Akira is a ransomware virus, that carries out a series of malicious actions to encrypt data, alter file names (by appending the “.akira” extension), and generate a ransom note named “akira_readme.txt.” Additionally, upon execution, Akira executes a PowerShell command to delete Windows Shadow Volume Copies on the infected device.
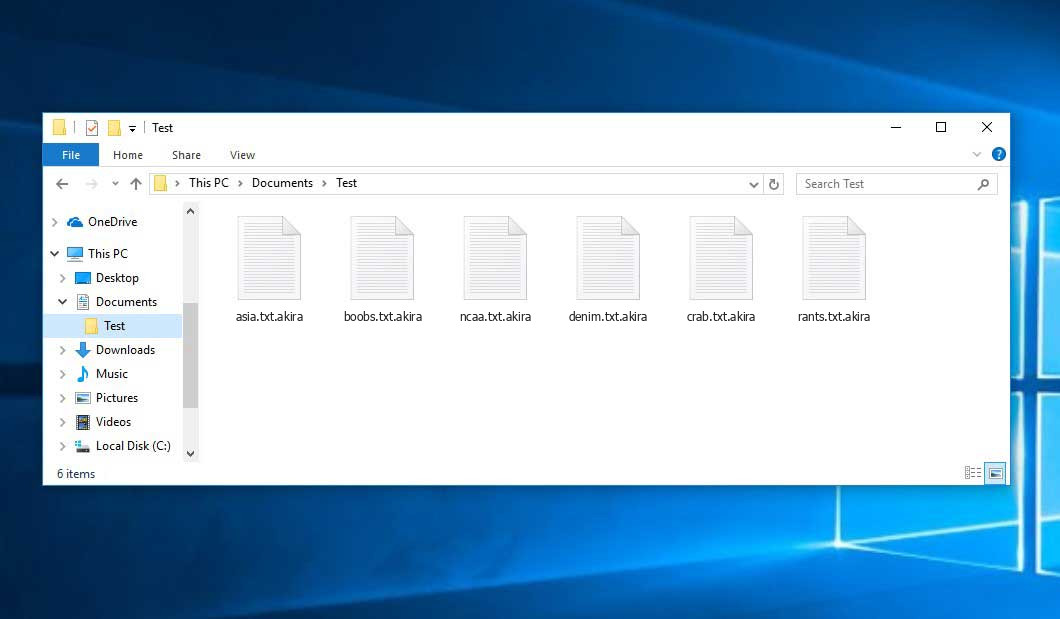
For example, Akira renames the file “1.jpg” to “1.jpg.akira” and “2.doc” to “2.doc.akira“, and so on. This makes them distinctive among untouched and new files.
What is Akira virus?
| Name | Akira Ransomware |
| Extension | .akira |
| Ransomware note | akira_readme.txt |
| Detection | Trojan:Win32/Azorult.CC!MTB, Trojan.Polyransom, Win32:Evo-gen [Trj] |
| Symptoms | Your files (photos, videos, documents) get a .akira extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Akira Ransomware |
The akira_readme.txt file accompanying the Akira malware provides the following dispiriting information:
Hi friends, Whatever who you are and what your title is if you're reading this it means the internal infrastructure of your company is fully or partially dead, all your backups - virtual, physical - everything that we managed to reach - are completely removed. Moreover, we have taken a great amount of your corporate data prior to encryption. Well, for now let's keep all the tears and resentment to ourselves and try to build a constructive dialogue. We're fully aware of what damage we caused by locking your internal sources. At the moment, you have to know: 1. Dealing with us you will save A LOT due to we are not interested in ruining your finances. We will study in depth your finance, bank & income statements, your savings, investments etc. and present our reasonable demand to you. If you have an active cyber insurance, let us know and we will guide you how to properly use it. Also, dragging out the negotiation process will lead to failing of a deal. 2. Paying us you save your TIME, MONEY, EFFORTS and be back on track within 24 hours approximately. Our decryptor works properly on any files or systems, so you will be able to check it by requesting a test decryption service from the beginning of our conversation. If you decide to recover on your own, keep in mind that you can permanently lose access to some files or accidently corrupt them - in this case we won't be able to help. 3. The security report or the exclusive first-hand information that you will receive upon reaching an agreement is of a great value, since NO full audit of your network will show you the vulnerabilities that we've managed to detect and used in order to get into, identify backup solutions and upload your data. 4. As for your data, if we fail to agree, we will try to sell personal information/trade secrets/databases/source codes - generally speaking, everything that has a value on the darkmarket - to multiple threat actors at ones. Then all of this will be published in our blog -. 5. We're more than negotiable and will definitely find the way to settle this quickly and reach an agreement which will satisfy both of us. If you're indeed interested in our assistance and the services we provide you can reach out to us following simple instructions: 1. Install TOR Browser to get access to our chat room - hxxps://www.torproject.org/download/. 2. Paste this link - -. 3. Use this code - - - to log into our chat. Keep in mind that the faster you will get in touch, the less damage we cause.
In the screenshot below, you can see what a folder with files encrypted by the Akira looks like. Each filename has the “.akira” extension appended to it.
How did Akira ransomware end up on my PC?
There is a huge number of possible ways of ransomware injection.
Malefactors currently employ three primary methods to make ransomware operate in your digital environment: email spam, Trojan infiltration, and peer-to-peer file transfer.
If you open your inbox and encounter letters resembling familiar notifications from utility service companies, delivery agencies like FedEx, Internet providers, and so on, but with unfamiliar senders, exercise caution before opening them. These letters are likely to contain harmful attachments. Consequently, opening any attachments accompanying such letters poses an even greater risk.
Another option favored by ransom hunters involves the use of a Trojan file model. A Trojan is a program that infiltrates your machine while disguised as something else. Picture this scenario: you download an installer for a program you require or an update for a service. However, upon unpacking, you discover a malicious program that encrypts your data. Since update files can bear any title and icon, it is essential to ensure the trustworthiness of the source from which you are downloading files. The safest approach is to obtain them from the official websites of the software developers.
Regarding peer networks like torrent trackers or eMule, they demand even more trust compared to the rest of the web. You cannot predict the content of your downloads until they are complete. We recommend using reputable websites and performing an immediate anti-malware scan on the directory containing the downloaded items once the download is finished.
How do I get rid of the Akira virus?
It is crucial to inform you that besides encrypting your data, the Akira virus will probably install Vidar Stealer on your PC to get access to credentials to different accounts (including cryptocurrency wallets). The mentioned program can derive your logins and passwords from your browser’s auto-filling cardfile.
Sometimes racketeers would decrypt some of your files so you know that they really have the decryption program. As Akira virus is a relatively recent ransomware, safety measures designers have not yet found a way to reverse its work. Nevertheless, the decryption tools are frequently updated, so the effective countermeasure may soon be available.
Understandably, if the criminals do the job of encrypting victim’s critical files, the hopeless person will most likely comply with their demands. Despite that, paying to racketeers gives no guarantee that you’re getting your files back. It is still risky. After receiving the ransom, the racketeers may deliver a wrong decryption key to the injured party. There were reports of malefactors simply disappearing after getting the ransom without even bothering to reply.
The optimal solution against ransomware is to have aan OS restore point or the copies of your critical files in the cloud disk or at least on an external disk. Of course, that might be not enough. Your most crucial thing could be that file you were working upon when it all went down. But at least it is something. It is also wise to scan your PC for viruses with the antivirus program after the OS is rolled back.
Akira is not the only ransomware of its kind, since there are other specimens of ransomware out there that act in the same manner. For instance, Coty, Foza, Boza, and some others. The two basic differences between them and the Akira are the ransom amount and the encoding method. The rest is almost identical: files become encoded, their extensions changed, ransom notes emerge in every directory containing encrypted files.
Some fortunate users were able to decode the blocked files with the aid of the free software provided by anti-ransomware developers. Sometimes the hackers accidentally send the decryption code to the wronged in the ransom readme. Such an extraordinary fail allows the injured part to restore the files. But obviously, one should never rely on such a chance. Make no mistake, ransomware is a bandits’ technology to pull the money out of their victims.
How do I avert ransomware infection?
Akira ransomware has no endless power, neither does any similar malware.
You can defend your PC from its attack within three easy steps:
- Never open any emails from unknown senders with strange addresses, or with content that has nothing to do with something you are expecting (how can you win in a money prize draw without even taking part in it?). In case the email subject is likely something you are waiting for, scrutinize all elements of the questionable email carefully. A hoax email will always have mistakes.
- Do not use cracked or untrusted software. Trojans are often shared as an element of cracked products, most likely under the guise of “patch” preventing the license check. But potentially dangerous programs are difficult to distinguish from trustworthy ones, as trojans may also have the functionality you need. Try to find information on this program on the anti-malware forums, but the best solution is not to use such programs at all.
Reasons why I would recommend GridinSoft1
How to decrypt Akira Ransomware Files?
1. To download the decryptor binary, you should first obtain the 64-bit version provided by Avast. Since the ransomware is designed for 64-bit systems, it cannot run on 32-bit Windows. However, if you are restricted to using 32-bit applications, you can download the 32-bit decryptor from this link.
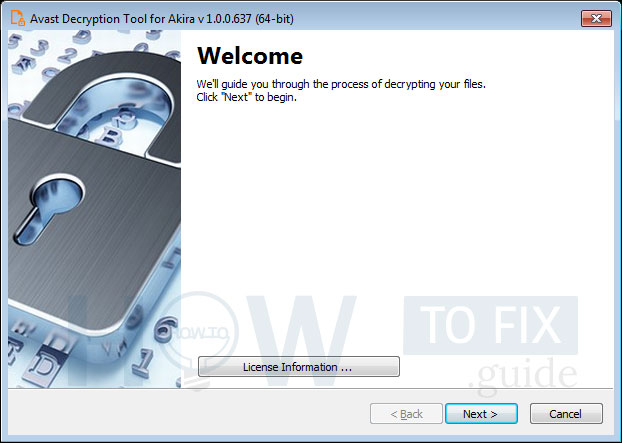
2. To initiate the decryption process, run the executable file as an administrator. The file functions as a wizard, guiding you through the configuration steps.
3. On the initial page, you will find a link to access the license information. When you are ready to proceed, click the Next button.
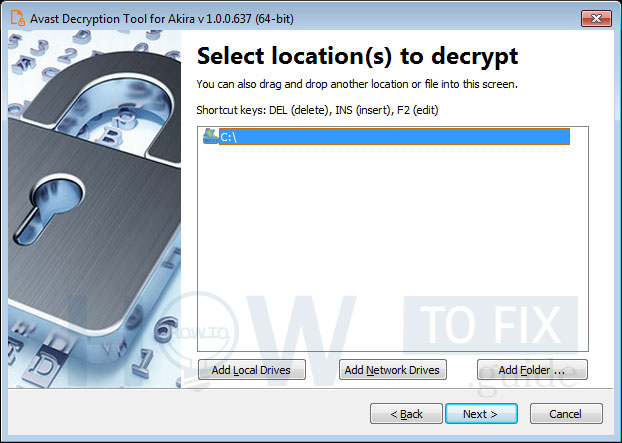
4. On the following page, select the locations you wish to search for and decrypt. By default, the tool includes a list of all local drives:
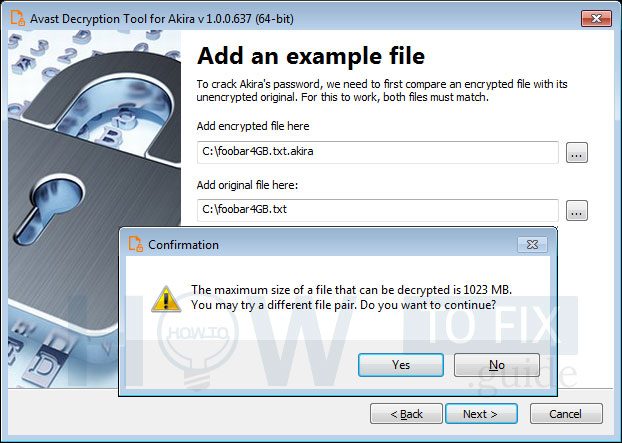
5. On the subsequent page, provide an example of a file in its original form, as well as one that has been encrypted by the Akira ransomware. Enter the names of both files or simply drag and drop them from Windows Explorer onto the wizard page.
It is crucial to select a pair of files that are as large as possible. Akira’s block size calculation can result in significant variations in the size limit, even for files that differ by just one byte.
When you click Next, the decryption tool will carefully analyze the file pair and indicate the largest decryptable file. In general, the size limit should match that of the original file:
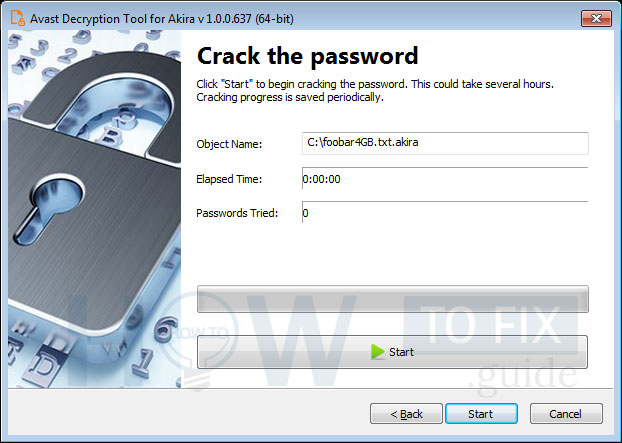
6. The subsequent page is where the password cracking process occurs. Click Start when you are ready to commence. This process typically takes only a few seconds but requires a considerable amount of system memory. Therefore, we strongly recommend using the 64-bit version of the decryption tool.
Once the password is discovered, you can proceed to decrypt all the encrypted files on your PC by clicking Next.
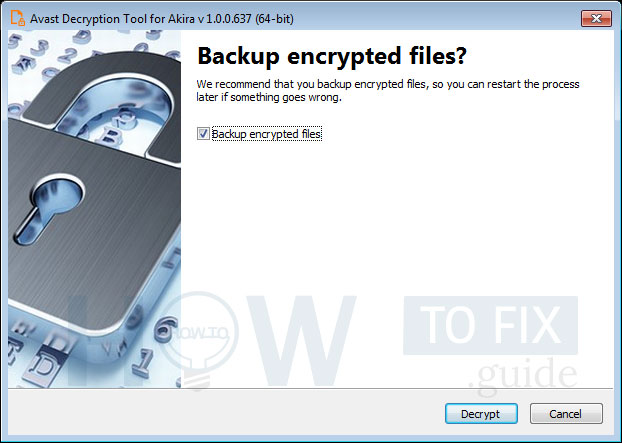
7. On the final page, you have the option to back up your encrypted files. These backups can be useful in case any issues arise during the decryption process. By default, this choice is selected, and we recommend keeping it that way. After clicking Decrypt, the decryption process will commence. Allow the decryptor to work and wait until it finishes decrypting all of your files.
FAQ
🤔 How can I open “.akira” files?Are the “.akira” files accessible?
There’s no way to do it, unless the files “.akira” files are decrypted.
🤔 I really need to decrypt those “.akira” files ASAP. How can I do that?
If the “.akira” files contain some really important information, then you probably have them backed up. In case you haven’t, there is still a chance that you do have a Restore Point from some time ago to roll back the whole system to the moment when it had no virus yet, but already had your files. All other solutions require time.
🤔 What should I do if the Akira virus has blocked my computer and I can’t get the activation key.
🤔 What could help the situation right now?
Some of the encrypted data can be found elsewhere.
- If you sent or received your critical files through email, you could still download them from your online mail server.
- You might have shared photographs or videos with your friends or family members. Simply ask them to give those pictures back to you.
- If you have initially got any of your files from the Web, you can try to do it again.
- Your messengers, social media pages, and cloud drives might have all those files too.
- Maybe you still have the needed files on your old PC, a laptop, mobile, external storage, etc.
HINT: You can use file recovery programs3 to get your lost data back since ransomware arrests the copies of your files, deleting the authentic ones. In the video below, you can see how to recover your files with PhotoRec, but be advised: you can do it only after you kill the ransomware itself with an antivirus program.
I need your help to share this article.
It is your turn to help other people. I have written this guide to help people like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Here are Best Data Recovery Software Of 2023.


Leave a Comment