Ransomware was a real curse of 2020, and the same trend continues in 2021. This kind of malware became enormously widespread, and the ways of its distribution became more and more sly. Even large companies with properly created network security may be under attack. However, despite the fact of attacks on corporations, ransomware injection cases are often kept unreported. Local authorities, that are called to investigate cybercrimes, get information about happened attacks from the mass media, instead of getting the reports directly from the victims. In this article, you will see a detailed guide for reporting the ransomware attack case, as well as the reasons why victims avoid doing it.
Why do you keep silent?
The reasons for giving no disclosure to the fact of a malware attack are different for people and corporations. The last ones prefer to be quiet because declaring the fact that your company was successfully attacked by ransomware means declaring that the corporation has a very low cybersecurity level. This fact will surely sink your position among other companies, especially if we talk about the public corporations (i.e. which have their shares in a free float on the stock market). Another reason for companies to avoid the sharing of such information is the possibility of being attacked by other malware. One more problem is that after reporting the ransomware attack, the company may be checked by the police to ensure the fact of cybercrime. And the fact of making use of unlicensed software may disclose right during such a check1.

The price of Ferrexpo plc (FXPO.L) shares plunged after the Petya ransomware attack in March, 2016.
Individuals can tell a much wider range of possible reasons to keep silent because possible consequences differ depending on the country. In Eastern Europe, people don’t want to report the ransomware attack to cyber police, because they are sure that the last ones are useless, so contacting them is just wasting their time. In other countries, victims often think that their report will bring no useful information for local authorities, i.e. they already know the facts that may be disclosed by the victim. Finally, individuals are also afraid that their PC may be checked for unlicensed software usage, so the victim will turn into a criminal.
Popular delusions
In some cases, both individuals and corporations think that the cybercriminals are so powerful that they will get informed about the fact that you have reported the attack, and will make things worse, for example, delete the files, or ruin the whole computer network. On the other hand, there are also a lot of cases when both people and companies do not report the fact of being attacked, thinking that there is no reason to do it and that they will deal with the problem without external help. And while other reasons for corporations can be understood, the reasons why individuals are not reporting the ransomware cases are very disputable.
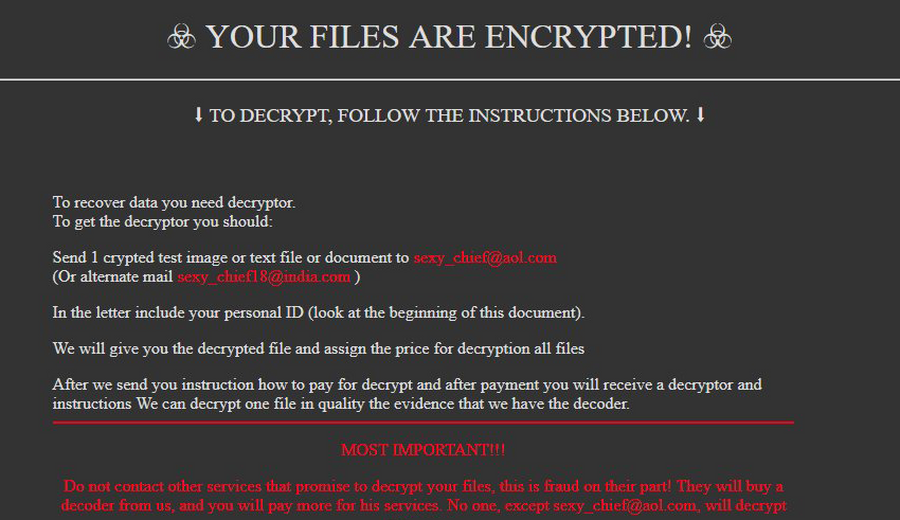
The example of misinformation in ransomware note.
Cyber police, or any other authority that investigates cybercrimes, will be very pleased to get one more piece of information. Every ransomware attack is unique, so the more information these authorities will get – the easier it will be to complete the jigsaw and catch the ransomware distributors. The last action usually results in obtaining the decryption keys for all victims.
Ransomware may steal your data
I have mentioned that a lot of victims (both companies and individuals) are underestimating the possible hazard, thinking that they can deal with the problem without help from authorities. Ransomware developers likely decided to put these self-confident characters down and started to distribute ransomware together with spyware.
Spyware is a type of virus that steals different sorts of data from your computer. Passwords, logins, banking app credentials, personal information, private conversations, corporate documents that are about to be kept away even from the personnel of this company – all these things are not private anymore. The first case when a ransomware attack was combined with a data leak happened a year ago, in January 2020. Maze ransomware developers asked for a separate ransom to be paid to delete the information they stole. Later, the private information of the victims that ignored this offer was published on the website in darknet2. Do you still think that it is a good idea to deal with this problem independently?
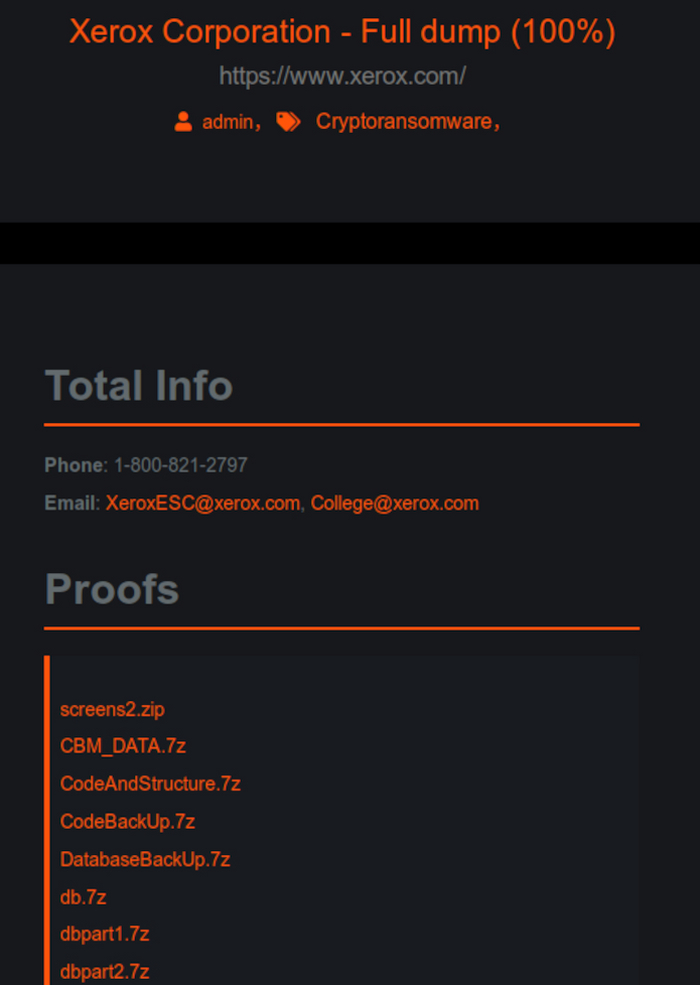
Private data of Xerox Corporation was published in the darknet after Maze ransomware attack
Several words about Maze ransomware. A lot of signs indicate that this ransomware family has Russian origins. There are no reported cases of this virus in Russia, Maze activity spikes at the moment when European/American governments start any actions against Russia or Russian international projects, like Nord Stream-2. And Russian authorities make no actions to counteract the ransomware distribution as it did to other malware distributors, which were disclosed as Russian cyber burglar groups.
How to report the ransomware attack case properly?
As it was mentioned several times, you need to contact your local authorities. But not every police department will fit. You need to check which one is employed in cyber crimes investigations and have the cyber safety experts which will surely make the right conclusions. The report filing for individuals is different compared to ones done by the attacked companies. Here is the list of documents/information that is needed for filling the report:
- Date and time of attack (at least approximated if you haven’t met the exact moment);
- Way of ransomware injection – email spamming, RDP vulnerability exploiting, network vulnerability exploiting, et cetera;
- Copy of money ransom note (a.k.a. readme.txt), or copy of email that was sent by ransomware distributors after contacting the specified email address;
- Extension that is added by ransomware to your files;
- Email addresses that is supposed to be used for getting information about the file decryption;
- Bitcoin wallet address that is supposed to be used to get the ransom;
- The amount of ransom to be paid;
- Name of your organization, its size and contact information;
- Total loss your company carried because of ransomware attack.
Where can I report the ransomware attack?
Here are the websites of authorities of different countries which are responsible for cyber crimes investigation:
Polizia di Stato – Italia
Cybercrime Project – Japan
Policija – Latvia
ePolicija – Lithuania
Police – Luxembourg
Pulizija – Malta
Politie – Netherlands
Police – New Zealand
Rendőrség – Hungary
Hong Kong Police – Hong Kong
Hellenic Police – Greece
Polizei – Germany
Poliisi – Finland
Ministère de l’Intérieur – France
Action Fraud – Great Britain
Politi – Denmark
Policie – Czech Respublic
Cyber Crime Police – Cyprus
Ministy of Internal Affairs – Russia
Ministry of the Interior – Croatia
Garda Síochána – Ireland
Cyber Crime Cell – India
Cyber Police – Iran
Police – Belgium
CyberCrime – Bulgaria
Polícia Federal – Brazil
Polizei – Austria
ACSC – Australia
Police Scotland – Scotland
Singapore Police Force – Singapore
IC3 – United States
Polisen – Sweden
Policija – Slovenia
Ministerstvo Vnútra – Slovakia
National Police Agency – South Korea
Cyber Police – Ukraine
Policia Nacional – Spain
Centre for Cyber Security – Canada
References
- About the consequences of pirated software usage disclosure
- Forbes article about the stolen data selling


Leave a Comment