Rage Stealer is an infostealer malware, notorious for its stealthy infiltration methods. It excels in exfiltrating sensitive data, notably login credentials, and can pilfer from over ten types of cryptocurrency wallets.
Its capability to spread via local networks and removable devices further amplifies its danger, making it a formidable tool for cybercriminals seeking financial gain and data theft. Let me explain the malware functionality in details, and also show the way to remove it from the system.
Rage Malware Overview
Rage infostealer, also recognized under the names RageStealer and xStealer, is a malicious program that aims at exfiltrating various categories of data from the infected device. Initially known as Priv8, it underwent rebranding and emerged as Rage in the summer of 2023. The primary function of this malicious software is to pilfer data, focusing on login credentials such as usernames and passwords.
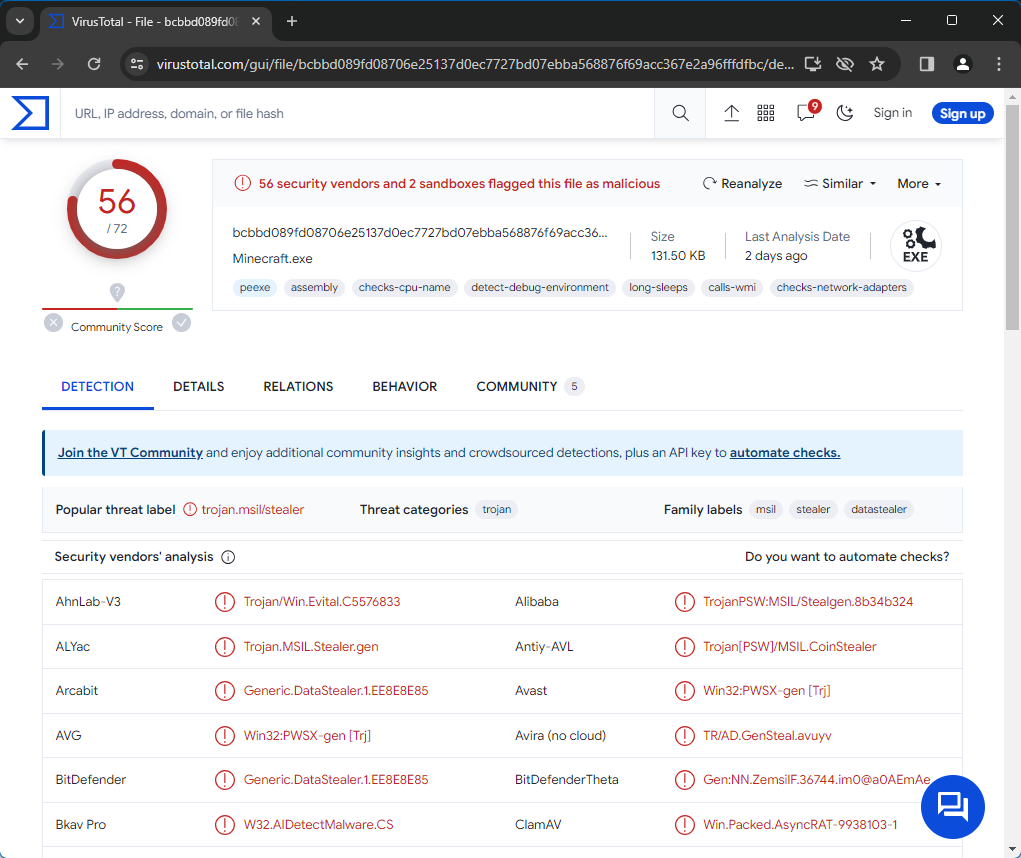
Rage malware on VirusTotal
| Name | Rage malware |
| Threat Type | Trojan, stealer, password-stealing virus. |
| Detection | Trojan.Win32.Packed.sa, PWS:MSIL/Stealgen.GA!MTB |
| Damage | Exploits your hardware to mine cryptocurrencies without your permission. |
| Similar Behavitor | S1deload Stealer, NightClub |
Technical Analysis
This stealer can hijack information from more than a dozen cryptocurrency wallets. It can also siphon off internet cookies and save passwords from Chrome-based internet browsers. Beyond login details and cookies, Rage seeks to capture tokens, session data, profiles, and other critical information. Rage’s targets include messaging apps, VPNs (Virtual Private Networks), FTP (File Transfer Protocol) clients, and gaming software, among others (see the complete list below). The malware is even equipped to take screenshots.
It’s important to note that the developers of Rage are continuously updating the malware, potentially expanding its list of targets or enhancing its functionalities in future versions. But even now, the infiltration of devices by malware like Rage can result in system compromises, significant privacy breaches, financial damages, and risks of identity theft.
Spreading Methods
Cybercriminals often deploy phishing and social engineering tactics to spread malware like Rage. Common strategies include deceptive downloads without the user’s knowledge, harmful attachments or links in unsolicited emails, private or direct messages, and text messages, as well as malvertising and online fraud. Unreliable sources for downloading content, such as sites offering freeware, file-hosting services, peer-to-peer sharing networks, and illegal software ‘cracks’ and counterfeit updates, are also frequent culprits.
Furthermore, malicious software can propagate across local networks and through removable storage devices like external hard drives and USB flash drives. Malware often masquerades as legitimate software or media files, adopting various forms such as compressed archives (like RAR and ZIP files), executable files (.exe, .run, etc.), documents (including PDFs and Microsoft Office files), and JavaScript files. When one of these infected files is activated, opened, or executed, the malware begins infiltrating.
How To Remove Malware?
While it’s possible to remove malware manually, I advise against it. In its quest for permanence, malware duplicates itself, complicating tracking all its components. Hence, manual removal can be time-consuming and often inefficient.


Leave a Comment