The Xrp virus belongs under the GlobeImposter ransomware family. Harmful software of this type encrypts all user’s data on the computer (photos, text files, excel sheets, audio files, videos, etc) and appends its own extension to every file, creating the Read_For_Restore_File.html files in each folder containing encrypted files.
What is Xrp virus?
☝️ Xrp is a GlobeImposter family ransomware-type infection.
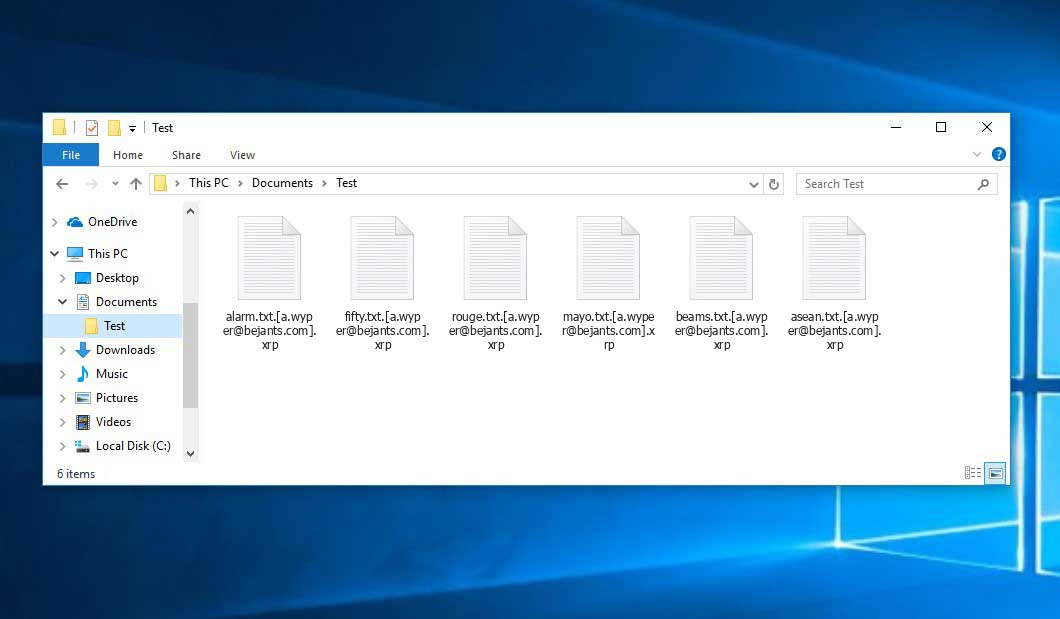
The scheme of renaming is this: .xrp. As a part of encryption, a file entitled, for instance, “report.docx” will be turned into “report.docx.[[email protected]].xrp”.
In every directory containing the encrypted files, a Read_For_Restore_File.html file will be created. It is a ransom money memo. Therein you can find information about the ways of paying the ransom and some other remarks. The ransom note most probably contains a description of how to buy the decryption tool from the tamperers. You can get this tool after contacting [email protected] through email. That is basically the scheme of the crime.
Xrp Overview:
| Name | Xrp Virus |
| Ransomware family1 | GlobeImposter ransomware |
| Extension | .xrp |
| Ransomware note | Read_For_Restore_File.html |
| Contact | [email protected] |
| Detection | Backdoor:Win32/Xtrat.B Virus Removal, Ransom:Win32/Mazedec.TA!MSR Virus Removal, Picsys.Worm.Bot.DDS Virus Removal |
| Symptoms | Your files (photos, videos, documents) have a .xrp extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Xrp virus |
The Read_For_Restore_File.html document accompanying the Xrp ransomware provides the following frustrating information:
YOUR FILES ARE ENCRYPTED! Your documents, photos, databases and all the rest files encrypted cryptographically strong algoritm RSA-2048. Without a secret key stored with us, the restoration of your files is impossible ---------------------------------------------------------- To start the recovery process: Register email box to protonmail.com or cock.li (do not waste time sending letters from your standard email address, they will all be blocked). Send a email from your new email address to: [email protected] with your personal ID. In response, we will send you further instructions on decrypting your files. --------------------------------------------------------- Your personal ID: - ----------------------------- P.S. ---------------------------------- It is in your interest to respond as soon as possible to ensure the recovery of your files, because we will not store your decryption keys on our server for a long time. Сheck the folder \"Spam\" when waiting for an email from us. If we do not respond to your message for more than 48 hours, write to the backup email : [email protected] ----------- Q: Did not receive an answer? A: Check the SPAM folder. Q: My spam folder is empty, what should I do? A: Register email box to protonmail.com or cock.li and do the steps above.
In the screenshot below, you can see what a directory with files encrypted by the Xrp looks like. Each filename has the “.xrp” extension added to it.
How did my machine catch Xrp ransomware?
There are plenty of possible ways of ransomware injection.
Nowadays, there are three most popular methods for hackers to have the Xrp virus acting in your system. These are email spam, Trojan introduction and peer-to-peer networks.
- Another option for ransom hunters is a Trojan file scheme. A Trojan is a program that infiltrates into your machine disguised as something else. For instance, you download an installer for some program you want or an update for some program. But what is unpacked turns out to be a harmful program that compromises your data. As the update package can have any name and any icon, you’d better be sure that you can trust the resource of the things you’re downloading. The best thing is to use the software companies’ official websites.
- As for the peer-to-peer networks like torrent trackers or eMule, the threat is that they are even more trust-based than the rest of the Web. You can never know what you download until you get it. Our suggestion is that you use trustworthy websites. Also, it is reasonable to scan the directory containing the downloaded items with the anti-malware utility as soon as the downloading is finished.
How do I get rid of ransomware?
It is important to note that besides encrypting your files, the Xrp virus will probably install Vidar Stealer on your machine to seize your credentials to different accounts (including cryptocurrency wallets). The mentioned program can extract your credentials from your browser’s auto-filling data.
How сan I avoid ransomware attack?
Xrp ransomware doesn’t have a endless power, neither does any similar malware.
You can protect your PC from its attack in three easy steps:
- Never open any letters from unknown mailers with strange addresses, or with content that has likely no connection to something you are expecting (how can you win in a money prize draw without participating in it?). If the email subject is likely something you are expecting, scrutinize all elements of the questionable email with caution. A fake letter will always contain mistakes.
- Do not use cracked or unknown software. Trojan viruses are often spreaded as a part of cracked software, possibly as a “patch” to prevent the license check. Understandably, untrusted programs are very hard to distinguish from reliable software, as trojans may also have the functionality you seek. You can try searching for information on this software product on the anti-malware forums, but the optimal solution is not to use such programs at all.
FAQ
🤔 Can I somehow access “.xrp” files?
There’s no way to do it, unless the files “.xrp” files are decrypted.
🤔 I really need to decrypt those “.xrp” files ASAP. How can I do that?
If the “.xrp” files contain some really important information, then you probably have them backed up. Otherwise, you might try to employ System Restore. The only question is whether you have saved any Restore Points that would be helpful now. There are other ways to beat ransomware, but they take time.
🤔 What should I do if the Xrp ransomware has blocked my PC and I can’t get the activation key.
🤔 What can I do right now?
Some of the encrypted files can be located elsewhere.
- If you sent or received your critical files via email, you could still download them from your online mailbox.
- You might have shared images or videos with your friends or family members. Simply ask them to post those pictures back to you.
- If you have initially got any of your files from the Web, you can try doing it again.
- Your messengers, social networks pages, and cloud drives might have all those files as well.
- Maybe you still have the needed files on your old computer, a laptop, mobile, external storage, etc.
USEFUL TIP: You can employ file recovery programs2 to retrieve your lost information since ransomware blocks the copies of your files, removing the original ones. In the video below, you can learn how to use PhotoRec for such a recovery, but be advised: you won’t be able to do it before you kill the ransomware itself with an antivirus program.


Leave a Comment