The Trojan:Win32/CobaltStrike!pz detection, is a sign that your PC has a problem. Allowing it to run may end up with some really bad consequences. CobaltStrike grants the criminals access to your system, or even connects it to the botnet.
Backdoors like CobaltStrike are flexible viruses that may act as self-sufficient malware, or be used in multi-stage attacks. Their primary target is creating a remote control point to the target system, that operates without the owner’s concent. To prevent any interruptions, backdoor tries to stay as stealthy as possible.
Trojan:Win32/CobaltStrike!pz Detection Overview
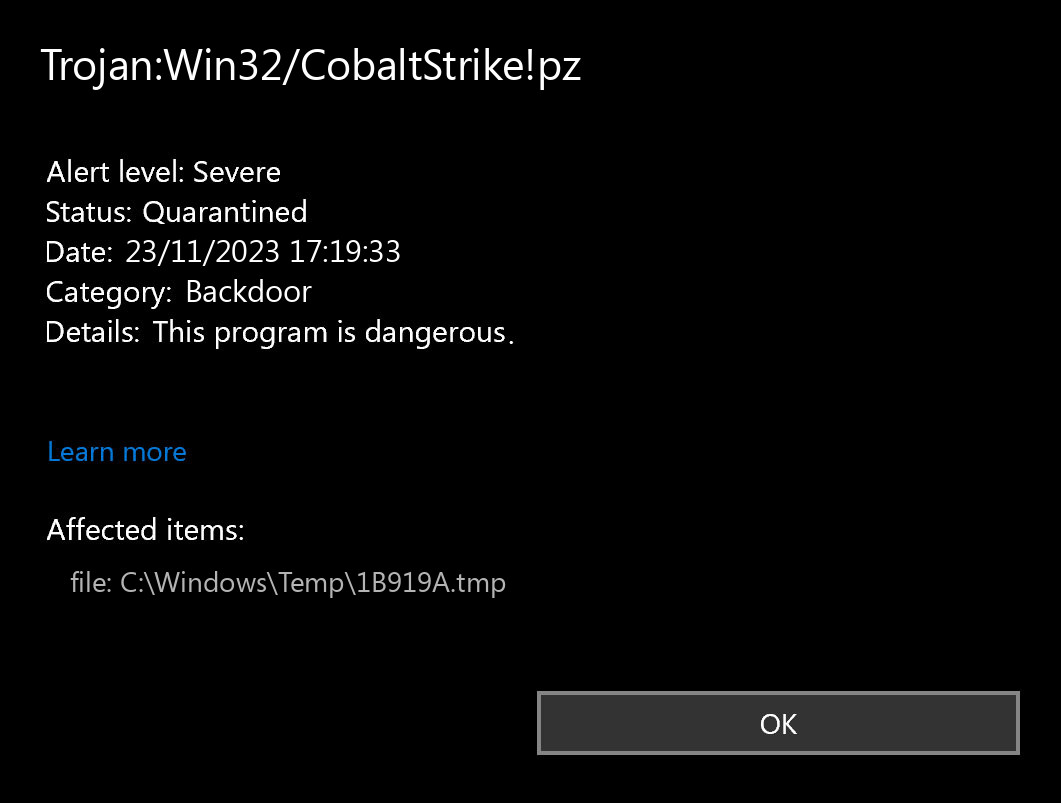
The Trojan:Win32/CobaltStrike!pz detection you can see in the lower right corner is demonstrated to you by Microsoft Defender. That anti-malware application is pretty good at scanning, however, prone to be mainly unreliable. It is unprotected to malware invasions, it has a glitchy user interface and bugged malware clearing capabilities. For this reason, the pop-up which states concerning the CobaltStrike is just a notification that Defender has actually detected it. To remove it, you will likely need to use another anti-malware program.
Backdoor Summary:
| Name | CobaltStrike Backdoor |
| Detection | Trojan:Win32/CobaltStrike!pz |
| Damage | Gain access to the operating system to perform various malicious actions. |
| Similar | Worm Alcan, Msil Quasar, Cur Malware, Trojan Msil Mamut, Hupigon, Luadream Malware, Pysilon Rat Malware, Sponsor Malware |
| Fix Tool | See If Your System Has Been Affected by CobaltStrike backdoor |
Shortly about backdoors
Backdoors are viruses that can acquire both separated and built-in shapes. Once you can uncover that a legitimate program from a well-known company has a functionality that makes it possible for someone to connect to your system. Will it be someone from the developers or a third party – no one knows. But the scandal when this detail is detected in an official program is probably impossible to miss. There is also chatter that there is a hardware-based backdoor in Intel CPUs1.
Is Trojan:Win32/CobaltStrike!pz dangerous?
As I have stated before, non-harmful malware does not exist. And Trojan:Win32/CobaltStrike!pz is not an exclusion. This backdoor does not deal a lot of harm exactly after it introduces. However, it will likely be a very unpleasant surprise when a random discussion forum or site in the Web will not let you in, because your IP-address is disallowed after the DDoS attack. However, even if it is not crucial for you – is it nice at all to realize that somebody can easily access your PC, read your discussions, open your files, as well as spectate what you do?
The spyware that is commonly present as a supplement to the Trojan:Win32/CobaltStrike!pz virus will be just another reason to remove it as fast as you can. Nowadays, when users’ information is priced incredibly high, it is too goofy to give the crooks such an opportunity. Even worse if the spyware will in some way manage to take your banking information. Seeing 0 on your bank account is the worst headache, in my thoughts.
References
- Gossip about the backdoor in Intel processors on Reddit.


Leave a Comment