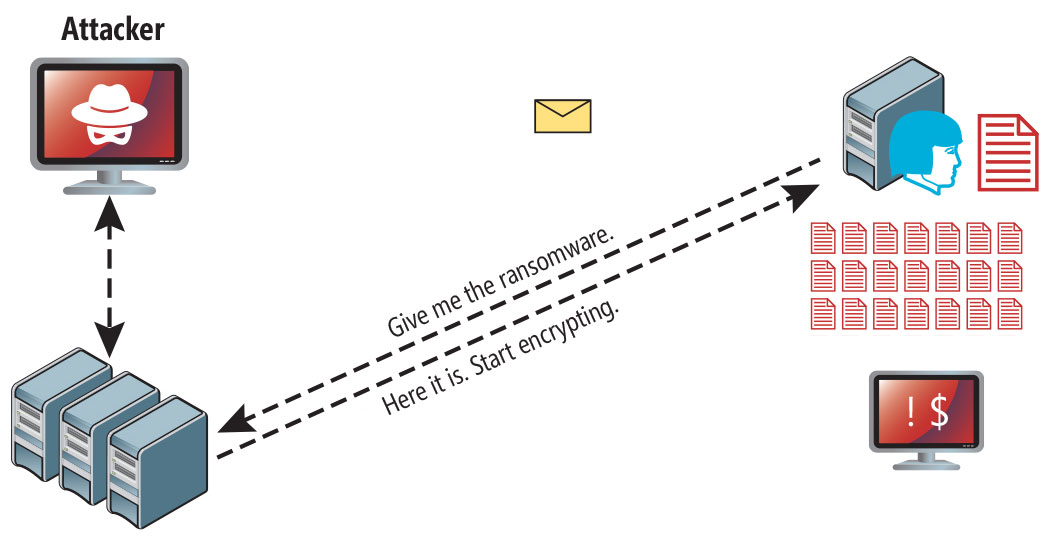
Each victim of the Nerz virus is assigned a unique decryption key, with one exception:
- If the Nerz virus fails to connect with its command and control servers (C&C Server) before initiating the encryption process, it utilizes an offline key. This offline key is the same for all victims, allowing for the decryption of files affected by the ransomware.
Is Nerz virus?
☝️ Nerz can be correctly identified as a STOP/DJVU ransomware infection.
Nerz
🤔 Nerz virus is ransomware that originates from the DJVU/STOP family. Its primary purpose is to encrypt files that are important to you. After that ransomware virus asks its victims for a ransom fee ($490 – $980) in BitCoin.
The Nerz ransomware belongs to the STOP/DJVU family of ransomware-type infections. It encrypts various file types, such as documents, photos, and videos, and appends the “.nerz” extension to them. The encryption method employed by the virus is robust, making it virtually impossible to decrypt the files without the decryption key.
Like other members of the DJVU ransomware family, such as Neon, Weqp, and Weon, Nerz encrypts files and adds its distinctive “.nerz” extension to each file. For example, a file named “1.jpg” will be renamed to “1.jpg.nerz“. Once the encryption process is complete, the ransomware creates a specific text file named “_readme.txt” and places it in all folders containing the encrypted files.
The image below gives a clear vision of how the files with “.nerz” extension look like:
| Name | Nerz Virus |
| Ransomware family1 | DJVU/STOP2 ransomware |
| Extension | .nerz |
| Ransomware note | _readme.txt |
| Ransom | From $490 to $980 (in Bitcoins) |
| Contact | [email protected], [email protected] |
| Detection | Trojan:Win32/Redline!ic, Trojan:Win32/Vindor!pz, Trojan:Win32/Vindor!pz |
| Symptoms |
|
| Fix Tool |
To remove possible malware infections, scan your PC:
6-day free trial available. |
This _readme.txt file asking payment is for get files back via decryption key:
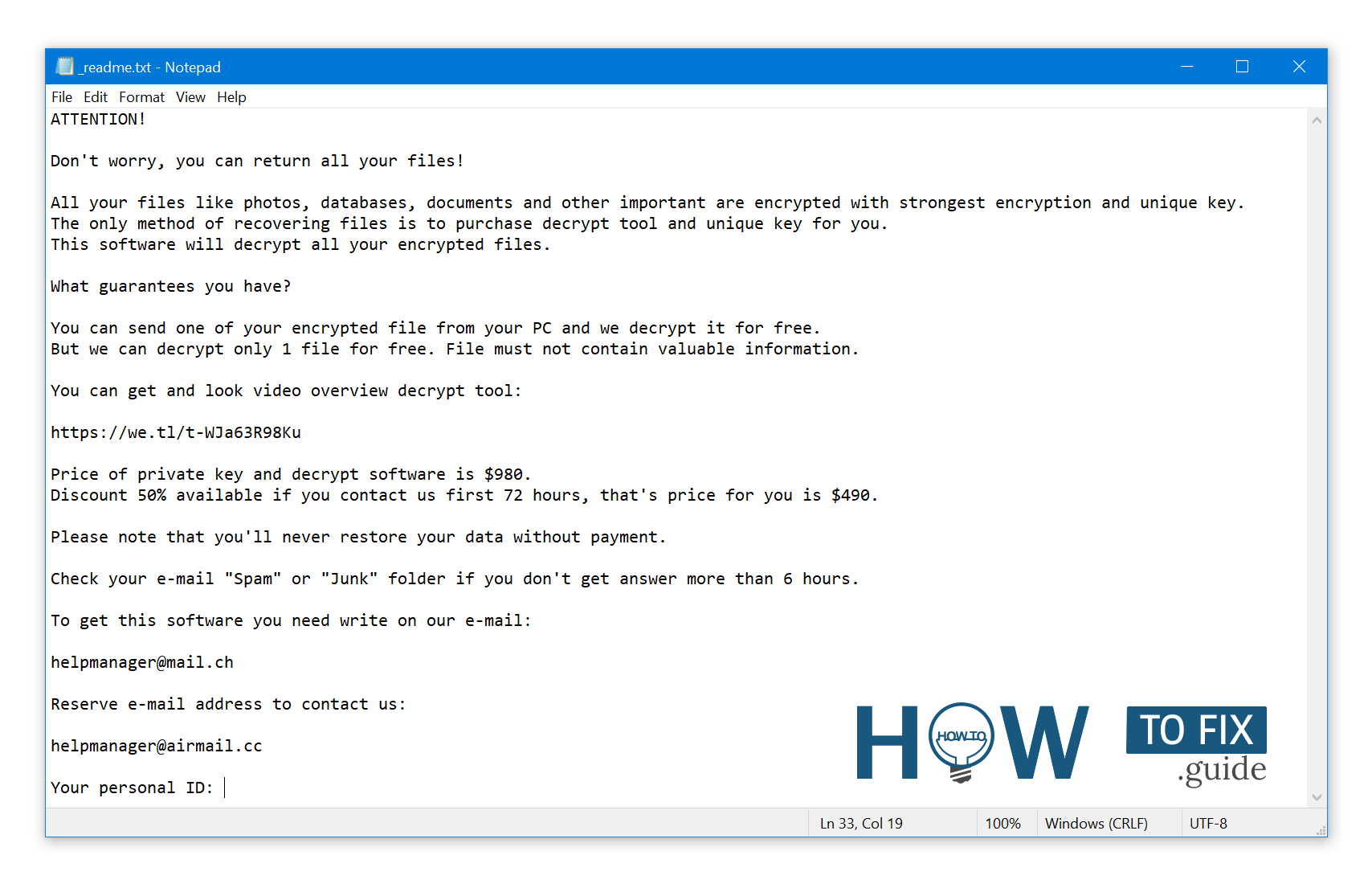
_readme.txt (STOP/DJVU Ransomware) – The scary alert demanding from users to pay the ransom to decrypt the encoded data contains these frustrating warnings
The Nerz ransomware employs several processes to carry out malicious activities on an infected computer. One of the initial processes launched is winupdate.exe, which displays a deceptive Windows update prompt during the attack. This is designed to mislead the victim into believing that a legitimate Windows update causes a sudden system slowdown. However, concurrently, the ransomware initiates another process, typically named with four random characters, which scans the system for targeted files and encrypts them.
Furthermore, the ransomware takes steps to hinder the victim’s ability to restore their computer to a previous state using System Restore Points. It accomplishes this by deleting Volume Shadow Copies from the system using the following CMD command:
vssadmin.exe Delete Shadows /All /Quiet
Once the Volume Shadow Copies are deleted, utilizing them for file restoration becomes impossible. Ransomware operators aim to eliminate Windows OS-based methods that could potentially aid victims in restoring their files free of charge.
The crooks also modify the Windows HOSTS file by adding a list of domains and mapping them to the localhost IP. This alteration results in the victim encountering a DNS_PROBE_FINISHED_NXDOMAIN error when attempting to access any blocked websites.
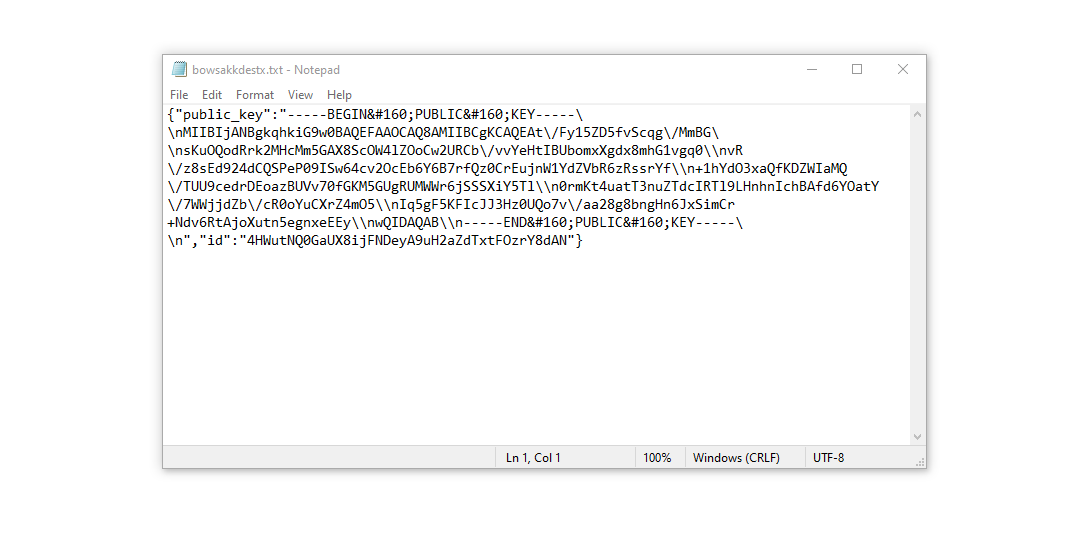
It has been observed that ransomware attempts to block websites that provide various how-to guides for computer users. By restricting access to specific domains, the attackers aim to hinder victims from accessing relevant and helpful information regarding ransomware attacks online. The ransomware also saves two text files on the victim’s computer that contain crucial details related to the attack: the victim’s public encryption key and personal ID. These files are named bowsakkdestx.txt and PersonalID.txt.
After all these modifications, the malware doesn’t stop. Variants of STOP/DJVU tend to drop Vidar password-stealing Trojans on compromised systems. This threat has a lengthy list of capabilities, such as:
- Stealing Steam, Telegram, Skype login/password
- Stealing cryptocurrency wallets
- Downloading malware to the computer and running it
- Stealing browser cookies, saved passwords, browsing history, and more
- Viewing and manipulating files on the victim’s computer
- Allowing hackers to perform other tasks on the victim’s computer remotely
In the case of DJVU/STOP ransomware, including the Nerz variant, the encryption algorithm used is AES-256. Each victim’s files are encrypted with a unique online decryption key, making it impossible to decrypt them without that key.
If Nerz ransomware operated in online mode, you can’t obtain the AES-256 key as it is stored on a remote server controlled by the criminals behind the ransomware.
To receive the decryption key, the ransom amount requested is $980. The victims are instructed to contact the fraudsters via email at [email protected] to obtain payment details.
The message by the ransomware states the following information:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-WJa63R98Ku Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: [email protected] Reserve e-mail address to contact us: [email protected] Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
Do not pay for Nerz!
Please, try to use the available backups, or Decrypter tool
The “_readme.txt” file also states that computer owners should contact the representatives of Nerz within 72 hours from the moment their files are encrypted. If they reach out within this timeframe, they will be granted a 50% rebate, reducing the ransom amount to $490. However, it is strongly recommended not to contact these criminals and refrain from paying the ransom.
I highly advise against contacting criminals and making payments. One of the most effective solutions to recover lost data is using available backups or a Decrypter tool specifically designed for this purpose.
It is worth noting that ransomware viruses, including Nerz, follow a similar pattern in generating unique decryption keys for data recovery. Unless the ransomware has severe flaws or is still in development, manually recovering the encrypted data is impossible. Regularly creating backups of your important files is the best preventive measure to avoid data loss.
When maintaining backups, storing them in a separate location that is not connected to your main workstation is essential. This can be a USB flash drive, an external hard drive, or an online (cloud) storage service. Storing the backup data on your main device is not advisable, as it can also be targeted and encrypted by ransomware.
How I was infected?
Ransomware has various methods to build into your system. But it doesn’t matter what concrete method was used in your case.
Nerz attack following a successful phishing attempt.
Nevertheless, these are common methods through which Nerz ransomware may be injected into your PC:
- Hidden installation and other apps, especially utilities offered as freeware or shareware.
- Clicking on dubious links in spam emails leads to the installation of the virus.
- Downloading files from online free hosting resources that may contain ransomware.
- Using illegal peer-to-peer (P2P) resources to download pirated software, which can be bundled with the ransomware.
It is crucial to exercise caution and maintain a strong security posture to prevent the infiltration of such malware.
There were cases when the Nerz virus was disguised as some legitimate tool, for example, in the messages demanding to initiate some unwanted software or browser updates. This is typically the way how some online frauds aim to force you into installing the Nerz ransomware manually by actually making you directly participate in this process.
Surely, the bogus update alert will not indicate that you will inject the virus. This installation will be concealed under some alert mentioning that you allegedly should update Adobe Flash Player or some other dubious program.
the use of cracked apps poses significant risks. Engaging in illegal activities such as P2P file sharing not only violates laws but also exposes your device to serious malware threats, including the Nerz ransomware.
here are some steps you can take to minimize the risk of Nerz ransomware infecting your device. While there is no foolproof method to guarantee absolute protection, these tips can help enhance your security:
- Exercise caution when installing free software and carefully review what additional offers or bundled programs are included.
- Avoid opening suspicious email attachments and refrain from opening files sent by unknown senders.
- Ensure that your security software is always up to date.
- Be aware that malware often disguises itself and may run in the background without appearing in the list of installed programs.
By following these practices, you can reduce the risk of malware infections, including the Nerz ransomware.
How To Remove Nerz Virus?
In addition to encode a victim’s files, the Nerz virus has also started to install the Vidar Stealer on PC to steal account credentials, cryptocurrency wallets, desktop files, and more.3
Reasons why I would recommend GridinSoft4
-
Run the setup file.


-
Press “Install” button.

-
Once installed, Anti-Malware will automatically run.

-
Wait for complete.

-
Click on “Clean Now”.



it works when you remove neqp file extension