Enigma Stealer, a multi-stage threat, showcases a sophisticated progression in its deployment. It commences by downloading, deobfuscating, and executing secondary and tertiary payloads. The malware’s ultimate form, Stage 4, emerges as an adept information gatherer.
It captures a broad spectrum of sensitive data, including user credentials, tokens, and passwords from renowned browsers and applications like Google Chrome, Microsoft Edge, and Telegram. This intricate process underscores Enigma Stealer’s proficiency in pilfering extensive digital footprints.
Enigma Stealer Overview
Enigma is an information stealer emerged in early 2023. Being a derivative of an open-source Stealerium Stealer, Enigma includes functionality of stealer, clipper and keylogger. Another legacy feature of this malware is the use of Telegram API for connecting to the C2 server.
Functionally, the Enigma stealer operates with the primary objective of extracting valuable insights from a designated system. It goes a step further by compromising critical information, including tokens, passwords, and usernames, from a diverse array of sources. Noteworthy targets encompass prominent platforms such as Google Chrome, Microsoft Edge, Microsoft Outlook, Telegram, Signal, and OpenVPN, among others.
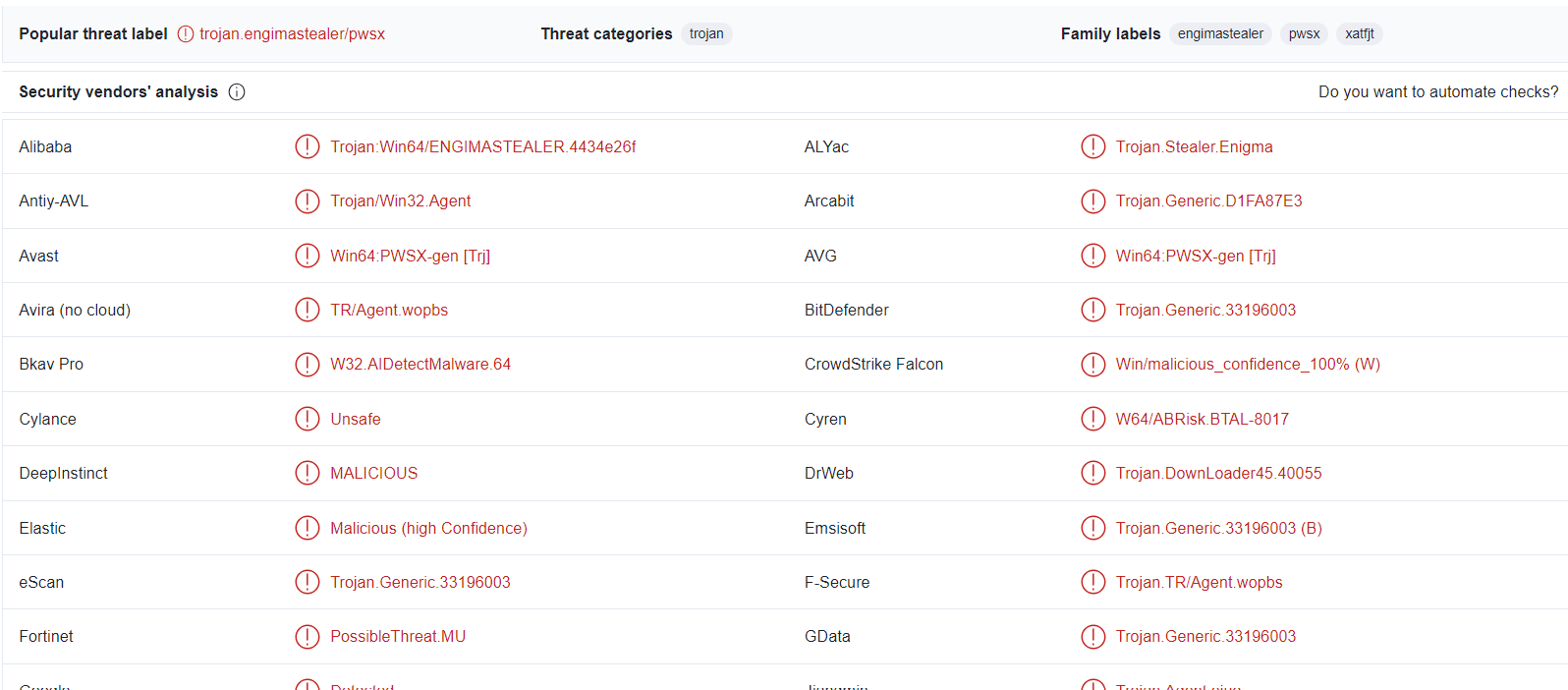
| Name | Enigma Stealer |
| Detection | TrojanSpy:Win32/Stealer!MSR (VirusTotal page) |
| Similar Behavior | S1deload, StealDeal |
| Damage | Exploits your hardware to mine cryptocurrencies without your permission. |
| Fix Tool | See If Your System Has Been Affected by Enigma Stealer Virus |
Technical analysis of Enigma Stealer
Contrary to other mass-market stealers, Enigma is a multi-stage malware. It’s initial phase is often latched within a file with double-extension trick (.docx.exe or the like). This is a C++-crafted downloader for the following stage. Its fundamental purpose is the sequential execution of downloading, deobfuscating, decompressing, and activating the second-stage payload. The malware adeptly employs an array of strategies aimed at evading detection and confounding reverse engineering endeavors. These tactics encompass API hashing, string encryption, and obfuscation through superfluous code inclusion.
Upon activation, the malware initiates the establishment of a mutual exclusion object (mutex) to establish its presence within the system. Simultaneously, it retrieves the MachineGuid associated with the compromised system from the SOFTWARE\Microsoft\Cryptography\MachineGuid registry entry. This MachineGuid serves as a distinctive identifier, crucial for the malware’s registration of the infected system on its command and control (C&C) server, thereby enabling ongoing monitoring of the infection’s progress.
Stage 2
In order to get the 2nd stage payload, the malware initiates an interesting sequence. It starts by dispatching a request to a Telegram channel under the control of the attacker, utilizing the URL https://api[.]telegram[.]org/bot{token}/getFile to retrieve the specific file_path. This approach is advantageous, rendering the attacker capable of consistent updates while eschewing the need for reliance on fixed filenames. Upon successful completion of the file’s retrieval, along with subsequent deobfuscation and decompression processes, the malware transmits the “bot getted” message to the designated debug server.
At its core, this malware harbors a primary objective: incapacitating Microsoft Defender. It achieves this by orchestrating the deployment of a noxious kernel mode driver, employing the “bring your own vulnerable driver” (BYOVD) methodology. This entails the exploitation of a vulnerability residing within an Intel driver (CVE-2015-2291). This tactical maneuver facilitates the subsequent download and execution of the third-stage payload.
Stage 3 and 4
The inception of the Stage 3 is marked by the introduction of a dedicated downloader module. This module shoulders the responsibility of downlading, decompressing, and executing the final stealer payload within the compromised environment. Notably, the malware remains amenable to commands conveyed through a designated Telegram channel, although the specifics of these commands might exhibit variations across distinct iterations.
Upon initiation, the malware promptly dispatches a “Bot started” message to both the Debug server and the designated Telegram channel. This communication serves as a confirmation of its successful launch. Then, it pulls and runs the Stage 4 payload from the C2.
Stage 4 is an actual Enigma Stealer in its final form. Its outset involves an intricate process of amassing comprehensive system details, thereafter progressing to the extraction of critical user data. The spectrum of pilfered information encompasses user details, tokens, and passwords sourced from an array of prominent web browsers and applications. Among the targeted platforms are Google Chrome, Microsoft Edge, Microsoft Outlook, Telegram, Signal, and OpenVPN, to name a few.
This advanced iteration of Enigma Stealer extends its capabilities further by capturing screenshots and extracting content from the clipboard, in addition to acquiring VPN configurations. This holistic approach underscores the malware’s sophisticated design, enabling it to amass a wealth of sensitive information for the malevolent actor’s benefit.
Spreading ways of Enigma Stealer
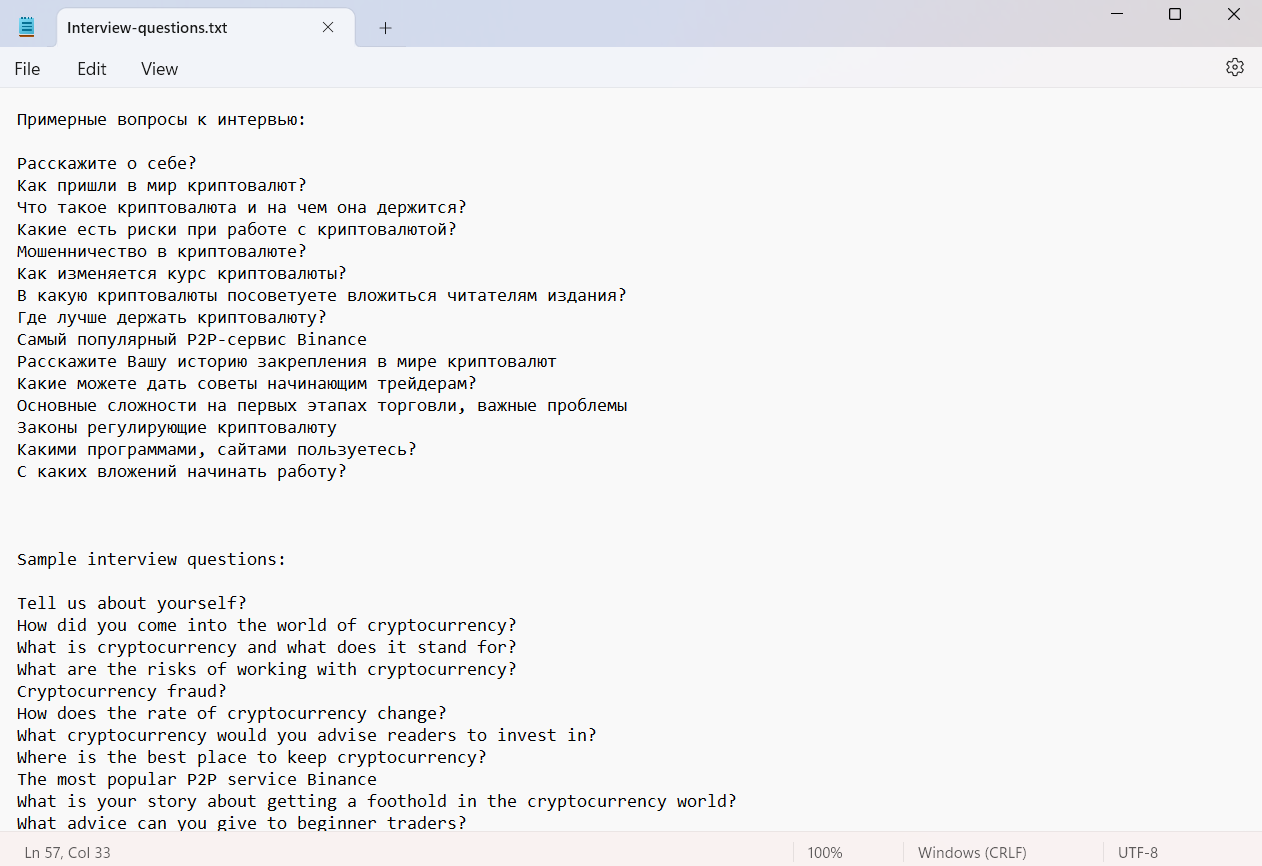
Enigma Stealer dissemination employs a malicious RAR archive dispatched via phishing emails or social media platforms. This archive encompasses “Interview questions.txt” and “Interview conditions.word.exe,” with file names subject to variation. The latter is an executable, beguiling recipients into activating the loader, resulting in Enigma information stealer contamination of their systems. The .txt version of the file looks like this:
Remove Enigma Stealer with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Stealers as shown from our tests with the software, and we assure you that it can remove Enigma Stealer as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “Enigma Stealer” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing Enigma Stealer and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Frequently Asked Questions (FAQ)
Reformatting your storage device should only be considered as a last resort for removing Enigma Stealer malware. Prior to taking such drastic action, it is advisable to perform a comprehensive scan using trustworthy antivirus or anti-malware software.
Malware poses a significant risk to the security and privacy of sensitive information, potentially leading to identity theft, financial loss, and unauthorized access to personal accounts. Furthermore, it can disrupt the normal operation of a system, causing performance issues, system crashes, and data corruption.
The purpose of Enigma Stealer is to enable remote access and control of compromised devices. It allows threat actors to perform various malicious activities, such as unauthorized access, data theft, system manipulation, and disabling security measures, potentially causing significant harm to individuals and organizations.
Gridinsoft Anti-Malware has the ability to identify and eliminate most malware infections. Nevertheless, it is crucial to recognize that sophisticated malware can remain hidden deep within the system. Consequently, conducting a complete system scan is imperative to detect and eradicate malware.
How to Remove Enigma Stealer Malware
Name: Enigma Stealer
Description: Enigma Stealer unfolds as a multi-stage threat, employing intricate deployment tactics. It initiates with the execution of subsequent payloads, orchestrated through downloading, deobfuscating, and activation processes. In its final iteration, Stage 4 emerges as a formidable data aggregator. It systematically harvests a wealth of sensitive information, encompassing user credentials, tokens, passwords, and more. This comprehensive data-gathering approach spans prominent platforms such as Google Chrome, Microsoft Edge, and Telegram. Enigma Stealer underscores its sophistication by meticulously acquiring and compromising extensive digital footprints, solidifying its status as a potent information theft instrument.
Operating System: Windows
Application Category: Malware