Cur malware, a sophisticated threat, spreads primarily through targeted malspam campaigns. It often arrives disguised as innocuous archives, exploiting the DLL side-loading technique.
Once inside a system, Cur malware can lead to data theft, privacy breaches, financial losses, and system compromises. It’s noteworthy for its precision-targeted attacks, posing significant dangers to organizations and individuals alike.
Cur Malware Overview
The Cur malware group, a cluster of malicious programs, comprises software that exhibits minimal commonalities among its members. Notably, there are no discernible code similarities. These programs, however, are linked through a common infrastructure, and indications point to their association with a Chinese-affiliated cyber-espionage group known as ToddyCat.
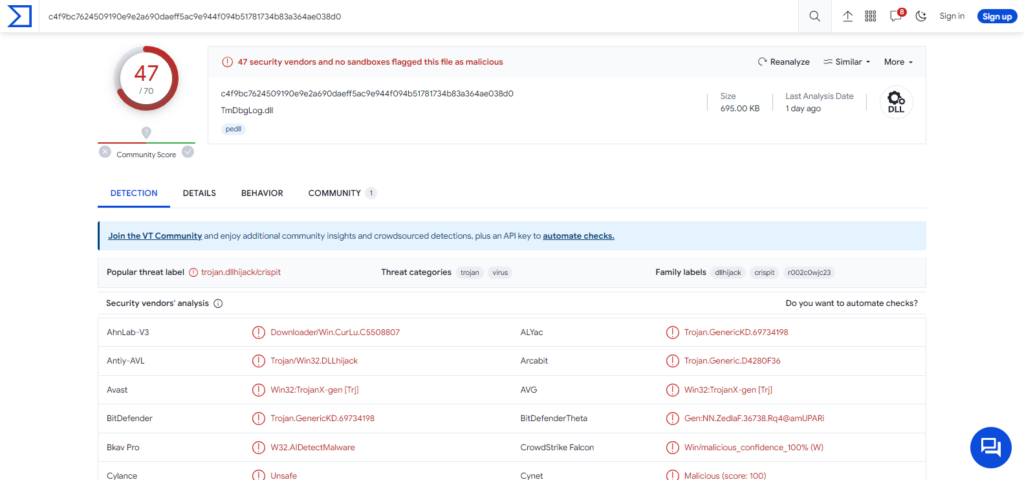
CurKeep malware on Virus Tortal site
At the time of this report, the Cur malware family is actively employed in an ongoing campaign referred to as “Stayin’ Alive,” which has been operational since at least 2021. This operation primarily targets Asia, with a focus on countries like Kazakhstan, Uzbekistan, Pakistan, and Vietnam. The attacks are directed at the telecommunications sector and entities with connections to government bodies.
| Name | Cur |
| Threat Type | Trojan, backdoor, loader. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software ‘cracks’. |
| Detection | Microsoft (Trojan:Win32/Injector!MSR) |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet. |
Technical Analysis of Cur Malware
Indications suggest that these programs are designed to be easily disposable due to their high specialization and limited versatility.
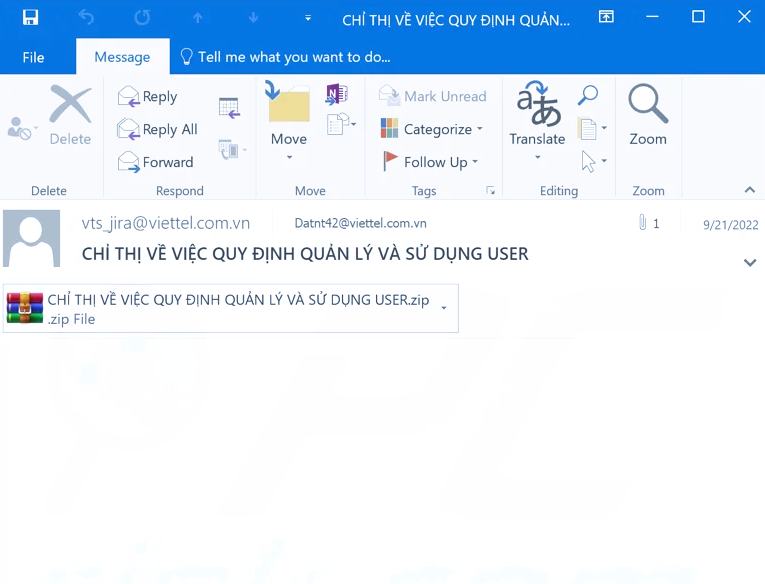
Screenshot of a spam email used to distribute CurKeep
CurKeep is a lightweight backdoor program, with a mere 10KB in size, typical of this malware group. Once installed, it promptly transmits fundamental device data to its Command and Control (C&C) server. Following this, the malware remains in a state of readiness to receive commands.
CurKeep has been disseminated through various archives, including:
- “QForm V8.zip”: This archive masquerades as “QForm,” professional engineering software employed for simulating metal forming processes.
- “Саммит 2022 г (парол – 0809).rar”: Translating to “Summit 2022 (password – 0809).rar,” this file, albeit in Russian, originated from Uzbekistan.
- “Приказ №83 от 29.05.2023г.rar”: This Russian archive signifies “Order No. 83 from 29/05/2023,” with “order” indicating a command or instruction. The date format is in DD/MM/YYYY, and it traces back to Kazakhstan.
CurLu, a loader in the Cur malware family, primarily functions to fetch payloads from its C&C server. It’s frequently associated with the “Stayin’ Alive” campaign. While many infections involve the DLL side-loading technique, it’s not exclusive to this method.
CurLog, another loader within the Cur family, serves the purpose of downloading and installing payloads. Multiple variants of CurLog exist. Like most Cur programs, it’s propagated through DLL side-loading. An instance includes an archive named “Compatible Products – Vector ver7.1.1.zip,” which contains an executable with the same filename. This ZIP archive was submitted from Kazakhstan.
CurCore, on the other hand, is a lightweight backdoor that likely plays a role in initial reconnaissance and payload delivery. CurCore possesses the capability to read and create files, copy their contents, encode the information, and transmit it to the C&C server. Furthermore, it can receive and execute commands as directed.
High-risk infections typically lead to reduced system performance or complete system failure, data loss, grave privacy breaches, financial setbacks, and the risk of identity theft. The perils escalate significantly when such malware is deployed against highly sensitive entities, a characteristic that aptly describes the Cur group.
Spreading methods
Cur malware is considered dangerous. While the level of danger can vary depending on the specific variant and how it’s used, Cur malware and related programs can pose significant threats to computer systems and data.
Cur malware infiltrates computers primarily through the following methods:
-
Malspam
Cur malware is actively disseminated via targeted spam emails. These emails often carry archive file attachments. These archives frequently contain seemingly legitimate software executables that leverage the DLL side-loading technique to introduce the Cur malware. In some cases, researchers have even discovered Cur malware archives hosted on portals used by them. - Diverse File Types and Methods
Cur malware can also be distributed using various other file types and techniques. Malicious files can be in formats such as ZIP, RAR, executables (e.g., .exe, .run), documents (PDF, Microsoft Office, Microsoft OneNote), JavaScript, and more.
In a broader context of malware distribution, common methods include:
- Phishing attacks and social engineering techniques are widespread and often involve convincing individuals to click on malicious links or open malicious attachments.
- These can be delivered via emails, private messages, direct messages, SMS messages, and so on.
- Stealthy and deceptive downloads occur when users unknowingly download malicious content while visiting a website.
- Malware can be distributed through sources like freeware websites, free file-hosting platforms, Peer-to-Peer sharing networks, and similar channels.
- Cybercriminals employ various online scams to trick users into downloading and executing malicious software.
Understanding these distribution methods is critical for preventing Cur malware and other threats from infiltrating computer systems.


Leave a Comment