If you spectate the alert of Trojan:Win32/Sabsik.TE.A!ml detection, it appears that your computer has a problem. All malicious programs are dangerous, with no exceptions. Sabsik is a virus that aims at ciphering your files and asking to pay the ransom to get the files back. Simply put, Trojan:Win32/Sabsik.TE.A!ml detection means that your system is in a big hazard.
Any malware exists with the only target – make money on you. And the programmers of these things are not thinking of morality – they use all possible tactics. In this case, they do not care about stealing your data or exploiting your hardware to mine cryptocurrencies. Sabsik malware ciphers your files, and then leaves ransom notes asking for up to $4000 for their decryption.
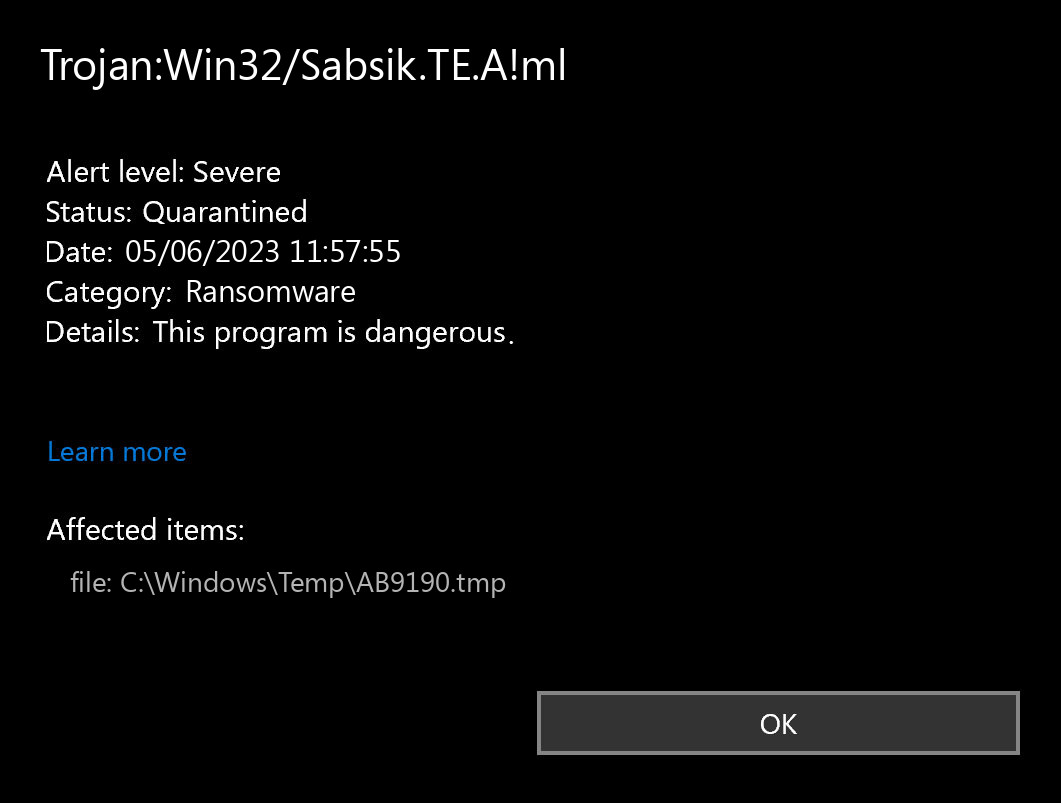
What does the notification with Trojan:Win32/Sabsik.TE.A!ml detection mean?
The Trojan:Win32/Sabsik.TE.A!ml detection you can see in the lower right corner is displayed to you by Microsoft Defender. That anti-malware program is quite OK at scanning, however, prone to be mainly unstable. It is unprotected to malware attacks, it has a glitchy interface and problematic malware removal capabilities. Thus, the pop-up which states about the Sabsik is simply an alert that Defender has actually recognized it. To remove it, you will likely need to make use of a separate anti-malware program.
The exact Trojan:Win32/Sabsik.TE.A!ml infection is a really unpleasant thing. It is present inside of your system disguised as a part of something benevolent, or as a part of the program you have got on a forum. Then, it makes all possible steps to weaken your system. At the end of this “party”, it downloads other malicious things – ones which are wanted by cyber burglars who manage this virus. Hence, it is impossible to predict the effects from Sabsik actions. And the unpredictability is one of the baddest things when we are talking about malware. That’s why it is rather not to choose at all, and don’t let the malware to complete its task.
Threat Summary:
| Name | Sabsik Ransomware |
| Detection | Trojan:Win32/Sabsik.TE.A!ml |
| Details | Sabsik is attached to another program (such as a document), which can replicate and spread after an initial execution. |
Is Trojan:Win32/Sabsik.TE.A!ml dangerous?
As I have pointed out previously, non-harmful malware does not exist. And Trojan:Win32/Sabsik.TE.A!ml is not an exclusion. This virus alters the system settings, edits the Group Policies and registry. All of these components are vital for proper system operating, even when we are not talking about Windows security. Therefore, the virus which Sabsik carries, or which it will inject after some time, will squeeze out maximum revenue from you. Cyber burglars can steal your data, and then sell it at the black market. Using adware and browser hijacker functions, built in Trojan:Win32/Sabsik.TE.A!ml virus, they can make profit by showing you the ads. Each view gives them a penny, but 100 views per day = $1. 1000 victims who watch 100 banners per day – $1000. Easy math, but sad conclusions. It is a bad choice to be a donkey for crooks.
How did I get this virus?
It is hard to trace the sources of malware on your computer. Nowadays, things are mixed, and spreading ways chosen by adware 5 years ago can be utilized by spyware nowadays. But if we abstract from the exact spreading tactic and will think of why it works, the answer will be pretty simple – low level of cybersecurity understanding. Individuals press on promotions on odd sites, open the pop-ups they get in their web browsers, call the “Microsoft tech support” thinking that the weird banner that says about malware is true. It is important to understand what is legit – to prevent misconceptions when trying to determine a virus.
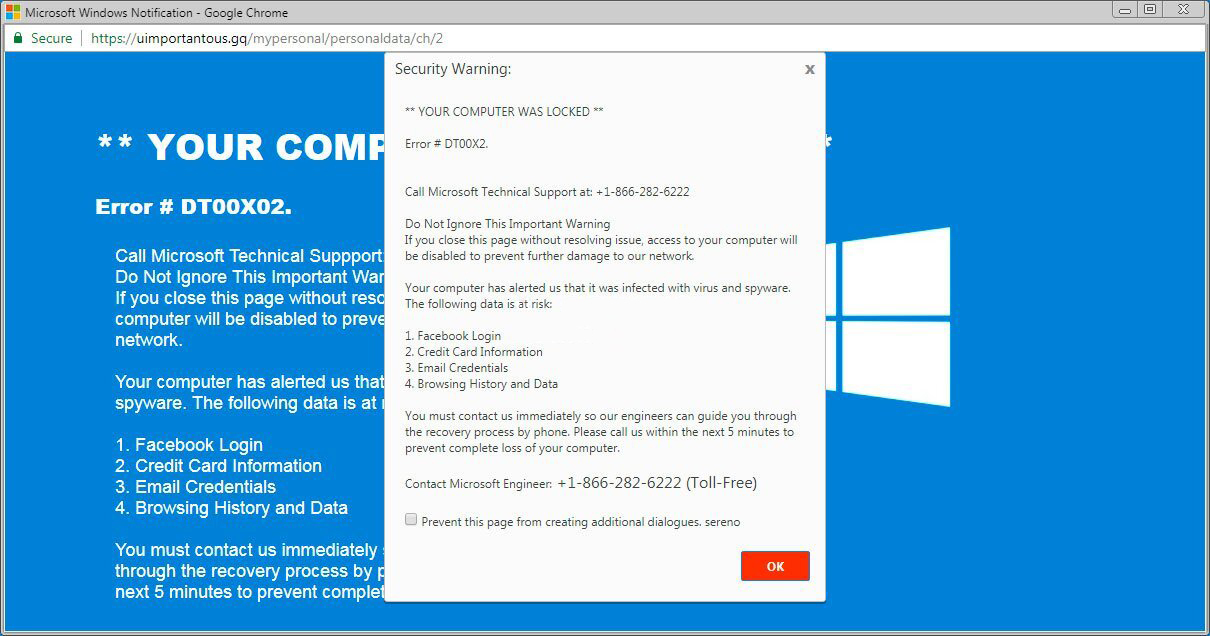
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most widespread methods of malware distribution – bait e-mails and also injection into a hacked program. While the first one is not so easy to evade – you must know a lot to understand a fake – the 2nd one is simple to solve: just don’t utilize cracked applications. Torrent-trackers and other providers of “free” applications (which are, exactly, paid, but with a disabled license checking) are just a giveaway place of malware. And Trojan:Win32/Sabsik.TE.A!ml is just one of them.


Leave a Comment