DBatLoader, also known as ModiLoader, spreads through deceptive email campaigns, often masquerading as trusted shipping services. Once executed, it unleashes a barrage of malicious activities, from bypassing security measures to injecting shellcode payloads.
DBatLoader Malware empowers cybercriminals with the ability to monitor victims’ actions, record keystrokes, capture screens, and even gain full control of infected systems. Its versatility in delivering various payloads, including ransomware and banking trojans, makes it a significant threatin the ever-evolving cyber landscape.
DBatLoader Malware Overview
DBatLoader, also recognized as ModiLoader, represents a malware variation engineered for the purpose of downloading and executing the primary payload associated with prevalent malware activities. These activities primarily involve information theft malware or remote access tools (RATs) such as Remcos, Warzone, FormBook, or AgentTesla.
The dissemination of DBatLoader is typically instigated via malicious emails. Notably, these campaigns leverage cloud services to prime and retrieve additional payloads.
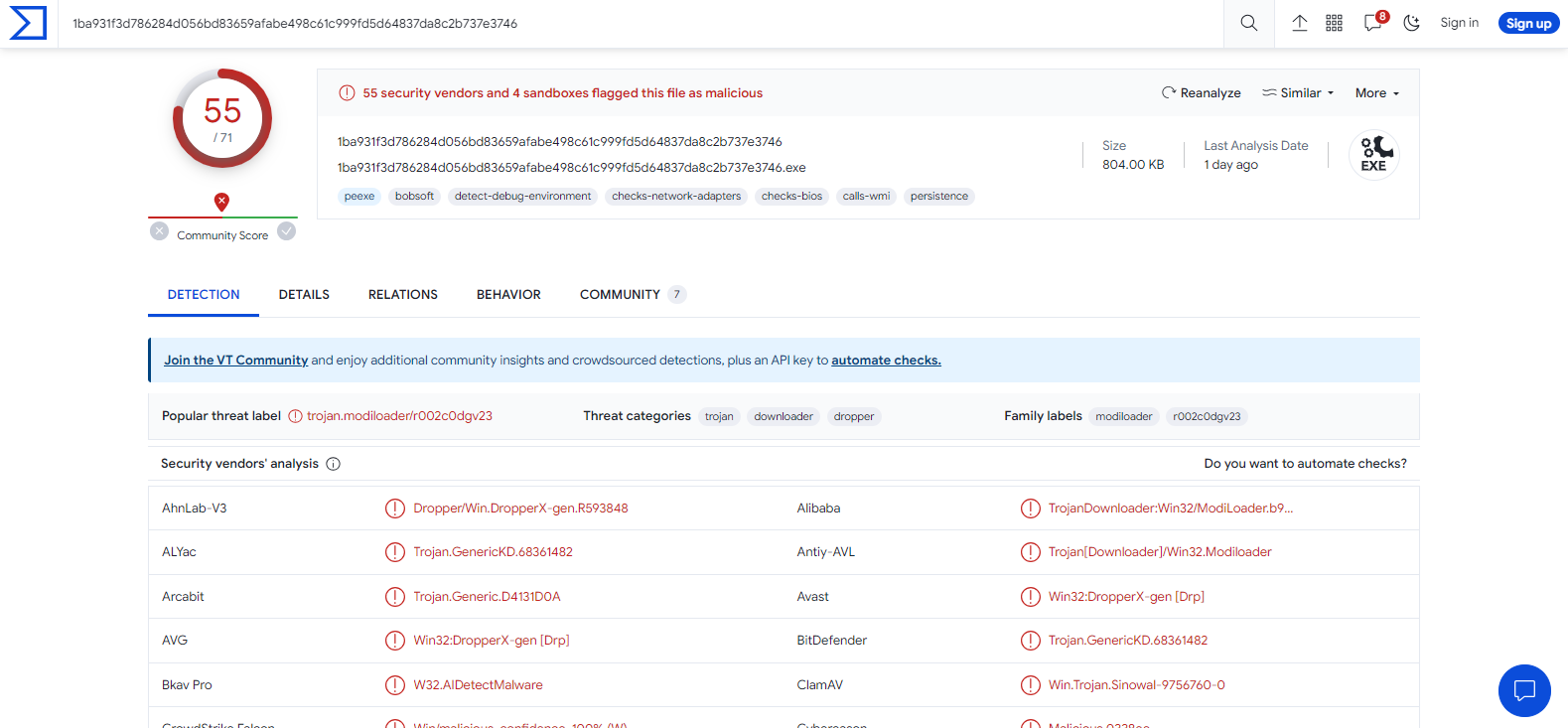
DBatLoader on Virus Total site
| Name | DBatLoader(ModiLoader) |
| Threat Type | Dropper, Malware Downloader |
| Detection | Trojan:Win32/Generic (Microsoft) |
| Payloads | Remcos, Warzone, FormBook, AgentTesla, and other RATs or information stealers |
| Symptoms | Droppers are designed to stealthily infiltrate the victim’s computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments (fake FedEx and DHL emails), malicious online advertisements, social engineering, software ‘cracks’. |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet, data encryption, monetary loss, and more. |
| Similar Behavitor | HijackLoader, WikiLoader, Trojan:BAT/FakeBardExtLoad.GA!MSR |
Technical Analysis of DBatLoader
DBatLoader undergoes ongoing development, continuously improving its capabilities. Recent versions introduce features like UAC bypass, persistence mechanisms, diverse process injection methods, and the ability to inject shellcode payloads. In its latest iteration, DBatLoader adopts an unconventional approach, employing DLL hooking. While this is typically used to evade AMSI, many of DBatLoader’s current hooking methods have critical flaws, rendering this tactic ineffective.
RATs delivered by DBatLoader allow cybercriminals to monitor and record victims’ activities, including keystrokes, screen captures, and webcam access, facilitating corporate espionage or blackmail. DBatLoader payloads offer attackers full control over infected systems, enabling the execution of arbitrary commands, file manipulation, or further network attacks. Some payloads focus on financial gain, targeting online banking credentials, cryptocurrency wallets, or conducting fraudulent transactions.
Spreading methods
Cybercriminals employ cunning methods for DBatLoader distribution. They utilize email campaigns, including fake DHL or FedEx emails. These emails package the DBatLoader executable within ISO images or various archive formats like 7-Zip, tar, zip, or rar.
To entice their targets into opening these malicious attachments, cybercriminals use convincing email lures. These lures often mimic legitimate documents, such as shipping orders, billing invoices, purchase requests, or inquiries. They create a sense of urgency or relevance, prompting victims to execute the malware and initiate the attack.


Leave a Comment