Gatz virus is a STOP/DJVU family of ransomware-type infections. This virus encrypts your files (video, photos, documents) that can be tracked by a “.gatz” extension. It uses a strong encryption method, which makes it impossible to calculate the key in any way.
I’ve compiled a comprehensive list of all possible solutions, tips, and practices in neutralizing the Gatz virus, and decrypting files. In some instances, it’s easy to retrieve your files. And sometimes it is just impossible.
 Be careful!
Be careful!
Payment of the ransom doesn’t ensure that you will receive your files back. The cybercriminals behind the Gatz virus are notoriously untrustworthy There have been instances where they have failed to supply the key to decrypt your files even after receiving the ransom.
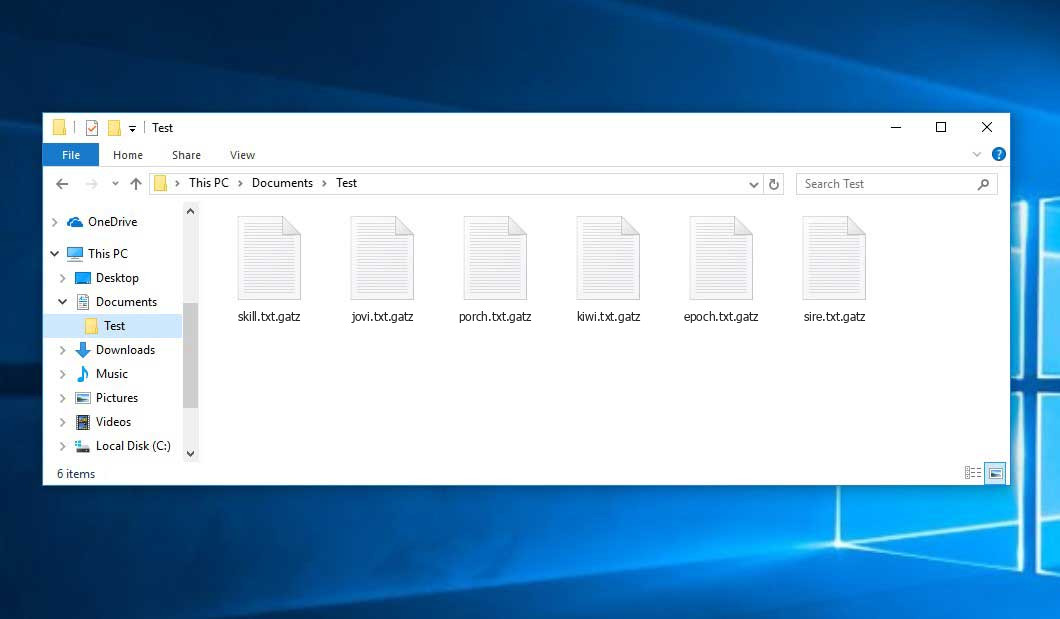
Once the Gatz virus is introduced into a computer system and starts to encrypt files, it begins and then adds the “.gatz” extension to the encrypted files. The virus demands a ransom payment in exchange for a key to decrypt the files which will allow the unlocking of encrypted files. In the majority of cases, the ransom note will appear as either a text file “_readme.txt”.
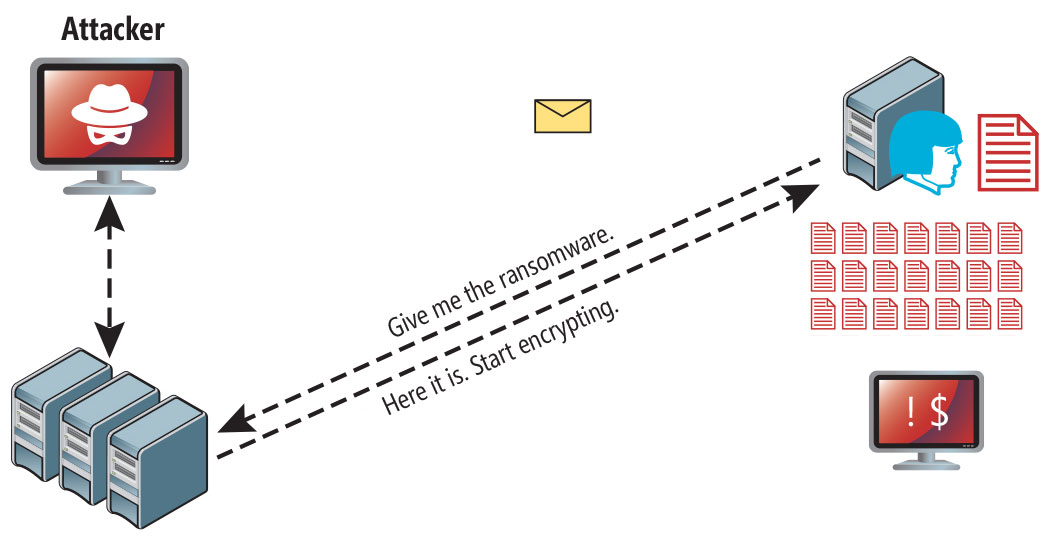
“Gatz” uses a unique code for every victim, with an exception:
- If Gatz is unable to establish a connection with the command and control server (C&C Server) prior to beginning the encryption process, it uses offline keys. This key is the same for all victims, making the possibility of decrypting encrypted files during a ransomware attack.
Is Gatz virus?
 Gatz can be correctly identified as a STOP/DJVU ransomware infection.
Gatz can be correctly identified as a STOP/DJVU ransomware infection.
Gatz

The Gatz ransomware is a specific kind of malware that encrypted your files and then forces you to pay to restore them. Note that Djvu/STOP ransomware family was first revealed and analyzed by virus analyst Michael Gillespie.
Gatz virus is similar to other DJVU ransomware like: Xash, Gash, Qore, Qopz. This virus encrypts all popular file types and adds its own “.gatz” extension into all files. For example, the file “1.jpg”, will be changed into “1.jpg.gatz“. As soon as the encryption is accomplished, the virus generates a special message file “_readme.txt” and adds it into all folders that contain the modified files.
The image below gives a clear vision of how the files with “.gatz” extension look like:
| Name | Gatz Virus |
| Ransomware family1 | DJVU/STOP2 ransomware |
| Extension | .gatz |
| Ransomware note | _readme.txt |
| Ransom | From $490 to $980 (in Bitcoins) |
| Contact | support@fishmail.top, datarestorehelp@airmail.cc |
| Detection | Wacatac: How to remove trojan from your computer?, Trojan:Win32/Azorult.CC!MTB, Trojan.Polyransom |
| Symptoms |
|
| Fix Tool | To remove possible malware infections, scan your PC: 6-day free trial available. |
This _readme.txt file asking payment is for restoring files via decryption key:
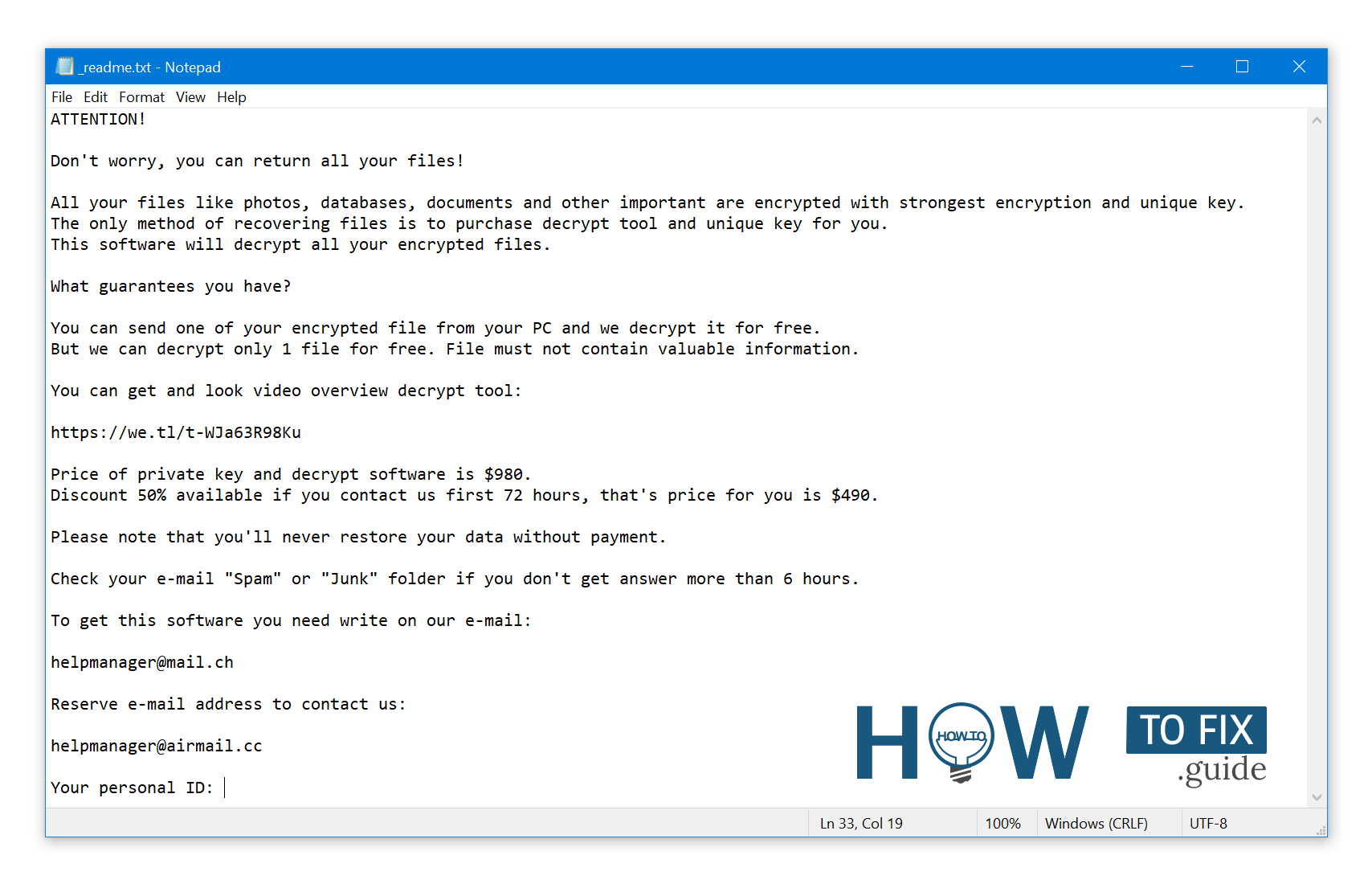
_readme.txt (STOP/DJVU Ransomware) – The scary alert demanding from users to pay the ransom to decrypt the encoded files contains these frustrating warnings
Gatz ransomware arrives as a set of processes that are meant to perform different tasks on a victim’s computer. One of the first ones being launched is winupdate.exe, a tricky process that displays a fake Windows update prompt during the attack. This is meant to convince the victim that a sudden system slowdown is caused by a Windows update. However, at the same time, the ransomware runs another process (usually named after four random characters) which starts scanning the system for target files and encrypting them. Next, the ransomware deletes Volume Shadow Copies from the system using the following CMD command:
vssadmin.exe Delete Shadows /All /Quiet
Once deleted, it becomes impossible to restore the previous computer state using System Restore Points. The thing is, ransomware operators are getting rid of any Windows OS-based methods that could help the victim to restore files for free. In addition, the crooks modify the Windows HOSTS file by adding a list of domains to it and mapping them to the local IP. As a result, the victim will run into a DNS_PROBE_FINISHED_NXDOMAIN error when accessing one of the blocked websites.
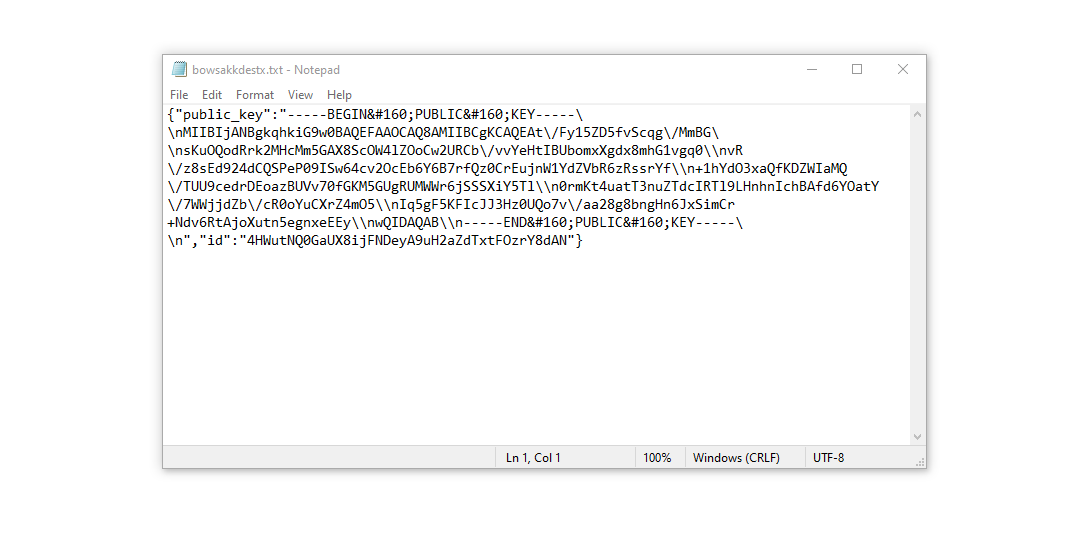
We noticed that ransomware attempts to block websites that publish various how-to guides for computer users. It is evident that by restricting specific domains, the crooks are trying to prevent the victim from reaching relevant and helpful ransomware-attack-related information online. The virus also saves two text files on the victim’s computer that provide attack-related details – the victim’s public encryption key and personal ID. These two files are called bowsakkdestx.txt and PersonalID.txt.
After all these modifications, the malware doesn’t stop. Variants of STOP/DJVU tend to drop Vidar password-stealing Trojan on compromised systems. This threat has a lengthy list of capabilities, such as:
- Stealing Steam, Telegram, Skype login/password;
- Stealing cryptocurrency wallets;
- Downloading malware to the computer and running it;
- Stealing browser cookies, saved passwords, browsing history, and more;
- Viewing and manipulating files on victim’s computer;
- Allowing the hackers to perform other tasks on the victim’s computer remotely.
The DJVU/STOP ransomware family utilizes the AES-256 cryptography algorithm. If the ransomware has encrypted your files with an online decryption key, a unique key is necessary to decrypt them. Unfortunately, it is impossible to decrypt the files without this key.
If Gatz was used in online mode, you cannot access the AES-256 key. The criminals who distribute the Gatz virus store the key on a remote server.
To obtain the decryption key, you must pay $980. The message encourages victims to contact the frauds via email (support@fishmail.top) to obtain payment details.
The message by the ransomware states the following information:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-WJa63R98Ku Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: support@fishmail.top Reserve e-mail address to contact us: datarestorehelp@airmail.cc Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
Do not pay for Gatz!
Please, try to use the available backups, or Decrypter tool
_readme.txt file also indicates that the computer owners must get in touch with the Gatz representatives within 72 hours starting from the moment of files were encrypted. On the condition of getting in touch within 72 hours, users will be granted a 50% rebate. Thus the ransom amount will be minimized to $490). Yet, stay away from paying the ransom!
I strongly recommend that you do not contact these crooks and do not pay. One of the most real working solutions to recover lost data – just using the available backups, or using Decrypter tool.
All such viruses apply a similar set of actions to generate the unique decryption key required to recover the ciphered data. Therefore, manual recovery of the ciphered data is impossible unless the ransomware is still in the development stage or has some hard-to-track flaws. Regularly backing up your crucial files is the only solution to prevent the loss of valuable data.
It should be noted that even if backups are maintained regularly, they must be stored in a specific location without loitering, and not connected to the main workstation. For example, the backup may be kept on a USB flash drive or an alternative external hard drive storage. Alternatively, the help of online (cloud) information storage can be referred to.
It is needless to mention that when backup data is maintained on a common device, it may also be ciphered like other data. For this reason, locating the backup on the main PC is surely not a wise idea.
How I was infected?
Ransomware has various methods to build into your system. But it doesn’t really matter what method had a place in your case.
Gatz attack following a successful phishing attempt.
- hidden installation along with other apps, especially the utilities that work as freeware or shareware;
- dubious link in spam emails leading to the virus installer
- online free hosting resources;
- using illegal peer-to-peer (P2P) resources for downloading pirated software.
There were cases when the Gatz virus was disguised as some legitimate tool, for example, in the messages demanding to initiate some unwanted software or browser updates. This is typically the way how some online frauds aim to force you into installing the Gatz ransomware manually, by actually making you directly participate in this process.
Surely, the bogus update alert will not indicate that you are going to actually inject the ransomware. This installation will be concealed under some alert mentioning that allegedly you should update Adobe Flash Player or some other dubious program whatsoever.
Cracked apps represent damage and can result in the injection of serious malware, including the Gatz ransomware. Using P2P is illegal and may lead to this type of malware infecting your device.
To prevent Gatz ransomware from penetrating your device, you need to be cautious while installing free software. There is no 100% guarantee to prevent your PC from getting damaged, but there are certain tips you can follow.
Always read what the installers offer in addition to the main free program. Stay away from opening dubious email attachments and do not open files from unknown addresses. Make sure to update your current security program regularly.
The malware does not openly disclose itself and will not be mentioned in the list of available programs. However, it will be masked under some malicious process running regularly in the background, starting from the moment when you launch your PC.
How To Remove Gatz Virus?
In addition to encoding a victim’s files, the Gatz infection has also started to install the Vidar Stealer on the system to steal account credentials, cryptocurrency wallets, desktop files, and more.3
Reasons why I would recommend GridinSoft4
There is no better way to recognize, remove and prevent ransomware than to use anti-malware software from GridinSoft5.
Download Removal Tool.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press the “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for complete.
GridinSoft Anti-Malware will automatically start scanning your computer for Gatz infections and other malicious programs. This process can take 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has completed, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Trojan Killer for special instances
In some certain instances, Gatz ransomware can block the running of setup files of different anti-malware programs. In this situation, you need to utilize the removable drive with a pre-installed antivirus tool.
There is a really little number of security tools that are able to be set up on USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft – Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version 6. This term will definitely be 100% enough to wipe malware out.
How To Decrypt .gatz Files?
Restore solution for big “.gatz files“
Try removing .gatz extension on a few BIG files and opening them. Either the Gatz infection read and did not encrypt the file, or it bugged and did not add the filemarker. If your files are very large (2GB+), the latter is most likely. Please, let me know in the comments if that will work for you.
The newest extensions were released around the end of August 2019 after the criminals made changes. This includes Saba, Sato, Fofd, etc.
As a result of the changes made by the criminals, STOPDecrypter is no longer supported. It has been removed and replaced with the Emsisoft Decryptor for STOP Djvu Ransomware developed by Emsisoft.
You can download free decryption tool here: Decryptor for STOP Djvu.
Download and run decryption tool.
Start downloading the decryption tool.
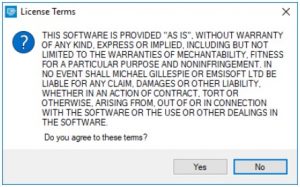
Make sure to launch the decryption utility as an administrator. You need to agree with the license terms that will come up. For this purpose, click on the “Yes” button:
As soon as you accept the license terms, the main decryptor user interface comes up:
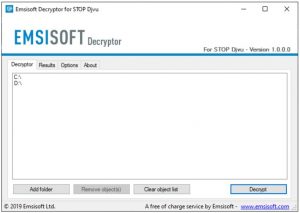
Select folders for decryption.
Based on the default settings, the decryptor will automatically populate the available locations in order to decrypt the currently available drives (the connected ones), including the network drives. Extra (optional) locations can be selected with the help of the “Add” button.
Decryptors normally suggest several options considering the specific malware family. The current possible options are presented in the Options tab and can be activated or deactivated there. You may locate a detailed list of the currently active Options below.
Click on the “Decrypt” button.
As soon as you add all the desired locations for decryption to the list, click on the “Decrypt” button in order to initiate the decryption procedure.
Note that the main screen may turn you to a status view, letting you know of the active process and the decryption statistics of your data:
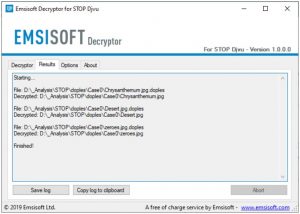
The decryptor will notify you as soon as the decryption procedure is completed. If you need the report for your personal papers, you can save it by choosing the “Save log” button. Note that it is also possible to copy it directly to your clipboard and paste it into emails or messages here if you need to do so.
The Emsisoft Decryptor might display different messages after a failed attempt to restore your gatz files:
✓ Error: Unable to decrypt file with ID: [your ID]
✓ No key for New Variant online ID: [your ID]
Notice: this ID appears to be an online ID, decryption is impossible

✓ Result: No key for new variant offline ID: [example ID]
This ID appears to be an offline ID. Decryption may be possible in the future.

It can take a few weeks or months until the decryption key gets found and uploaded to the decryptor. Please follow updates regarding the decryptable DJVU versions here.
✓ Remote name could not be resolved
How to Restore .gatz Files?
In some cases Gatz ransomware is not doom for your files…
Gatz ransomware encryption mechanism feature is next: it encrypts every file byte-by-byte, then saves a file copy, deleting (and not overriding!) the original file. Hence, the information on the file location on the physical disk is lost, but the original file is not deleted from the physical disk. The cell, or the sector where this file was stored, can still contain this file, but it is not listed by the file system and can be overwritten by data that has been loaded to this disk after the deletion. Hence, it is possible to recover your files using special software.
Anyway, after realizing it was an online algorithm, it is impossible to retrieve my encrypted files. I also had my backup drive plugged in at the time of the virus, and this was also infected, or so I thought. Every folder within my backup drive had been infected and was encrypted. However, despite losing some important files, I retrieved almost 80% of my 2TB storage.
When I started going through the folders, I noticed the readme.txt ransom note in every folder. I opened some of the folders and found that all files that were not in a subfolder within that folder had been encrypted. However, I found a flaw and a glimmer of hope when I went into the subfolders in other folders and found that these files had not been encrypted. Every folder within my c and d drives, including subfolders, had been encrypted, but this was not the case with the backup drive. Having subfolders created within a folder has saved 80% of my data.
As I said, I believe this to be only a small loophole on a backup drive. I’ve since found a further 10 % of my data on another hard drive on a different pc. So my advice is if you use a backup drive, create subfolders. I was lucky, I guess. But I was also unlucky that the virus hit as I was transferring some files from my backup.
Hopefully, this can help some other people in my situation.
Jamie NewlandRecovering your files with PhotoRec
PhotoRec is an open-source program, which is originally created for files recovery from damaged disks, or for files recovery in case if they are deleted. However, as time has gone by, this program got the ability to recover the files of 400 different extensions. Hence, it can be used for data recovery after the ransomware attack
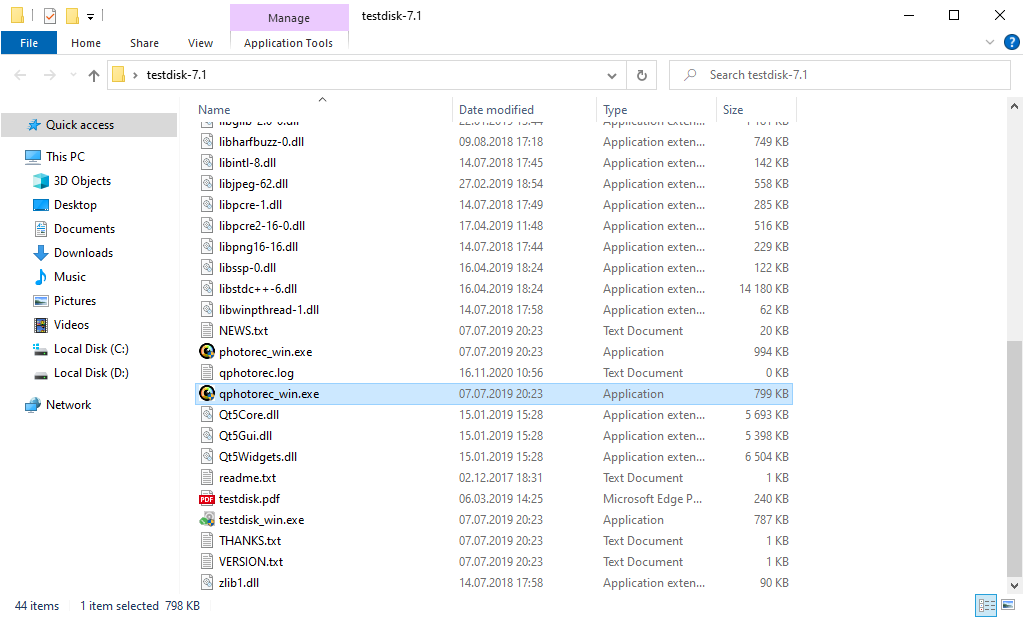
At first, you need to download this app. It is 100% free, but the developer states that there is no guarantee that your files will be recovered. PhotoRec is distributed in a pack with other utilities of the same developer – TestDisk. The downloaded archive will have a TestDisk name, but don’t worry. PhotoRec files are right inside.
To open PhotoRec, you need to find and open “qphotorec_win.exe” file. No installation is required – this program has all the files it need inside of the archive, hence, you can fit it on your USB drive, and try to help your friend/parents/anyone who was been attacked by DJVU/STOP ransomware.
After the launch, you will see the screen showing you the full list of your disk spaces. However, this information is likely useless, because the required menu is placed a bit higher. Click this bar, then choose the disk which was attacked by ransomware.
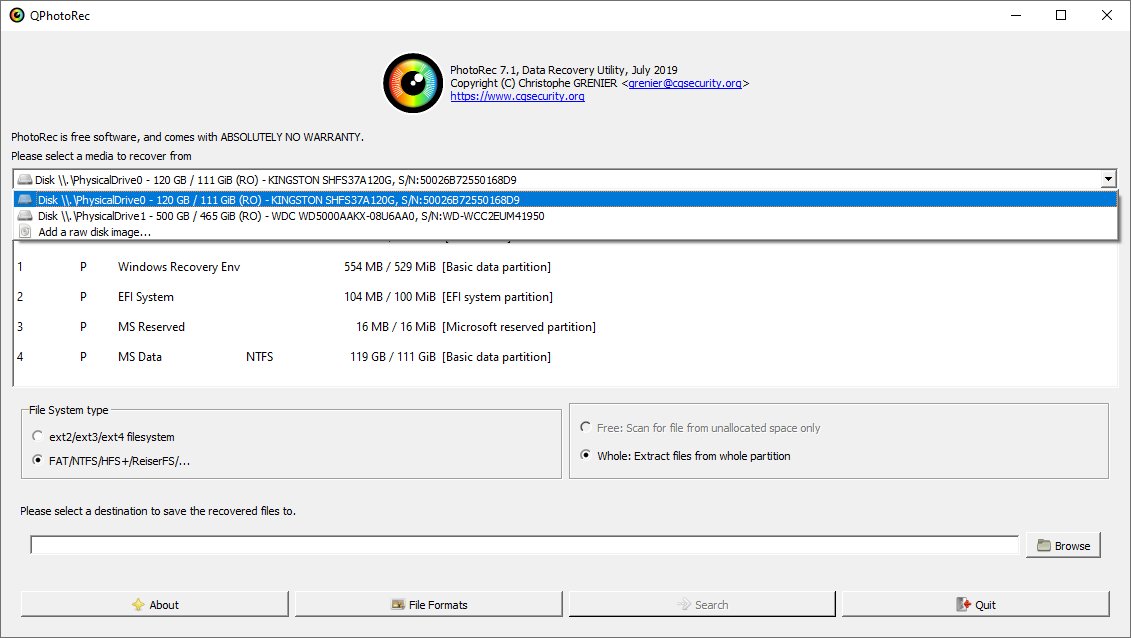
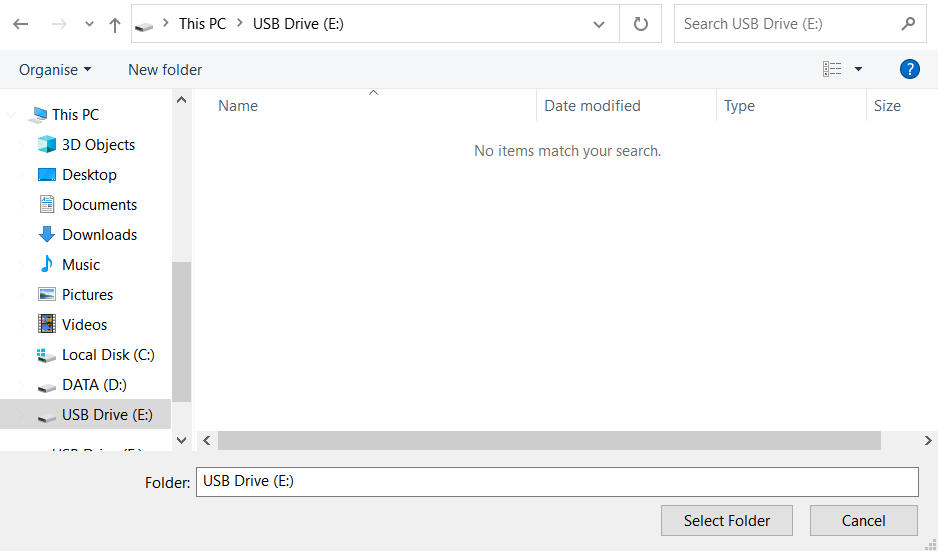
After choosing the disk, you need to choose the destination folder for the recovered files. This menu is located at the lower part of the PhotoRec window. The best decision is to export them on a USB drive or any other type of removable disk.
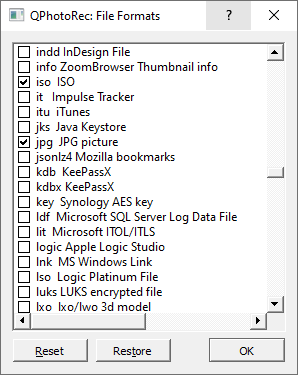
Then, you need to specify the file formats. This option is located at the bottom, too. As it was mentioned, PhotoRec can recover files of about 400 different formats.
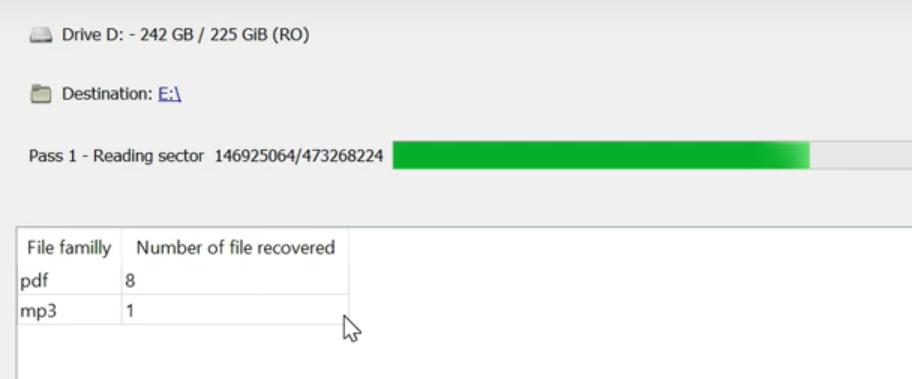
Finally, you can start file recovery by pressing the “Search” button. You will see the screen where the results of the scan and recovery are shown.
Gatz files recovery guide
Frequently Asked Questions
 How can I open “.gatz” files?
How can I open “.gatz” files?No way. These files are modified by ransomware. The contents of .gatz files are not available until they are decrypted.
 Gatz files contain important information. How can I decrypt them urgently?
Gatz files contain important information. How can I decrypt them urgently?If your data remained in the .gatz files is very valuable, then most likely you made a backup copy.
If not, then you can try to restore them through the system function – Restore Point.
All other methods will require patience.
 You have advised using GridinSoft Anti-Malware to remove Gatz. Does this mean that the program will delete my encrypted files?
You have advised using GridinSoft Anti-Malware to remove Gatz. Does this mean that the program will delete my encrypted files?Of course not. Your encrypted files do not pose a threat to the computer. What happened has already happened.
You need GridinSoft Anti-Malware to remove active system infections. The virus that encrypted your files is most likely still active and periodically runs a test for the ability to encrypt even more files. Also, these viruses install keyloggers and backdoors for further malicious actions (for example, theft of passwords, credit cards) often.
 Gatz virus has blocked the infected PC: I can’t get the activation code.
Gatz virus has blocked the infected PC: I can’t get the activation code.In this situation, you need to prepare the memory stick with a pre-installed Trojan Killer.
 Decryptor did not decrypt all my files, or not all of them were decrypted. What should I do?
Decryptor did not decrypt all my files, or not all of them were decrypted. What should I do?Have patience. You are infected with the new version of STOP/DJVU ransomware, and decryption keys have not yet been released. Follow the news on our website.
We will keep you posted when new Gatz keys or new decryption programs appear.
 What can I do right now?
What can I do right now?The Gatz ransomware encrypts only the first 150KB of files. So MP3 files are rather large, some media players (Winamp for example) may be able to play the files, but – the first 3-5 seconds (the encrypted portion) will be missing.
You can try to find a copy of an original file that was encrypted:
- Files you downloaded from the Internet that were encrypted and you can download again to get the original.
- Pictures that you shared with family and friends that they can just send back to you.
- Photos that you uploaded on social media or cloud services like Carbonite, OneDrive, iDrive, Google Drive, etc)
- Attachments in emails you sent or received and saved.
- Files on an older computer, flash drive, external drive, camera memory card, or iPhone where you transferred data to the infected computer.
Also, you can contact the following government fraud and scam sites to report this attack:
- In the United States: On Guard Online;
- In Canada: Canadian Anti-Fraud Centre;
- In the United Kingdom: Action Fraud;
- In Australia: SCAMwatch;
- In New Zealand: Consumer Affairs Scams;
- In India, go to Indian National Cybercrime Reporting Portal.
- In France: Agence nationale de la sécurité des systèmes d’information;
- In Poland: KOMENDA GŁÓWNA POLICJI;
- In Portugal: Polícia Judiciária;
- In Italy: Polizia di Stato;
- In Spain: Cuerpo Nacional de Policía;
- In Germany: Bundesamt für Sicherheit in der Informationstechnik;
- In Ireland: An Garda Síochána;
To report the attack, you can contact local executive boards (A full list you can find here). For instance, if you live in the USA, you can have a talk with FBI Local field office, IC3 or Secret Service.
Video Guide
It’s my favorite video tutorial: How to use GridinSoft Anti-Malware and Emsisoft Decryptor for fix ransomware infections.
If the guide doesn’t help you to remove Gatz virus, please download the GridinSoft Anti-Malware that I recommended. Do not forget to share your experience in solving the problem. Please leave a comment here! This can help other victims to understand they are not alone. And together we will find ways to deal with this issue.
I need your help to share this article.
It is your turn to help other people. I have written this guide to help users like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithGATZ Ransomware — How To Restore & Decrypt Files?
Name: GATZ Virus
Description: GATZ Virus is a STOP/DJVU family of ransomware-type infections. This virus encrypts your files, video, photos, documents that can be tracked by a specific gatz extension. So, you can't use them at all after that GATZ ransomware asks victims for a ransom fee ($490 - $980) in Bitcoin.
Operating System: Windows
Application Category: Virus
User Review
( votes)References
- My files are encrypted by ransomware, what should I do now?
- About DJVU (STOP) Ransomware.
- Windows passwords vulnerability (Mimikatz HackTool): https://howtofix.guide/mimikatz-hacktool/
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison
- Trojan Killer Review: https://howtofix.guide/trojan-killer/
![]() German
German ![]() Japanese
Japanese ![]() Spanish
Spanish ![]() Portuguese (Brazil)
Portuguese (Brazil) ![]() French
French ![]() Turkish
Turkish ![]() Chinese (Traditional)
Chinese (Traditional) ![]() Korean
Korean ![]() Indonesian
Indonesian ![]() Hindi
Hindi ![]() Italian
Italian

 FIX & DECRYPT DATA
FIX & DECRYPT DATA