The “Hello My Perverted Friend” phishing scam targets many blameless victims with deception. The fraudster’s email threatens to distribute explicit personal videos to extort money.
This fear-based social engineering aims to exploit panic and urgency, tricking users into paying ransoms. However, the hackers made no real malware infiltrations, video recordings, or account access. The technically falsified threats manipulate targets through raw fear over their reputation.
What Is “Hello My Perverted Friend” Email Scam?
The “Hello My Perverted Friend” scam email is an example of phishing, where the scammer addresses the target as “my perverted friend” to create a false sense of a hacker who has been spying on the target’s online activities for months.
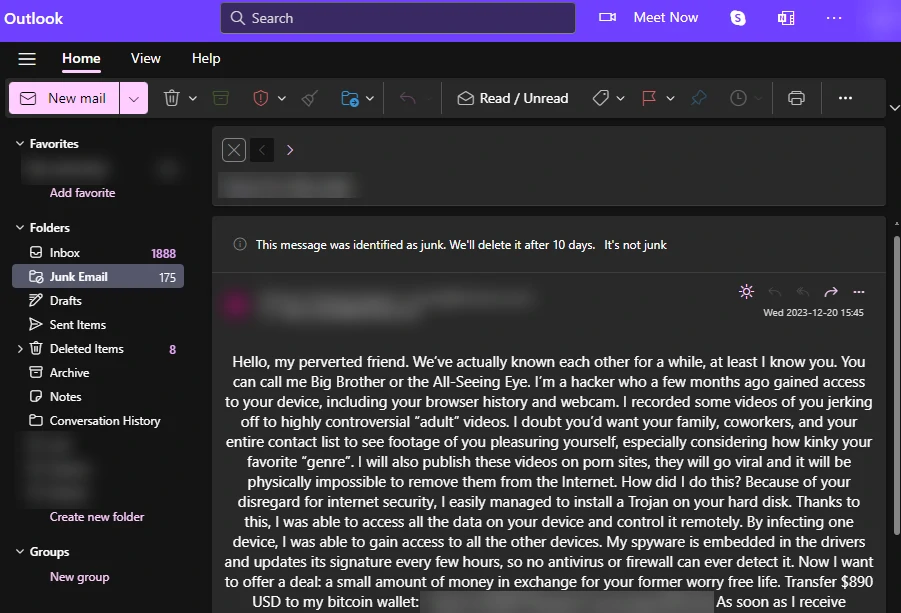
“Hello My Perverted Friend” Scam
| Name | “Hello My Perverted Friend” Email Scam |
| Threat Type | Phishing, Scam, Social Engineering |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Similar Behavitor | “Password Was Compromised Through A Legitimate Website” Email Scam, “Some Bad News That You Are About To Hear” Email Scam |
How Does “Hello My Perverted Friend” Scam Work?
Employing intimidating and shaming language, the phishing email describes supposed embarrassing sexual acts illegally captured through webcam access. It hopes that provoking panic will manipulate the target. Alleging the use of advanced malware, the scam claims to have easily bypassed security protections. Amping up threats, the fraudulent email warns it will virally spread explicit videos showcasing illegal situations across social media, adult sites, and video platforms. This ploy to ruin reputations gives the impression that such footage could become impossible to remove once publicly propagated. The deception attempts to leverage fear by claiming urgent ransom payment of $890 or more in anonymous cryptocurrency like Bitcoin provides the only containment hope against this fabricated sex scandal. Payment timeframe demands are short, typically 24 to 48 hours at most. Bitcoin wallet addresses are provided to submit funds.
In truth, no hacking, malware infections, or inappropriate recordings occurred. The criminals never gained account or device access as claimed. All technical jargon and explicit imagery threats lack factual basis, simply aiming to intimidate. The “Hello My Perverted Friend” phishing email uses raw fear to swindle money from victims. Preying on anxieties surrounding reputation damage from leaked sexual material, the cybercriminals hope to exploit confusion and urgency to trick targets into complying with ransom payment instructions.
Is It Dangerous?
Although this phishing email does not pose an immediate threat, it is essential to be cautious. Scammers may manipulate recipients into meeting their demands, leading to financial loss. Falling for such a scam can also increase the risk of repeated targeting. We strongly recommend ignoring this fraudulent email, labeling it as spam, and blocking the sender. Doing so not only protects the target but also improves anti-spam filters. Taking proactive steps to prevent such scams can deter scammers from making future phishing attempts against the individual.


Leave a Comment