“Password Was Compromised Through A Legitimate Website” email is a scam that tries attracting user attention with subjects like “Careful, it’s important.” In the message body, the scam falsely claims to have accessed personal data and threatens to leak content unless a Bitcoin payment is made.
While email is not harmful, giving in to the demands could result in financial loss. We recommended ignoring the email, marking it as spam, and blocking the sender to prevent further targeting. Let’s check out the way it operates, step by step.
What Is “Your Account Was Hacked” Email Scam?
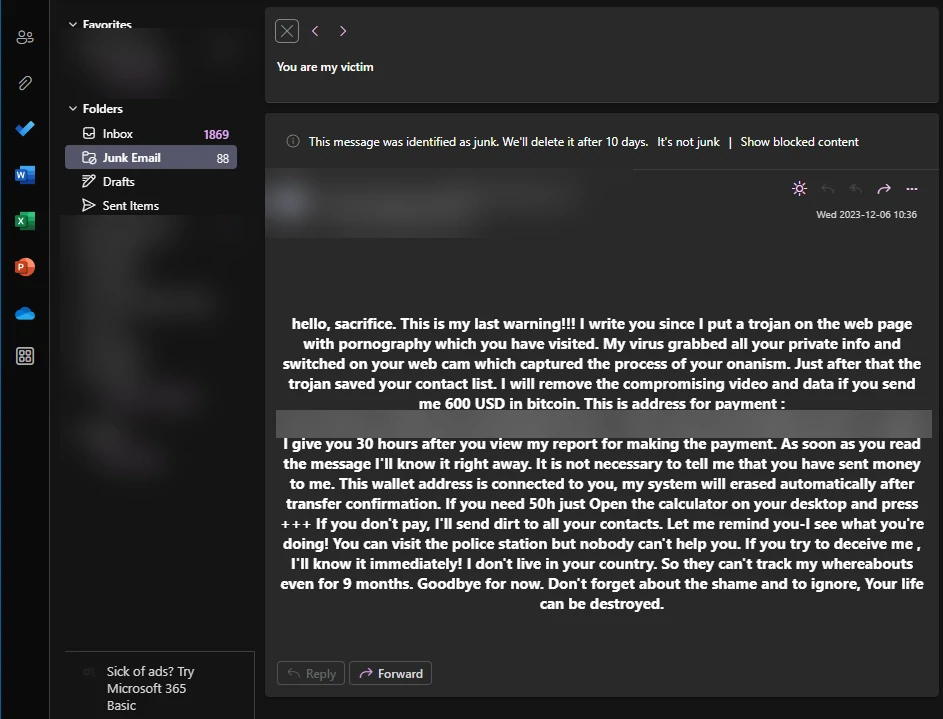
The email “Password Was Compromised Through A Legitimate Website” has been identified as spam upon thorough analysis. It is categorized as a sextortion scam, falsely asserting that the recipient’s device was infected with malware, granting unauthorized access to the microphone and camera.
“Password Was Compromised Through A Legitimate Website” Scam
| Name | “Password Was Compromised Through A Legitimate Website” Email Scam |
| Threat Type | Phishing, Scam, Social Engineering |
| Distribution methods | This scam is spread wide via spam email campaigns. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Similar Behavitor | “Some Bad News That You Are About To Hear” Email Scam, “Your Account Was Hacked” Email Scam |
How Does “Password Was Compromised Through A Legitimate Website” Scam Work?
The email, often bearing the subject “Careful, it’s important” (subject may vary), delivers a false narrative to the recipient, asserting that their email account password has been acquired through a legitimate website. According to the sender, this compromise enabled them and their team to infiltrate the account, analyze stored data, and devise an attack vector. The claimed success of this plan resulted in the alleged infection of the recipient’s device with a backdoor-type virus. This malware purportedly grants the sender access to the device’s content and control over its microphone and camera.
The email introduces a unique element by asserting the compilation of an “archive” of “exploding” videos. The lack of further details distinguishes this spam from typical sextortion scams. Yet, the implicit threat is apparent, and the vagueness likely expands the pool of potential victims. A subsequent threat in the email demands that the recorded materials will be leaked unless the recipient transfers 750 USD in Bitcoin cryptocurrency to a specified wallet address within two days. Compliance with this demand supposedly guarantees the deletion of all stolen and recorded data and the removal of the virus.
It is crucial to emphasize that all information presented in this spam email is false. No device infection, data exfiltration, or content creation has occurred. As a result, recipients should disregard the email and promptly report it as spam. Additionally, it’s noteworthy that scammers deliberately opt for cryptocurrencies in ransom demands due to their near-untraceable nature, rendering transaction reversals practically impossible.
Is It Dangerous?
The email does not present an immediate threat unless the recipient succumbs to its demands. The primary risk associated with this communication is financial loss. Furthermore, there exists a potential for an escalation in similar scams targeting the individual, given the success of the initial attempt by scammers.
As previously mentioned, we advise ignoring the email. Moreover, labeling it as spam and blocking the sender is a protective measure, not only shielding the recipient but also aiding in enhancing anti-spam filters. Proactively taking this step may act as a deterrent, dissuading scammers from persistently targeting the individual’s mailbox.


Leave a Comment