Spectating the Trojan:Win32/Tnega.BQ!MTB detection name means that your computer is in big danger. This malware can correctly be named as ransomware – virus which ciphers your files and forces you to pay for their decryption. Stopping it requires some unusual steps that must be taken as soon as possible.
Trojan:Win32/Tnega.BQ!MTB detection is a virus detection you can spectate in your system. It often shows up after the preliminary activities on your PC – opening the dubious e-mail messages, clicking the advertisement in the Web or mounting the program from suspicious resources. From the moment it appears, you have a short time to act before it starts its malicious action. And be sure – it is much better not to wait for these malicious things.
What is Trojan:Win32/Tnega.BQ!MTB virus?
Trojan:Win32/Tnega.BQ!MTB is ransomware-type malware. It looks for the files on your disk drives, encrypts it, and after that asks you to pay the ransom for receiving the decryption key. Besides making your files inaccessible, this malware also does a lot of damage to your system. It changes the networking settings in order to prevent you from looking for the removal guides or downloading the anti-malware program. In some cases, Trojan:Win32/Tnega.BQ!MTB can also stop the launching of anti-malware programs.
Trojan:Win32/Tnega.BQ!MTB Summary
In total, Trojan:Win32/Tnega.BQ!MTB virus activities in the infected PC are next:
- SetUnhandledExceptionFilter detected (possible anti-debug);
- Behavioural detection: Executable code extraction – unpacking;
- Yara rule detections observed from a process memory dump/dropped files/CAPE;
- Presents an Authenticode digital signature;
- Creates RWX memory;
- Dynamic (imported) function loading detected;
- Enumerates the modules from a process (may be used to locate base addresses in process injection);
- CAPE extracted potentially suspicious content;
- Unconventionial language used in binary resources: Arabic (Algeria);
- The binary likely contains encrypted or compressed data.;
- Authenticode signature is invalid;
- CAPE detected the RedLine malware family;
- Anomalous binary characteristics;
- Ciphering the files located on the victim’s drive — so the victim cannot check these documents;
- Blocking the launching of .exe files of security tools
- Blocking the launching of installation files of anti-virus programs
Ransomware has been a headache for the last 4 years. It is hard to realize a more hazardous virus for both individual users and businesses. The algorithms used in Trojan:Win32/Tnega.BQ!MTB (typically, RHA-1028 or AES-256) are not hackable – with minor exclusions. To hack it with a brute force, you need to have more time than our galaxy actually exists, and possibly will exist. However, that virus does not do all these unpleasant things instantly – it may require up to several hours to cipher all of your files. Therefore, seeing the Trojan:Win32/Tnega.BQ!MTB detection is a clear signal that you need to start the elimination procedure.
Where did I get the Trojan:Win32/Tnega.BQ!MTB?
Ordinary ways of Trojan:Win32/Tnega.BQ!MTB spreading are usual for all other ransomware examples. Those are one-day landing websites where users are offered to download the free app, so-called bait emails and hacktools. Bait emails are a pretty modern method in malware spreading – you get the e-mail that imitates some normal notifications about deliveries or bank service conditions modifications. Within the e-mail, there is an infected MS Office file, or a link which leads to the exploit landing site.

Malicious email message. This one tricks you to open the phishing website.
Avoiding it looks fairly uncomplicated, however, still demands a lot of focus. Malware can hide in various spots, and it is far better to stop it even before it invades your system than to depend on an anti-malware program. Standard cybersecurity awareness is just an essential item in the modern world, even if your interaction with a PC remains on YouTube videos. That can keep you a great deal of time and money which you would spend while searching for a fixing guide.
Trojan:Win32/Tnega.BQ!MTB malware technical details
File Info:
name: DB694ECB88E56C3479DA.mlwpath: /opt/CAPEv2/storage/binaries/ff6cf494a9a9267ced583a5305c89bc0f3f5931d2b3fbc189e89c84379b40388crc32: EFB1F514md5: db694ecb88e56c3479da20a68c6f521esha1: a2c44812c65780bc35600573c5cb63e0dc676864sha256: ff6cf494a9a9267ced583a5305c89bc0f3f5931d2b3fbc189e89c84379b40388sha512: 9c9c9ce5d22a63cd657d6e66d3ca375ad16c7cce598e1954899e8c35768a41e883d5838902f52f86f9e03998467006242d814f2eec47b0e083c0049685efeaa9ssdeep: 6144:EgDwrm5/AHf6s8TxLIGmiE418rrpbvRmWOtdk6rb6H9mb92KtLsu:J8dys8VLZmi18npbpmhtdL6H900KZsutype: PE32 executable (console) Intel 80386, for MS Windowstlsh: T15794BF10A7A0C035F5F356F45AF9A269BA3E7AA16B2490CF53D41AE95B30AD1FC30317sha3_384: 4585720ef528dd4c8efa3b8442a51dc680394063cdc7edb7368faed920773be652b221dd9ff94d398f77ba9ce49c34fcep_bytes: 8bff558bece8b6610000e8110000005dtimestamp: 2021-04-16 02:28:26Version Info:
Translation: 0x0151 0x0013
Trojan:Win32/Tnega.BQ!MTB also known as:
| Elastic | malicious (high confidence) |
| MicroWorld-eScan | Gen:Variant.Mikey.129520 |
| FireEye | Generic.mg.db694ecb88e56c34 |
| ALYac | Gen:Variant.Mikey.129520 |
| Cylance | Unsafe |
| K7AntiVirus | Riskware ( 00584baa1 ) |
| K7GW | Riskware ( 00584baa1 ) |
| Cyren | W32/Kryptik.FMD.gen!Eldorado |
| Symantec | Packed.Generic.620 |
| ESET-NOD32 | a variant of Win32/Kryptik.HMWZ |
| TrendMicro-HouseCall | TROJ_GEN.R06CC0DJH21 |
| ClamAV | Win.Trojan.Generic-9904323-0 |
| Kaspersky | HEUR:Trojan-Spy.Win32.Stealer.gen |
| BitDefender | Gen:Variant.Mikey.129520 |
| SUPERAntiSpyware | Trojan.Agent/Gen-Kryptik |
| Avast | Win32:RansomX-gen [Ransom] |
| Ad-Aware | Gen:Variant.Mikey.129520 |
| Emsisoft | Gen:Variant.Mikey.129520 (B) |
| Baidu | Win32.Trojan.Kryptik.jm |
| TrendMicro | TROJ_GEN.R06CC0DJH21 |
| McAfee-GW-Edition | Packed-GDT!DB694ECB88E5 |
| Sophos | Troj/Krypt-DI |
| Ikarus | Trojan.Win32.Crypt |
| Jiangmin | TrojanSpy.Stealer.fza |
| Avira | TR/Crypt.ZPACK.cgdlo |
| Microsoft | Trojan:Win32/Tnega.BQ!MTB |
| GData | Gen:Variant.Mikey.129520 |
| Cynet | Malicious (score: 100) |
| AhnLab-V3 | Trojan/Win.Azorult.R445459 |
| Acronis | suspicious |
| McAfee | Packed-GDT!DB694ECB88E5 |
| MAX | malware (ai score=80) |
| VBA32 | BScope.Backdoor.Agent |
| Malwarebytes | Trojan.MalPack.GS |
| APEX | Malicious |
| Rising | Trojan.Kryptik!1.DA12 (CLASSIC) |
| SentinelOne | Static AI – Malicious PE |
| MaxSecure | Trojan.Malware.121218.susgen |
| Fortinet | W32/Kryptik.HMYI!tr |
| AVG | Win32:RansomX-gen [Ransom] |
| Panda | Trj/GdSda.A |
| CrowdStrike | win/malicious_confidence_90% (W) |
How to remove Trojan:Win32/Tnega.BQ!MTB?
Trojan:Win32/Tnega.BQ!MTB malware is incredibly difficult to erase manually. It places its documents in several locations throughout the disk, and can restore itself from one of the parts. Furthermore, countless modifications in the windows registry, networking settings and also Group Policies are really hard to find and revert to the original. It is far better to use a special tool – exactly, an anti-malware tool. GridinSoft Anti-Malware will definitely fit the best for virus removal objectives.
Why GridinSoft Anti-Malware? It is very light-weight and has its detection databases updated nearly every hour. In addition, it does not have such bugs and weakness as Microsoft Defender does. The combination of these facts makes GridinSoft Anti-Malware perfect for taking out malware of any kind.
Remove the viruses with GridinSoft Anti-Malware
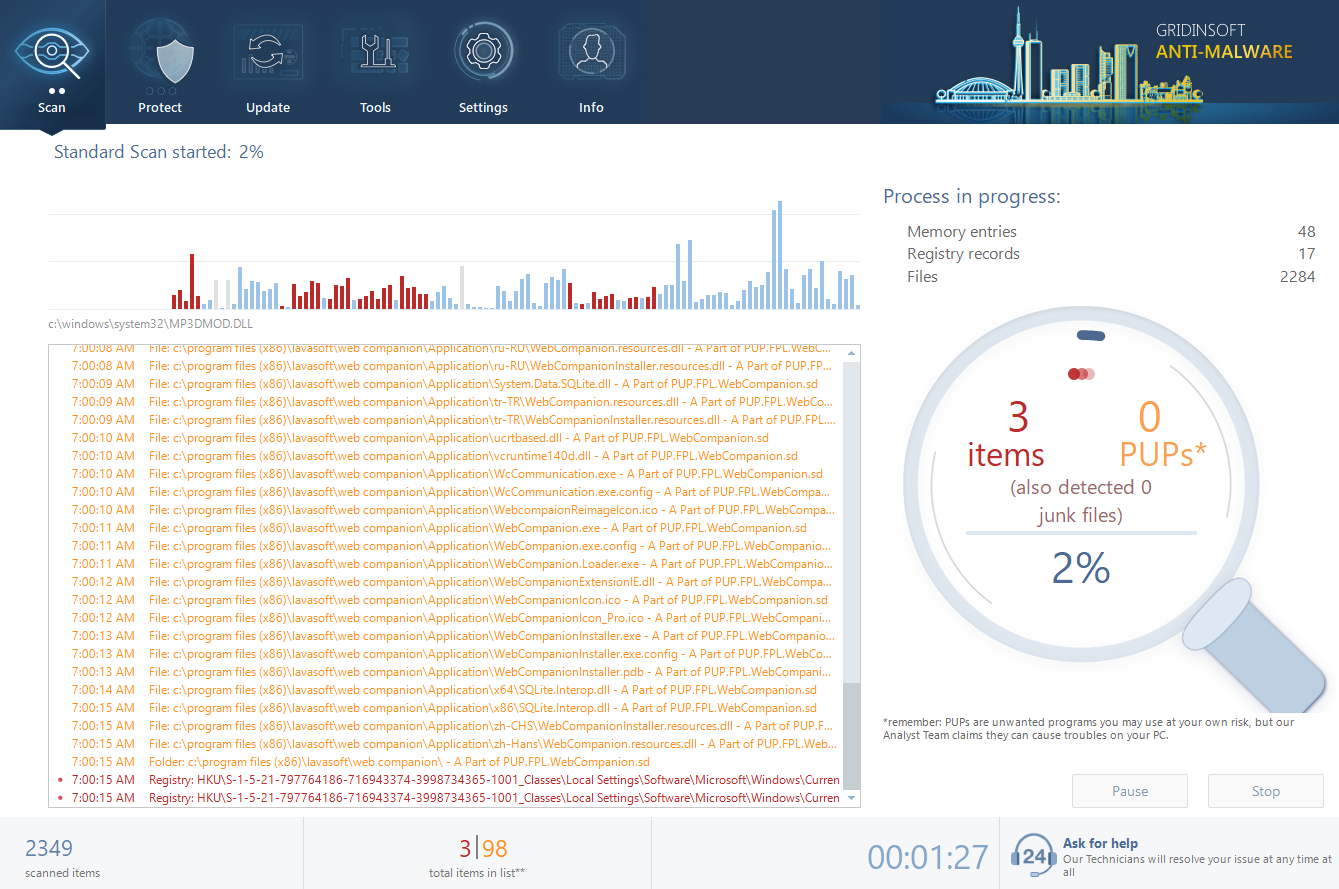
- Download and install GridinSoft Anti-Malware. After the installation, you will be offered to perform the Standard Scan. Approve this action.
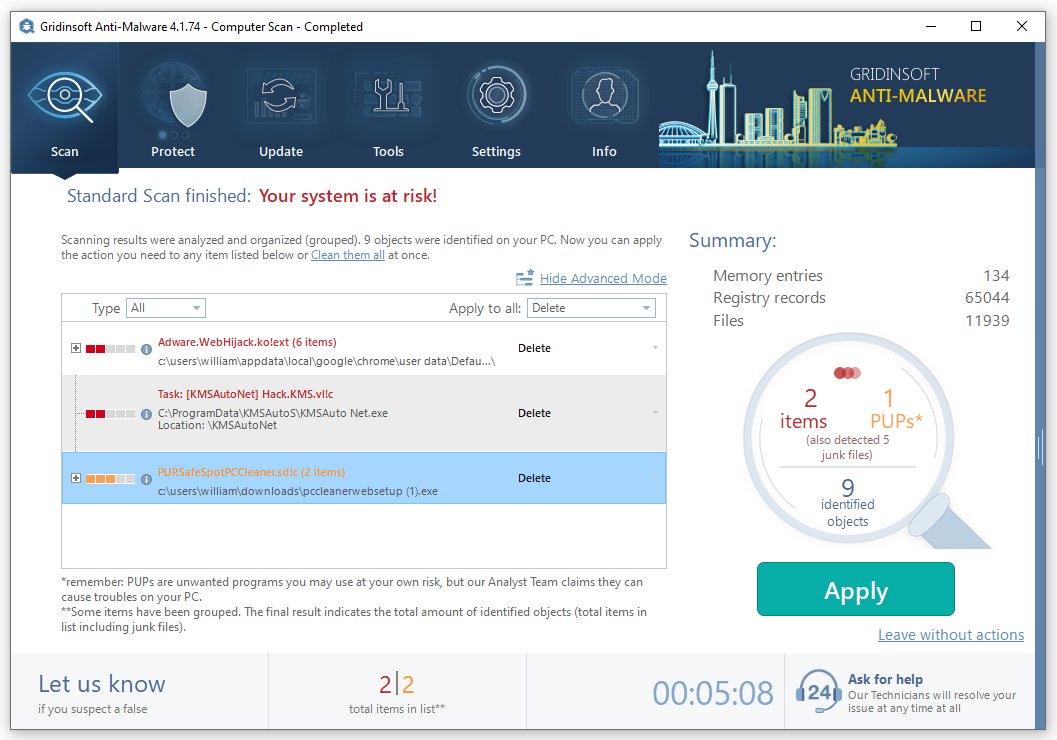
- Standard scan checks the logical disk where the system files are stored, together with the files of programs you have already installed. The scan lasts up to 6 minutes.
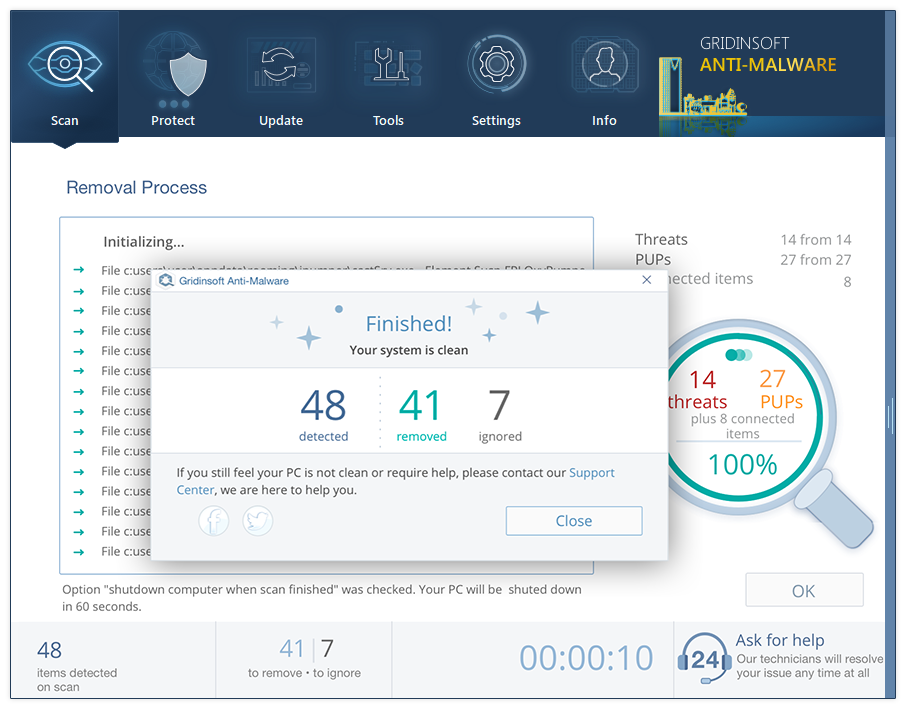
- When the scan is over, you may choose the action for each detected virus. For all files of [SHORT_NAME] the default option is “Delete”. Press “Apply” to finish the malware removal.

![What is the Win32:Evo-gen [Trj] virus?](https://howtofix.guide/wp-content/uploads/2019/11/trojan-ransom-1140x760.jpg)
