Solan is a potent Python-based malware, that uses a wide range of spreading methods to propagate itself into the system. These include malicious downloads, deceptive links, and infected email attachments.
Once inside, it stealthily targets sensitive data within browsers, mainly at session cookies and stored passwords. Its insidious actions compromise user privacy, leading to potential identity theft, fraud, and unauthorized access to online accounts. Solan’s multifaceted approach underscores the importance of robust cybersecurity measures.
Solan Stealer Overview
Solan is an infostealer malware written in Python. It is distinctive for its stealthy operations in extracting sensitive data from diverse sources, including web browsers and social media platforms such as Facebook. Additionally, Solan focuses on a browser extension linked to cryptocurrency activities.
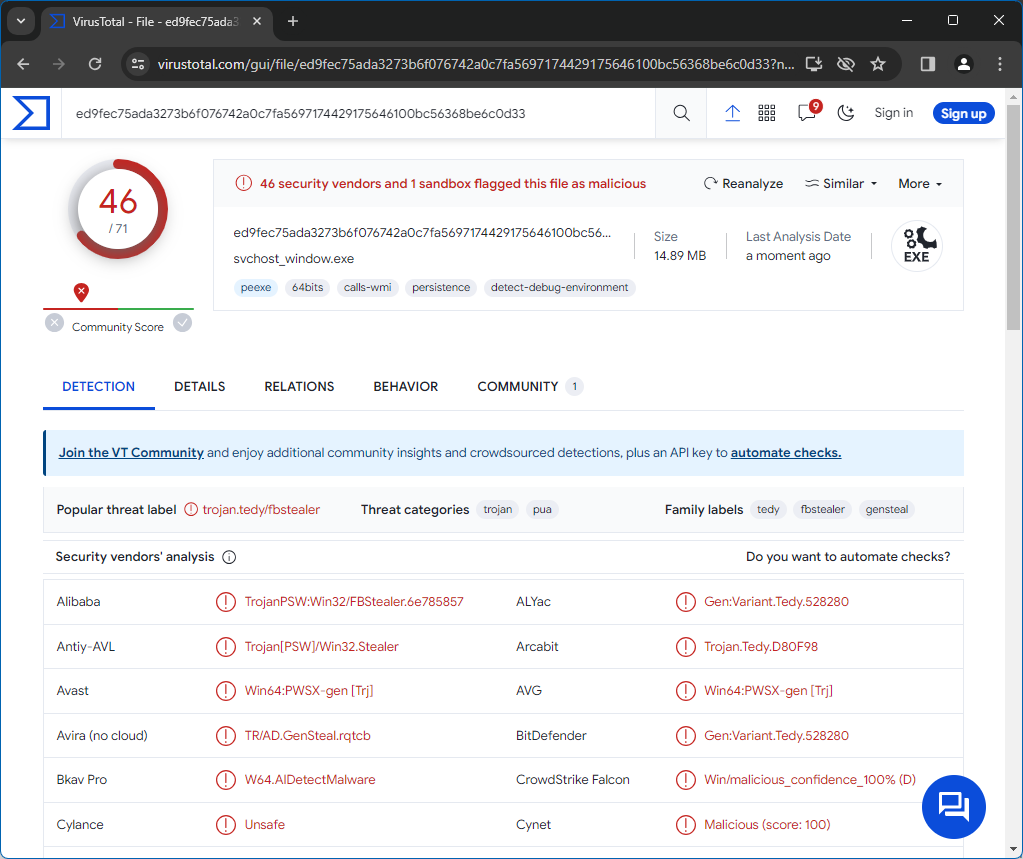
Solan Stealer on VirusTotal
| Name | Solan information stealer |
| Threat Type | Stealer |
| Detection | Trojan:Win32/Wacatac.B!ml (Microsoft) |
| Damage | Stolen passwords and cookies, identity theft, monetary loss, compromised online accounts, and more. |
| Similar Behavior | Rage Stealer, WhiskerSpy |
Technical Analysis
Solan employs a multifaceted strategy for data theft, focusing on extracting sensitive information stored within targeted browsers. Among its primary goals is the pilfering of cookies and passwords. By targeting session cookies, Solan seeks to exploit the authentication tokens and user session data contained within these files. Session cookies are essential for maintaining user sessions across websites, facilitating seamless authentication and interaction.
In the hands of cybercriminals, these cookies can be exploited to impersonate users, bypass login screens, and gain unauthorized access to online accounts. Access to stored passwords enables Solan to compromise user accounts across various online platforms, including email, social media, and financial services. This covert data theft undermines user privacy and poses significant risks of identity theft, fraud, and unauthorized access to sensitive information.
Furthermore, Solan extends its reach beyond traditional browser data theft by targeting social media platforms like Facebook. With access to Facebook data, Solan can harvest personal information such as user profiles, friends lists, and private messages. This data can be abused for malicious purposes, including identity theft, fraud, and social engineering attacks. In addition to social media platforms, Solan targets MetaMask, a popular cryptocurrency wallet software. MetaMask enables users to manage Ethereum-based assets and interact with decentralized applications on the Ethereum blockchain.
By infiltrating MetaMask, Solan accesses users’ cryptocurrency holdings, private keys, and transaction histories. This poses a significant risk to individuals involved in cryptocurrency trading and investment, potentially leading to substantial financial losses and compromising the security of digital assets. An infection with Solan can result in severe consequences, including theft of sensitive information, compromised online accounts, financial fraud, degraded system performance, and potential loss of cryptocurrency assets.
Spreading Methods
Solan can infiltrate your computer through various channels, often exploiting unsuspecting user behavior. Users may inadvertently download malicious files or software, such as pirated software, from untrustworthy websites. Clicking on malicious links or advertisements, opening infected email attachments, or using infected USB drives or other removable media can also facilitate malware infection.
Moreover, malware like Solan can exploit vulnerabilities in outdated software or operating systems to gain unauthorized access to your device. It can be distributed through a range of file types, including executable files (.exe), script files (.bat, .vbs), document files (.doc, .xls), compressed files (.zip, .rar), and even image files (.jpg, .png).


Leave a Comment