The Trojan:Win32/Vindor!pz detection, is a sign that your computer has a problem. Giving it a go may end up with really bad consequences.
Win32/Vindor is a threat that aims at blocking your system and asking for a ransom to revert the changes. To notify the victim it displays a banner with a scary text. Typically, hackers use appeals to law enforcement, who allegedly blocked your PC for violating the law.
Trojan:Win32/Vindor!pz Summary
- Sample contains Overlay data;
- Reads data out of its own binary image;
- Drops a binary and executes it;
- Unconventionial language used in binary resources: Turkish;
- Authenticode signature is invalid;
- Installs itself for autorun at Windows startup;
- Operates on local firewall’s policies and settings;
- Encrypting the documents kept on the target’s drives — so the victim cannot open these documents;
- Blocking the launching of .exe files of security tools
- Blocking the launching of installation files of security tools
Manual Trojan:Win32/Vindor!pz Removal
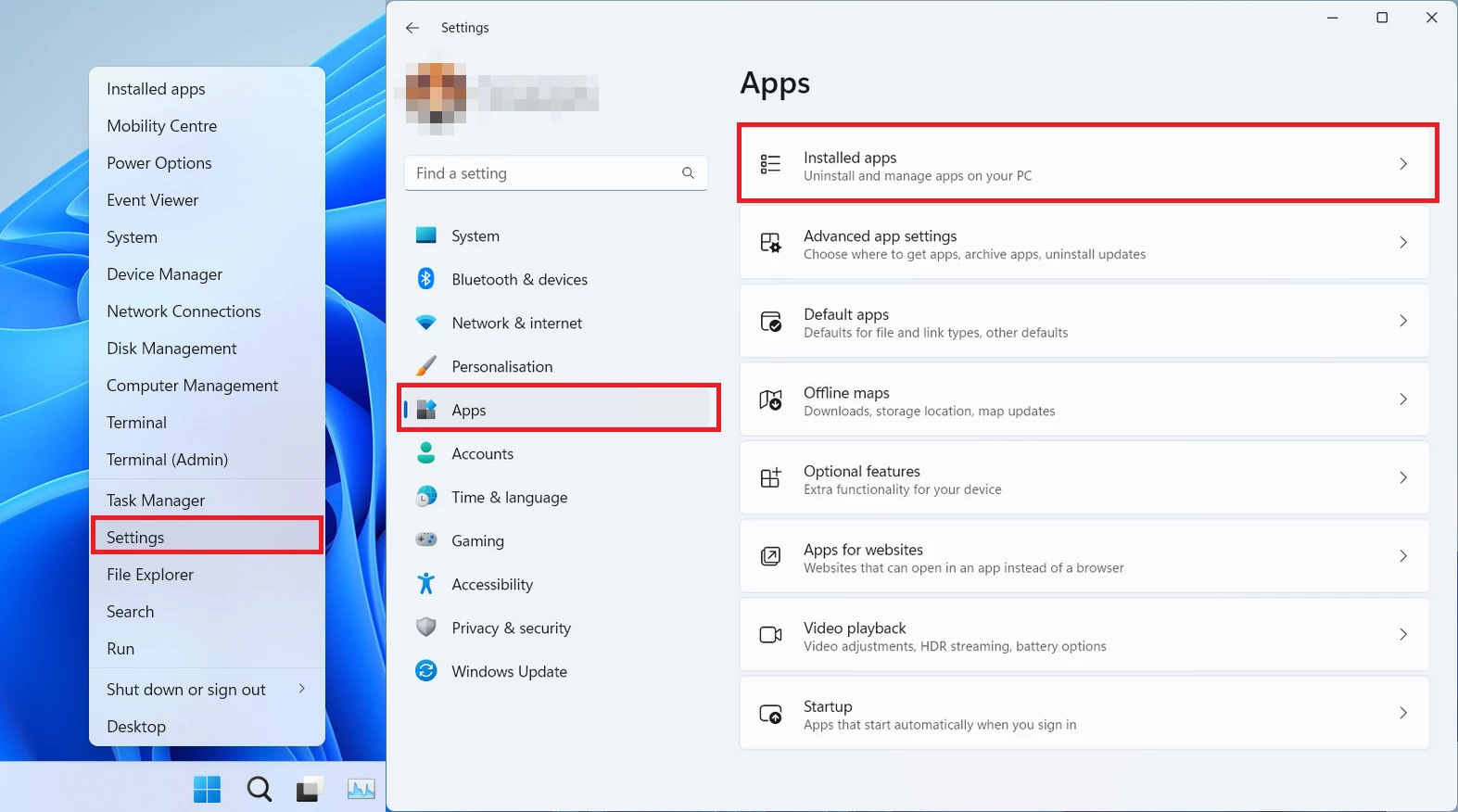
You can try removing Vindor manually, through the system Settings app. Click the Windows button with the right mouse button and find Settings in the appeared list. In Settings, go to Apps → Installed Apps menu.
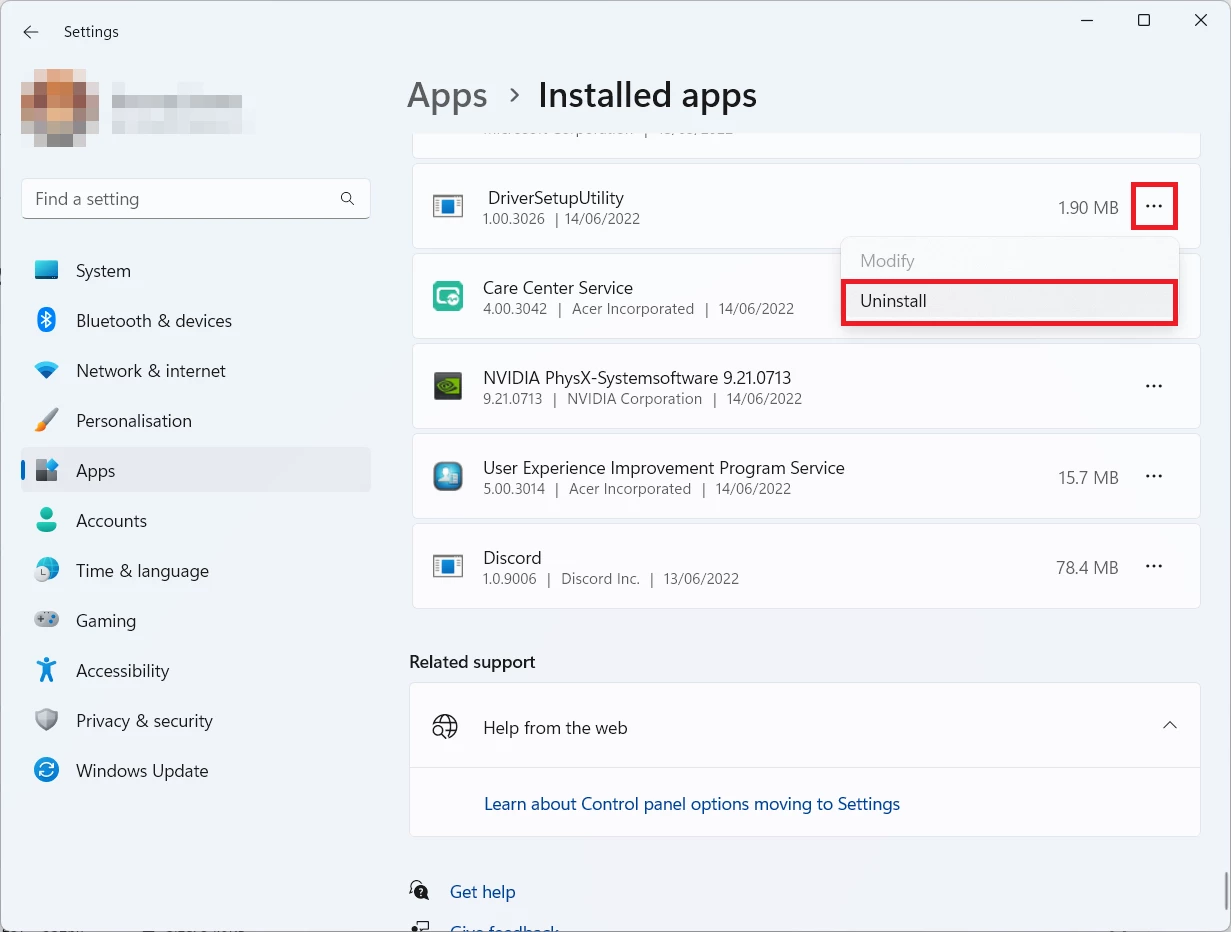
There, find the apps you do not remember installing. If you know a specific one that Windows Defender is complaining on with the Win32/Tnega!MSR detection, seek for them. Click the three-dot symbol to the right, and then choose “Uninstall”.


Leave a Comment