So Avast or AVG just popped up with something called “IDP.HEUR.26” and now you’re panicking. Take a breath. This is just a fancy way of saying “our algorithm thinks this might be suspicious but we’re not entirely sure.”
The “IDP” part stands for “Identity Protection,” which is just Avast’s way of saying they’re watching how files behave rather than what they look like. “HEUR” means they’re using heuristics – basically making educated guesses based on patterns. The “26” is just their internal code for this specific type of detection.
Here’s the kicker – half the time these alerts are false alarms. Discord, Adobe Acrobat, and even machine learning tools like LM Studio regularly get flagged with this warning. It’s like that friend who thinks every stomach ache is appendicitis.
Of course, actual malware exists for one reason – to make money off you. These aren’t charity programmers writing code for fun. They want your data, your processing power, or to bombard you with ads. Nobody enjoys being someone’s digital cash cow.
What’s With That IDP.HEUR.26 Pop-up?
I’ve relocated the files to quarantine on numerous occasions, but they keep reappearing. Is there any possibility that this file could pose any genuine threat?from reddit
That pop-up is Avast or AVG throwing a fit in your corner. While they’re decent at scanning, they’re also drama queens of the antivirus world. The notification basically says “we found something,” but doesn’t actually do much about it. You’ll likely need another program to handle the dirty work.
When it’s not a false positive, IDP.HEUR.26 is basically a digital parasite. It sneaks in disguised as something legitimate – maybe that “free” Photoshop you downloaded from a sketchy forum. Then it starts inviting its friends over to trash your digital house. The unpredictability is what makes it annoying to deal with.
Threat Summary:
| Name | IDP.HEUR.26 |
| Details | A heuristic detection by Avast/AVG that flags potentially suspicious behavior. Often triggers false positives with legitimate software like Discord, Adobe products, and various development tools. |
| Fix Tool | See If Your System Has Been Affected by IDP.HEUR.26 Trojan |
Is This Thing Actually Dangerous?
Let’s be honest – there’s no such thing as friendly malware. If it’s real (big if), IDP.HEUR.26 messes with system settings, group policies, and your Windows registry. These aren’t just random parts of your computer – they’re the instruction manual that keeps everything running. It’s like someone rearranging all the furniture in your house while you’re sleeping.
Real infections want to squeeze every penny possible from your system. They grab personal data to sell, show you ads for profit, or use your computer to mine cryptocurrency. A thousand infected users seeing 100 ads a day equals $1000 in the hacker’s pocket. Simple math, depressing result.
But remember – the Reddit threads are full of people getting this warning while using perfectly legitimate software. Discord users, Adobe Acrobat installers, and developers using LM Studio have all been falsely accused. It’s like getting arrested because you “look suspicious.”
How Did This Thing Get On My Computer?
If it’s a real infection (again, big if), it probably got in because someone clicked something they shouldn’t have. We all have moments of weakness – that flashing download button, that email attachment from a “bank,” or that popup claiming your computer has 847 viruses. Low cybersecurity awareness is the digital equivalent of leaving your front door wide open.
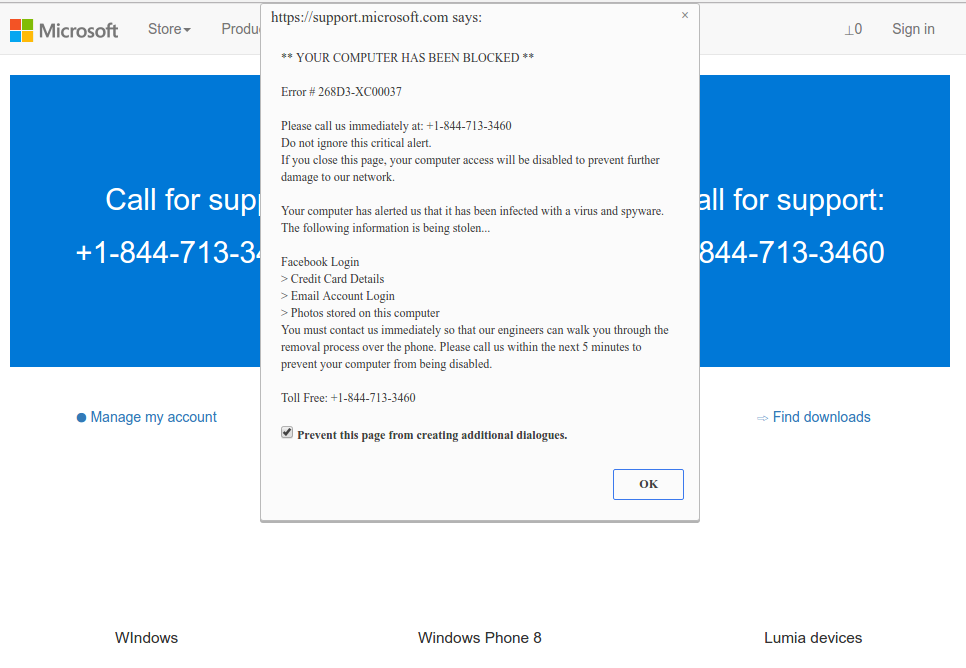
The classic “Microsoft” tech support scam – about as real as a $3 bill
The two main highways for malware are phishing emails and cracked software. Spotting fake emails takes practice, but avoiding cracked software is simple – just don’t do it. Those “free” Photoshop downloads from torrent sites come with unwanted roommates. Nothing in life is truly free, especially not expensive software.
But if you’re seeing this alert after installing Discord, Adobe products, or developer tools like LM Studio, you’re probably looking at a false positive. One GitHub issue reports LM Studio getting flagged simply because it uses Chromium, which shows how trigger-happy these detections can be.
How Do I Get Rid of This Thing?
First, determine if it’s real or a false alarm. If you just installed Discord, Adobe software, or other legitimate applications, try submitting a false positive report to Avast/AVG. Their community support forums confirm they’ll whitelist legitimate software that’s incorrectly flagged.
If you suspect it’s a genuine infection, manual removal is like performing surgery with oven mitts. Malware spreads its files everywhere and makes registry changes that are hard to track down. A dedicated anti-malware program like GridinSoft Anti-Malware is your best bet for thorough cleanup.
When in doubt, get a second opinion. If Avast/AVG is your only source saying something is wrong, try scanning with a different security tool. Multiple Reddit users reported that other antivirus programs found nothing wrong with the same files AVG was panicking about.
Remove IDP.HEUR.26 with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Trojans as shown from our tests with the software, and we assure you that it can remove IDP.HEUR.26 as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “IDP.HEUR.26” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing IDP.HEUR.26 and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Avast Detections
- IDP.HEUR.26 Malware: A Complete Removal Guide
- URL:Scam
- IDP.ALEXA.54 Dangerous or Avast (AVG) False Positive?
- IDP.Generic Malware ✔️ Avast IDP Generic Detection
- Win32:BogEnt Virus (Avast Detection)
- Win32:Trojan-gen Avast Virus
- URL:Phishing Avast Virus Detection: What Is It?
- URL:TechScam Avast Virus (TechScam Detection)
- URL:Blacklist (Blacklisted URL) Avast Detection
- IDP.HEUR.24 Virus Detection by Avast
How to Remove IDP.HEUR.26 Virus
Name: IDP.HEUR.26
Description: Avast or AVG just popped up with something called "IDP.HEUR.26" and now you're panicking. Take a breath. This is just a fancy way of saying "our algorithm thinks this might be suspicious but we're not entirely sure." The "IDP" part stands for "Identity Protection," which is just Avast's way of saying they're watching how files behave rather than what they look like. "HEUR" means they're using heuristics – basically making educated guesses based on patterns. The "26" is just their internal code for this specific type of detection.
Operating System: Windows
Application Category: Trojan

