The Fastbackdata virus falls under the Phobos ransomware family. Ransomware of such sort encrypts all user’s data on the PC (images, documents, excel tables, music, videos, etc) and appends its specific extension to every file, creating the info.txt text files in every folder with the encrypted files.
What is Fastbackdata virus?
☝️ Fastbackdata is a Phobos family ransomware malicious agent.
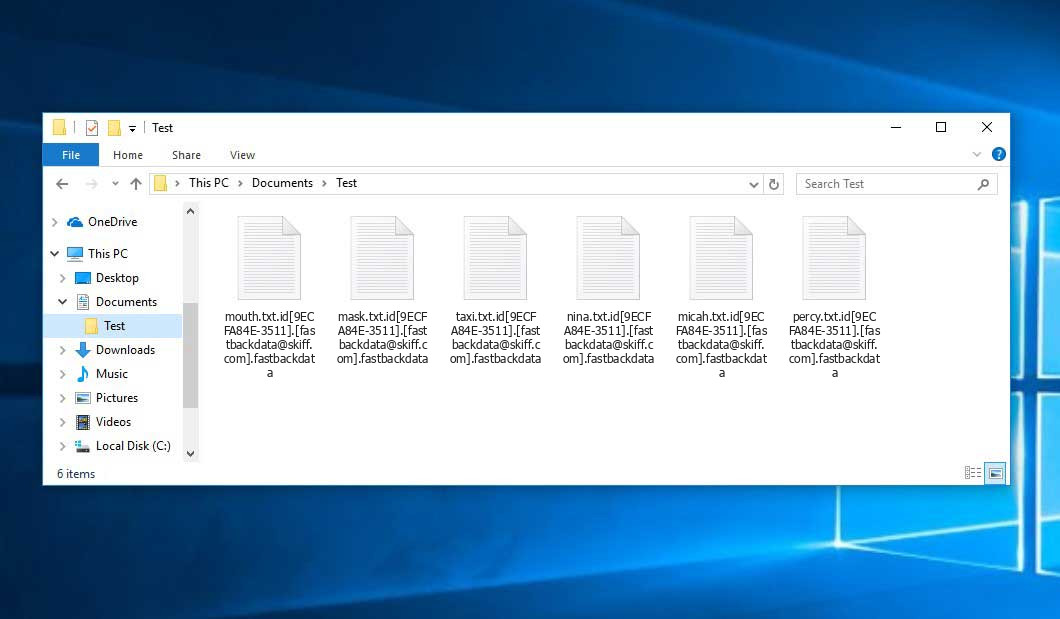
The pattern of renaming is this: id[xxxxxx].[contact_email].fastbackdata. After the encryption, a file entitled, for instance, “report.docx” will be renamed to “report.docx.id[9ECFA84E-3511].[[email protected]].fastbackdata”.
In every folder containing the encoded files, a info.txt text document will be created. It is a ransom money memo. Therein you can find information on the ways of paying the ransom and some other remarks. The ransom note usually contains instructions on how to buy the decryption tool from the racketeers. You can obtain this decrypting software after contacting [email protected] by email. That is how they do it.
Fastbackdata Overview:
| Name | Fastbackdata Virus |
| Ransomware family1 | Phobos ransomware |
| Extension | .fastbackdata |
| Ransomware note | info.txt |
| Contact | [email protected] |
| Detection | Win32/Remtasu.O Virus Removal, Trojan:Win32/BazarLoader!MSR Virus Removal, Trojan:MSIL/AgentTesla Virus Removal |
| Symptoms | Your files (photos, videos, documents) have a .fastbackdata extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Fastbackdata virus |
The info.txt file accompanying the Fastbackdata ransomware states the following:
!!! ATTENTION !!! Your network is hacked and files are encrypted. Including the encrypted data we also downloaded other confidential information: Data of your employees, customers, partners, as well as accounting and other internal documentation of your company. All data is stored until you will pay. After payment we will provide you the programs for decryption and we will delete your data We dont want did something bad to your company, it is just bussines (Our reputation is our money!) If you refuse to negotiate with us (for any reason) all your data will be put up for sale. What you will face if your data gets on the black market: 1) The personal information of your employees and customers may be used to obtain a loan or purchases in online stores. 2) You may be sued by clients of your company for leaking information that was confidential. 3) After other hackers obtain personal data about your employees, social engineering will be applied to your company and subsequent attacks will only intensify. 4) Bank details and passports can be used to create bank accounts and online wallets through which criminal money will be laundered. 5) You will forever lose the reputation. 6) You will be subject to huge fines from the government. You can learn more about liability for data loss here: hxxps://en.wikipedia.org/wiki/General_Data_Protection_Regulation hxxps://gdpr-info.eu/ Courts, fines and the inability to use important files will lead you to huge losses. The consequences of this will be irreversible for you. Contacting the police will not save you from these consequences, and lost data, will only make your situation worse. IF YOU WILL CONTACT US IN FIRST 6 hours , and we close our deal in 24 hours , PRICE WILL BE ONLY 30%. (time is money for both of us , if you will take care about our time , we will do same , we will care of price and decryption process will be done VERY FAST) ALL DOWNLOADED DATA WILL BE DELETED after payment. You can get out of this situation with minimal losses (Our reputation is our money!) !!! To do this you must strictly observe the following rules: DO NOT Modify, DO NOT rename, DO NOT copy, DO NOT move any files. Such actions may DAMAGE them and decryption will be impossible. DO NOT use any third party or public decryption software, it may also DAMAGE files. DO NOT Shutdown or Reboot the system this may DAMAGE files. DO NOT hire any third party negotiators (recovery/police, etc.) You need to contact us as soon as possible and start negotiations. You can send us 1-2 small data not value files for test , we will decrypt it and send it to you back. After payment we need no more that 2 hours to decrypt all of your data. We will be support you untill fully decryption going to be done! ! ! (Our reputation is our money!) Instructions for contacting our team: Download the (Session) messenger (hxxps://getsession.org) in messenger 0585ae8a3c3a688c78cf2e2b2b7df760630377f29c0b36d999862861bdbf93380d MAIL:[email protected]
In the picture below, you can see what a directory with files encrypted by the Fastbackdata looks like. Each filename has the “.fastbackdata” extension appended to it.
How did my computer get infected with Fastbackdata ransomware?
There are plenty of possible ways of ransomware injection.
Nowadays, there are three most exploited ways for malefactors to have the Fastbackdata virus working in your system. These are email spam, Trojan infiltration and peer networks.
- If you open your mailbox and see letters that look just like notifications from utility services providers, postal agencies like FedEx, web-access providers, and whatnot, but whose addresser is strange to you, be wary of opening those emails. They are most likely to have a harmful item attached to them. Thus it is even more dangerous to open any attachments that come with letters like these.
- Another option for ransom hunters is a Trojan file model. A Trojan is a program that infiltrates into your machine disguised as something else. Imagine, you download an installer for some program you need or an update for some service. However, what is unpacked turns out to be a harmful program that encrypts your data. As the installation package can have any name and any icon, you’d better be sure that you can trust the source of the stuff you’re downloading. The best way is to trust the software developers’ official websites.
- As for the peer-to-peer networks like BitTorrent or eMule, the danger is that they are even more trust-based than the rest of the Web. You can never guess what you download until you get it. Our suggestion is that you use trustworthy websites. Also, it is a good idea to scan the folder containing the downloaded items with the antivirus as soon as the downloading is finished.
How do I get rid of ransomware?
It is important to inform you that besides encrypting your data, the Fastbackdata virus will probably deploy Vidar Stealer on your PC to get access to credentials to different accounts (including cryptocurrency wallets). The mentioned spyware can extract your logins and passwords from your browser’s auto-filling data.
How сan I avert ransomware injection?
Fastbackdata ransomware has no endless power, neither does any similar malware.
You can protect yourself from ransomware injection in several easy steps:
- Never open any letters from unknown senders with strange addresses, or with content that has likely no connection to something you are expecting (how can you win in a lottery without participating in it?). In case the email subject is more or less something you are expecting, scrutinize all elements of the dubious email with caution. A hoax email will surely have mistakes.
- Avoid using cracked or untrusted software. Trojan viruses are often distributed as an element of cracked software, possibly under the guise of “patch” which prevents the license check. Understandably, potentially dangerous programs are difficult to tell from trustworthy software, because trojans may also have the functionality you seek. You can try to find information on this program on the anti-malware message boards, but the optimal solution is not to use such software.
Frequently Asked Questions
🤔 Is it possible to open “.fastbackdata” files?
Unfortunately, no. You need to decipher the “.fastbackdata” files first. Then you will be able to open them.
🤔 What should I do to make my files accessible as fast as possible?
If the “.fastbackdata” files contain some really important information, then you probably have them backed up. In case you haven’t, there is still a chance that you do have a Restore Point from some time ago to roll back the whole system to the moment when it had no virus yet, but already had your files. The rest of the methods require patience.
🤔 What actions should I take if the Fastbackdata malware has blocked my PC and I can’t get the activation key.
🤔 And what should I do now?
Many of the encoded files might still be within your reach
- If you exchanged your critical files by email, you could still download them from your online mail server.
- You might have shared photographs or videos with your friends or relatives. Simply ask them to give those images back to you.
- If you have initially downloaded any of your files from the Internet, you can try downloading them again.
- Your messengers, social networks pages, and cloud drives might have all those files too.
- Maybe you still have the needed files on your old PC, a laptop, phone, external storage, etc.
USEFUL TIP: You can employ file recovery programs2 to get your lost data back since ransomware blocks the copies of your files, deleting the authentic ones. In the tutorial below, you can see how to use PhotoRec for such a restoration, but remember: you can do it only after you remove the virus with an anti-malware program.


Leave a Comment