“CPU-Z virus,” malicious material camouflaged that spreads through malvertising, SEO poisoning, and dubious download channels like freeware sites. Employing deceptive tactics, it often disguises itself as a legitimate CPU-Z application.
“CPU-Z virus” executes a trojanized installer with a valid certificate, minimizing detection. The malware’s key actions include deploying a malicious PowerShell script to install the FakeBat loader, introducing the RedLine stealer into systems. This versatile information-stealing malware targets browser data, cryptocurrency wallets, and various software, posing a significant threat to users.
CPU-Z Virus Overview
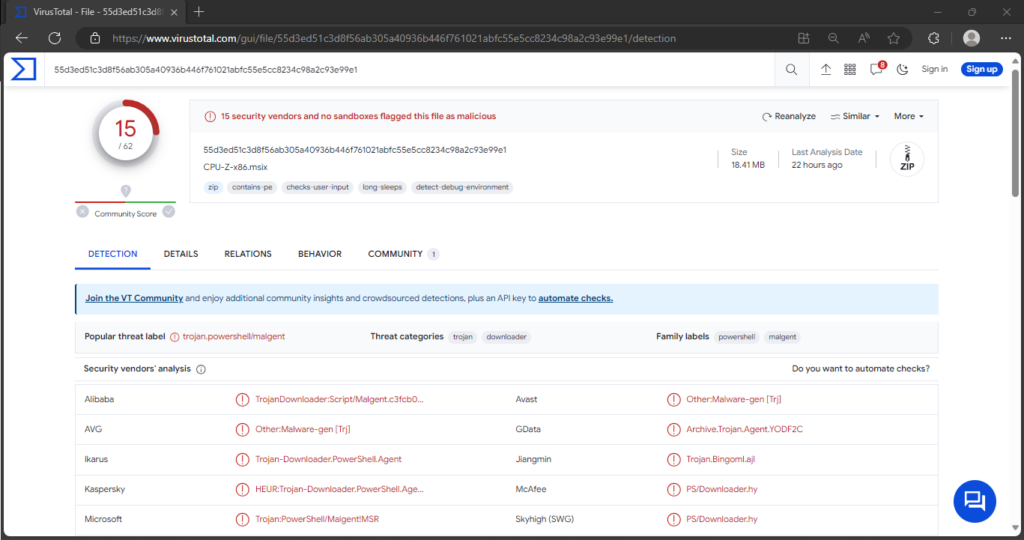
“CPU-Z Virus” on Virus Total site
| Name | “CPU-Z” |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
| Distribution methods | Malicious online advertisements, social engineering, software ‘cracks’. |
| Detection | Microsoft (Trojan:PowerShell/Malgent!MSR) |
| Domains | argenferia[.]com; realvnc[.]pro; corporatecomf[.]online; cilrix-corp[.]pro; thecoopmodel[.]com; winscp-apps[.]online; wireshark-app[.]online; cilrix-corporate[.]online; workspace-app[.]online. |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet. |
Technical Analysis
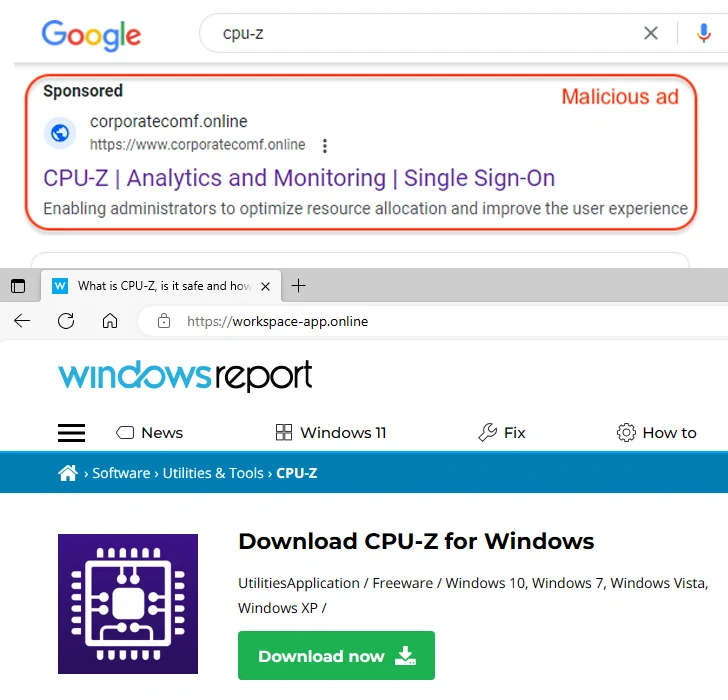
Ads promoting “CPU-Z virus”
Upon clicking the “Download now” button on the counterfeit Windows Report site, users downloaded an MSI file—the trojanized CPU-Z installation setup. Equipped with a valid certificate, this installer minimizes the likelihood of detection by Windows security measures and other antivirus tools. It targets browser data, cryptocurrency wallets, file-transferring clients, messengers, VPNs, video game platforms, and other software. However, it is crucial to note that the CPU-Z disguise may also be employed to propagate other perilous programs or malware.
Spreading methods
As previously discussed, malicious software distribution frequently involves malvertising and SEO poisoning. Users may unwittingly acquire bundled and harmful programs from questionable download channels, including freeware and free file-hosting websites, Peer-to-Peer sharing networks, and other third-party sources.
The spreading methods of malicious software encompass various strategies:
- Malicious actors exploit online advertising and search engine optimization techniques to disseminate harmful content.
- Users may inadvertently download bundled and harmful programs from questionable sources like freeware and free file-hosting websites, Peer-to-Peer sharing networks, and third-party platforms.
- Unsolicited communication methods, such as emails, PMs/DMs, SMSes, and social media posts, are utilized to promote malicious content.
- Malware or unwanted programs are often concealed in pirated software or media, enticing users with free versions of paid applications or media content.
- Cybercriminals exploit users’ trust in software updates by distributing fake updates containing malware or unwanted programs.
Understanding these spreading methods is crucial for users to adopt vigilant practices and employ security measures to protect against potential threats.
How to remove the CPU-Z Virus from my PC?
While manual removal of the threat is technically possible, I strongly discourage this method. In its pursuit of establishing persistence, Malware generates numerous instances of itself, making it exceedingly difficult to trace all its components manually. Consequently, manual removal can be time-consuming and often yield minimal to no results. Below, I have assembled a guide outlining the most effective removal practices for CPU-Z Virus.


Leave a Comment