Loqw is malware that belongs to STOP/Djvu ransomware family. Its key action in the infected system is to encrypt as many user files as possible, and then ask to pay the ransom. After the encryption, you will see the .loqw file extensions on all your files.
Loqw Virus Overview
As I’ve said at the beginning, Loqw is an example of the STOP/Djvu ransomware family. This malware family attacks people since at least 2018, infecting thousands of victims across the globe. After infiltrating the victim’s device, malware starts seeking for the data throughout all the volumes present in the system, and ciphers them with AES-256 encryption algorithm.
To each of the ciphered files, it adds its specific .loqw extension. An image1.png will turn into image1.png.loqw, documentation.docx – into documentation.docx.loqw and the like. Removing the extension will not recover the files, and may also create problems with their further recovery.
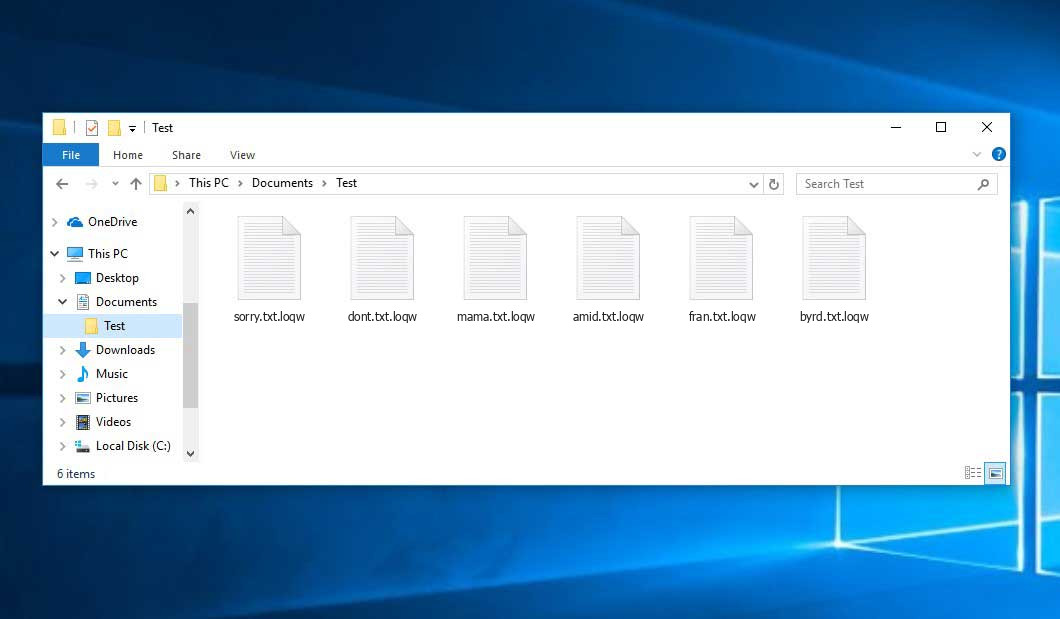
Encrypted Files by STOP/DJVU Ransomware
| Name | Loqw Virus |
| Ransomware family1 | DJVU/STOP2 ransomware |
| Extension | .loqw |
| Ransomware note | _readme.txt |
| Ransom | From $490 to $980 (in Bitcoins) |
| Contact | [email protected], [email protected] |
| Detection | Win32/Filecoder.Avaddon.H, TrojanDropper:Win32/BcryptInject.A!MTB, BScope.TrojanRansom.Reveton |
| Symptoms |
|
Loqw virus goes through directories one by one, creating a file in every folder once it is done encrypting files in it. The .txt file instructs you to pay the equivalent of $980 in Bitcoin to a specified cryptowallet. Rascals who stand behind this malware do not hunt for personal information, their only target is money extortion.
The message by the ransomware states the following information:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-WJa63R98Ku Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: [email protected] Reserve e-mail address to contact us: [email protected] Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
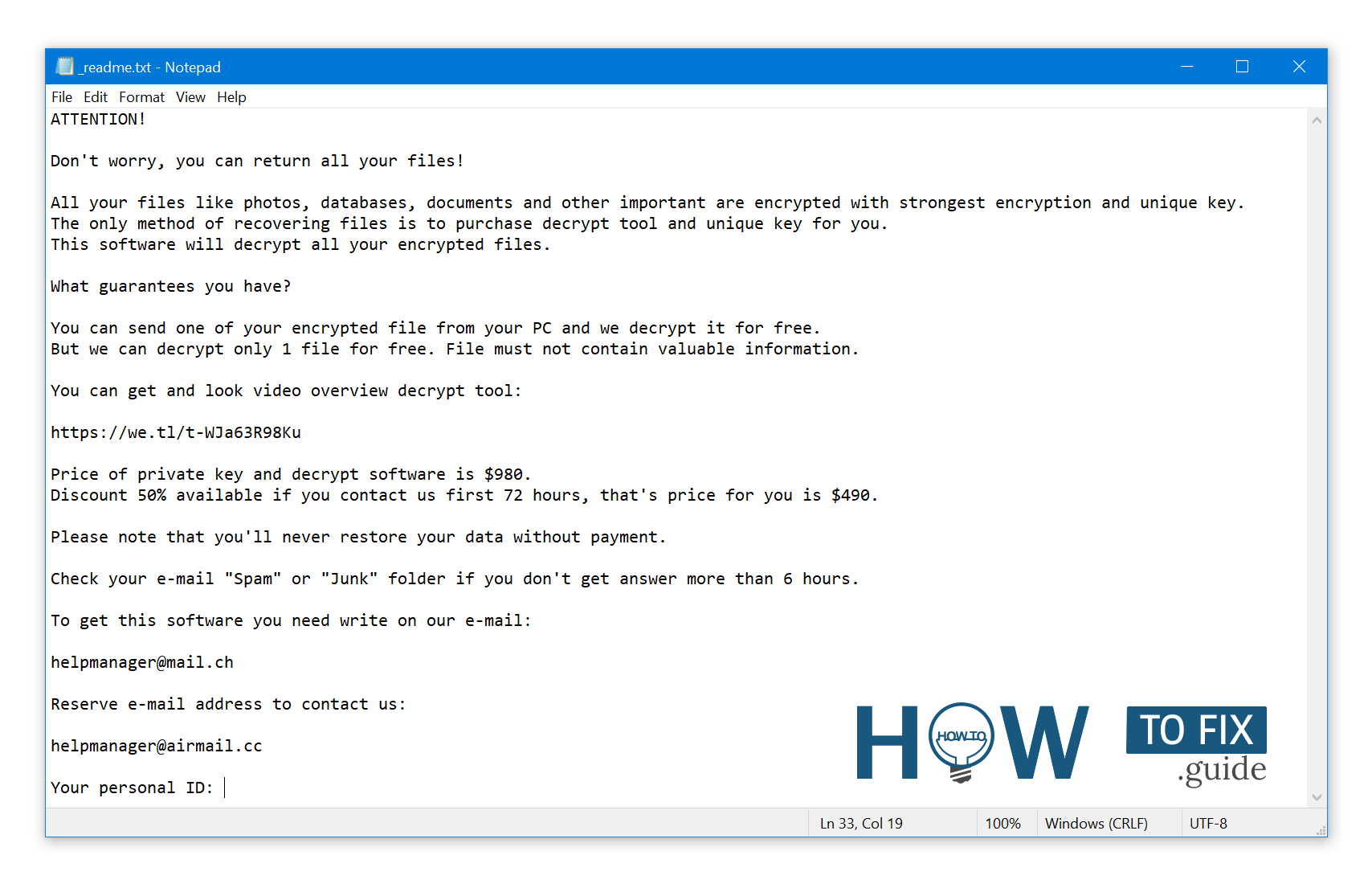
_readme.txt (STOP/DJVU Ransomware) – The scary alert demanding from users to pay the ransom to decrypt the encoded files contains these frustrating warnings
Never pay the ransom!
There is no guarantee that crooks will give you the decryptor, or will not ask you to pay a bigger sum. By paying off the ransom, you unwillingly sponsor their activity and future attacks. Moreover, the email you use for contacting the frauds can further become a target for email spam campaigns.
The ransom note shares basic information about the attack, the explanation of what happened, and the demand to pay $980 to the specified wallet. To make paying the ransom a more attractive option, crooks offer paying half a price for the decryptor during the first 72 hours after the attack. Hackers assure that there is no way to decrypt the files, except for using their decryptor.
As a contact information, attackers specify 2 emails from anonymous email services. Those are [email protected] and [email protected]. Both are in use for quite some time, which means the same crooks operate the ransom charging and negotiations.
How did ransomware infect my PC?
Typically, STOP/Djvu ransomware operators opt for popular topics, like a new game or a cracked program version. Beware of sites that spread torrents of a program that has just been released, or is even not publicly available yet. Crooks can also parasite on sharing pirated movies – by offering virus as a “video player” you should use to watch the movie.
How to remove Loqw ransomware?
Meanwhile, ransomware removal is an essential step before trying to perform any decryption operations. When the encryption is over, the malware keeps idling, searching for new files. If you will start recovering the data before the ransomware is gone, or will download new, unencrypted files, ransomware will cipher them almost immediately.
Video Guide
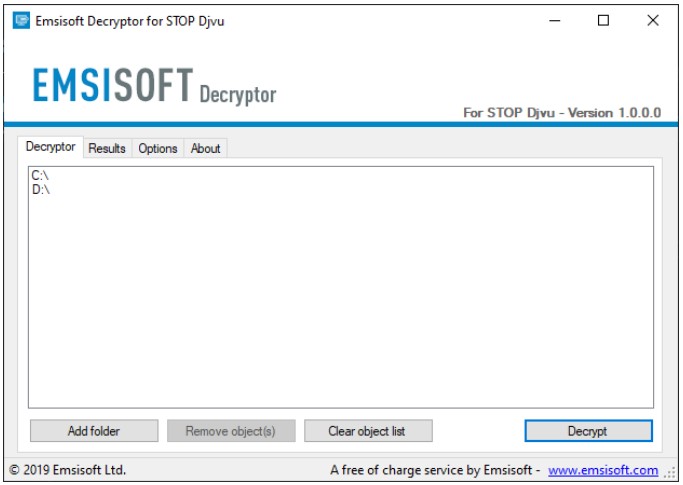
How to Decrypt .loqw Files?
Alternatively, there are a couple of other options you can try. The easiest thing is related to the malware’s problems when working with big files 1+GB. One more way is to use file recovery utilities – it can work out due to the peculiarity of the ransomware modus operandi. Let’s dig into them one by one.
How to restore big files?
As anything in the world, Loqw ransomware is not flawless. In particular, it has issues encrypting large files – ones that are 1GB and bigger. The malware struggles to start their encryption, thus just adds the extension and moves on. It is actually possible to just remove the .loqw extension from the file and use it almost as usual.
One more piece of good news is that smaller files may be usable, too. Videos and audio files, for example, get only their beginning encrypted – ransomware ciphers only the first 150KB of the file. Therefore, all other elements of the file are intact. Through using programs that do not check for the file integrity, for example, a good-old WinAmp, you can open them almost flawlessly. The only visible problem will be a missing part at the beginning – but that is nothing compared to losing the entire file.
How to recover .loqw files?
It is possible to recover the files encrypted by Loqw ransomware using file recovery tools. The malware does not overwrite the files; it instead creates a duplicate of the original file, ciphers it, and then deletes the source. Therehence, you can act as if the file was just unintentionally deleted, not encrypted.
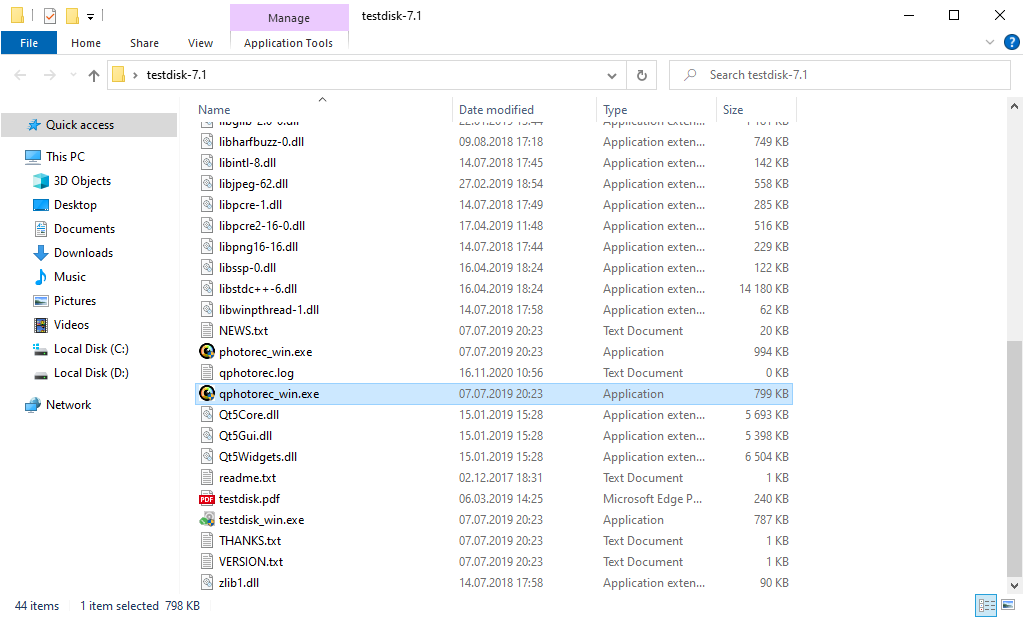
For such a purpose, I’d recommend PhotoRec. This free open-source utility supports recovering files of over 400 formats, and has proven itself in our tests. You can download the program by clicking the link. It comes in the package with the program of the same developer – TestDisk, and the archive with the utility carries its name.
To launch PhotoRec, you need to find and open “qphotorec_win.exe” file. No installation process is needed – this program has all the files it need inside of the archive, hence, you can fit it on your USB drive, and try to help your friends/parents/anyone who has been attacked by Loqw ransomware.
Upon the start, you will witness the screen showing you the full list of your disks. However, this information is presumably unhelpful, because the required menu is a bit higher. Click this tab, then choose the disk which was attacked by ransomware.
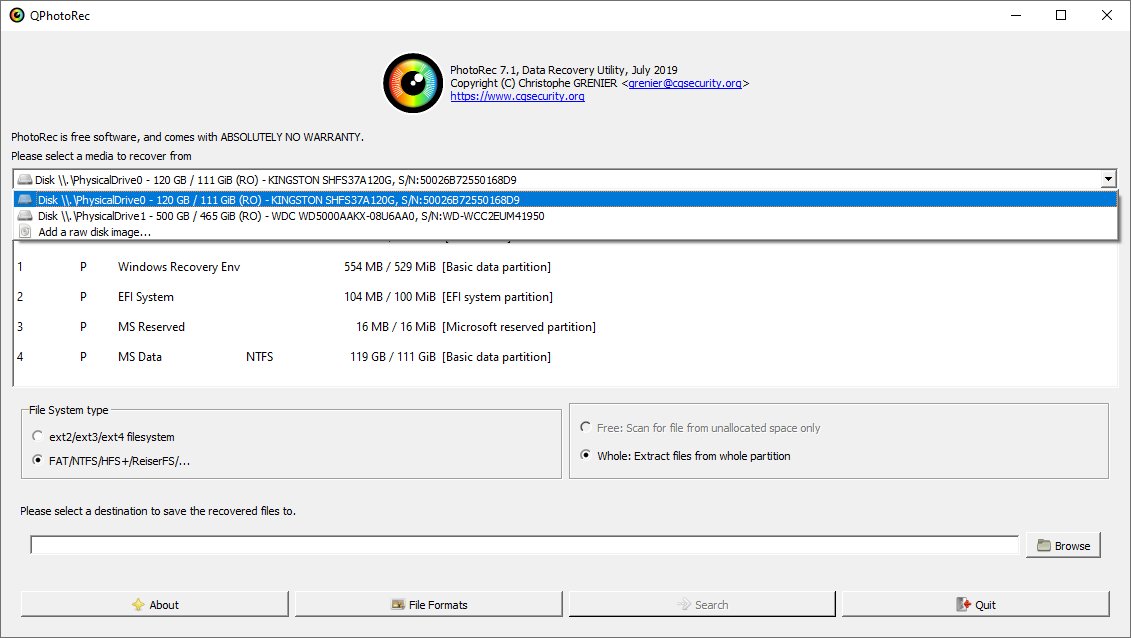
After picking the disk, you need to choose the destination folder for the reclaimed files. This menu is located at the lower part of the PhotoRec window. The best selection is to export them on USB drive or any other type of removable disk.
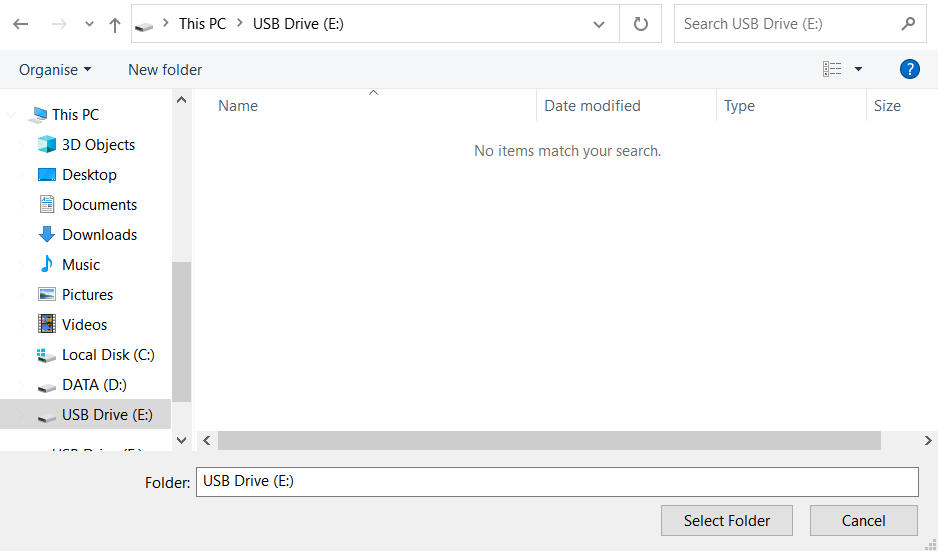
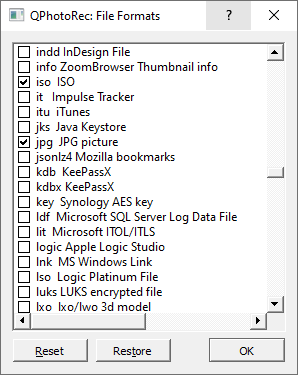
Then, you need to designate the file formats. You will find the option at the lower part, too. As I mentioned, PhotoRec can restore the files of about 400 different formats.
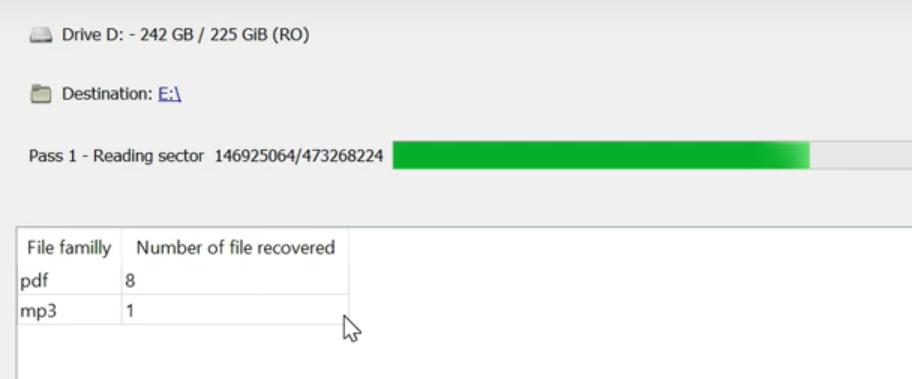
Finally, you can start files recovery by pressing the “Search” button. You will see the screen where the results of the scan and recovery are shown.
Loqw files recovery Video Guide.
Frequently Asked Questions
References
![]() German
German ![]() Japanese
Japanese ![]() Spanish
Spanish ![]() Portuguese (Brazil)
Portuguese (Brazil) ![]() French
French ![]() Turkish
Turkish ![]() Chinese (Traditional)
Chinese (Traditional) ![]() Korean
Korean ![]() Indonesian
Indonesian ![]() Hindi
Hindi ![]() Italian
Italian


Leave a Comment