Sponsor malware, primarily distributed through Microsoft Exchange server vulnerabilities, infiltrates systems with ease.
Sponsor Backdoor collects host information and communicates with a central server. Its versatile capabilities include executing commands from operators, downloading and running files, and adjusting communication intervals. This malware’s wide-ranging infiltration methods and potent functionality make it a noteworthy threat.
Sponsor Backdoor Overview
Sponsor malware, categorized as a backdoor, is a malicious software variant with a notable presence in cyberattacks across various sectors such as healthcare, manufacturing, retail, insurance, communications, and telecommunications. This malware is notably coded using the C++ programming language, which allows it to establish unauthorized access to compromised systems, making it a significant cybersecurity concern for organizations across diverse industries.
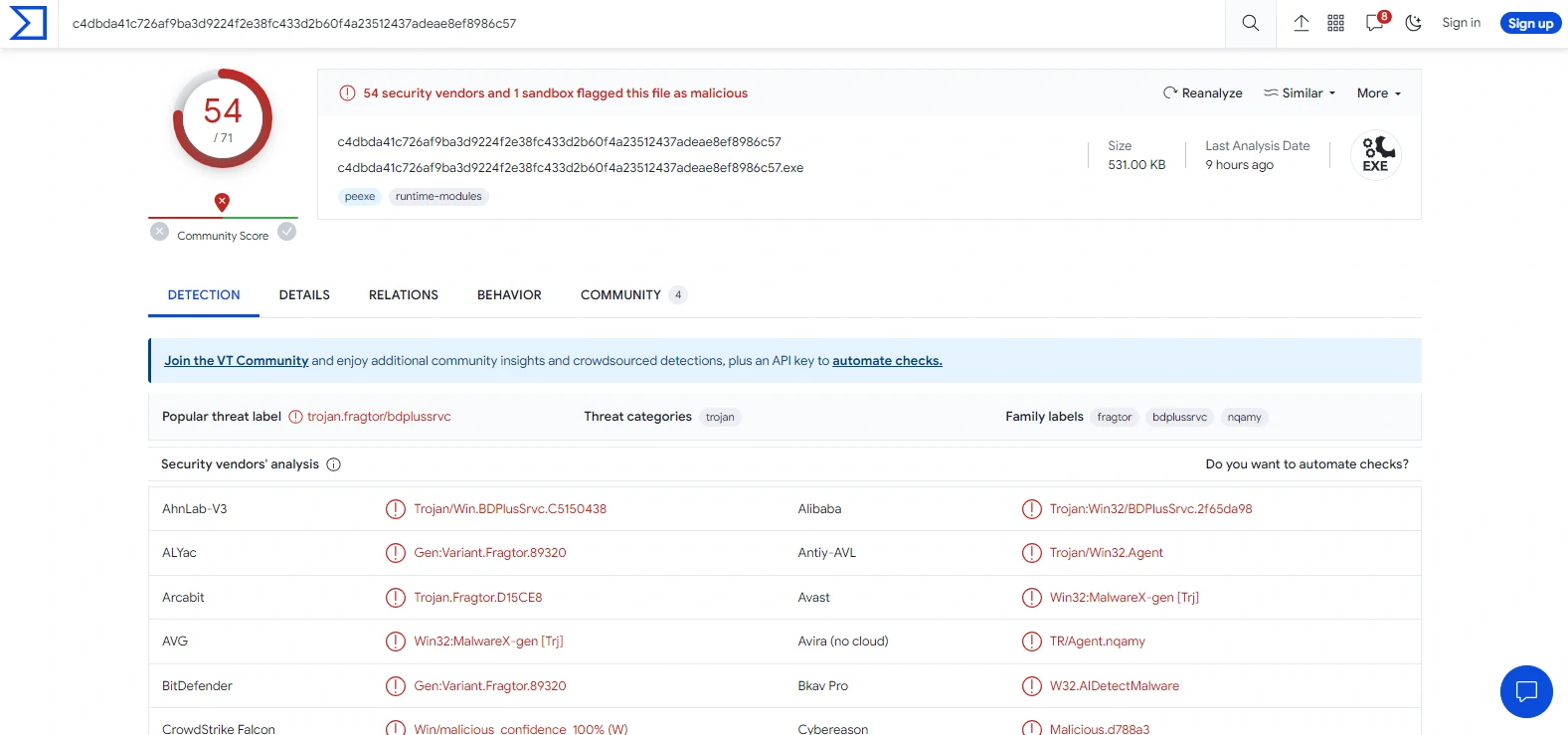
Sponsor backdoor on Virus Total
| Name | Sponsor |
| Detection | Microsoft (Trojan:Win32/BDPlusSrvc.B!dha), Gridinsoft (Trojan.Win32.Agent.dd!s1) |
| Symptoms | Backdoor malware typically is designed to stealthily infiltrate the victim’s computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Vulnerability in Miccrosoft Exchange servers. Other possible channels include infected email attachments, malicious online advertisements, social engineering, and software ‘cracks’. |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet, additional infections, monetary loss, data encryption, and more. |
| Similar Behavior | Redsip, CSBeacon, BitRat |
Technical Analysis of Sponsor
Sponsor, as a type of malware, carries out various tasks upon receiving specific commands from its operator. These tasks include providing its process ID to the operator, executing designated commands on the infected host and relaying the results, accepting and executing files sent by the operator, and downloading and executing files from the internet.
Additionally, Sponsor can execute a script to uninstall the malware, enter a sleep mode for a specified duration before reconnecting with the operator, and modify the check-in interval for communication with the operator.
Spreading methods
Sponsor malware gains access by exploiting a known vulnerability in Microsoft Exchange servers. This well-documented security flaw has been exploited by cybercriminals as a gateway for initial access. Once successfully exploited, it provides these attackers with a foothold on compromised systems, enabling the deployment and activation of the Sponsor backdoor.
Other potential infection vectors include malicious attachments or links in phishing emails, malicious ads, drive-by downloads from compromised websites, or the delivery of infected files through social engineering techniques. These tactics leverage human vulnerabilities, deceiving users into unwittingly installing the malware on their systems.


Leave a Comment