The “Your browser is (62%) DAMAGED by Tor.Jack Malware” scam is a deceptive social engineering attack that spreads through pop-up ads and malicious websites. It presents users with a fabricated error message, urging them to download malicious browser extensions or programs.
The scam’s key actions include creating a false sense of urgency and tricking users into installing malware. Also, altering browser settings and potentially compromising personal information.
“Your Browser Is (62%) DAMAGED By Tor.Jack Malware” Scam Overview
The “Your Browser Is (62%) DAMAGED By Tor.Jack Malware” scam operates by displaying fake error messages. It claims that the user’s browser is severely damaged by the Tor.Jack Malware, creating a sense of urgency and fear. To further its malicious agenda, it provides a link, ostensibly to repair the browser, but in reality, it leads users to download malicious browser extensions or programs. Once users are lured into installing these malware, the scam can take several harmful actions. It may alter browser settings, inundate users with unwanted ads, and even have the potential to steal personal information, posing a significant threat to individuals’ online security and privacy.
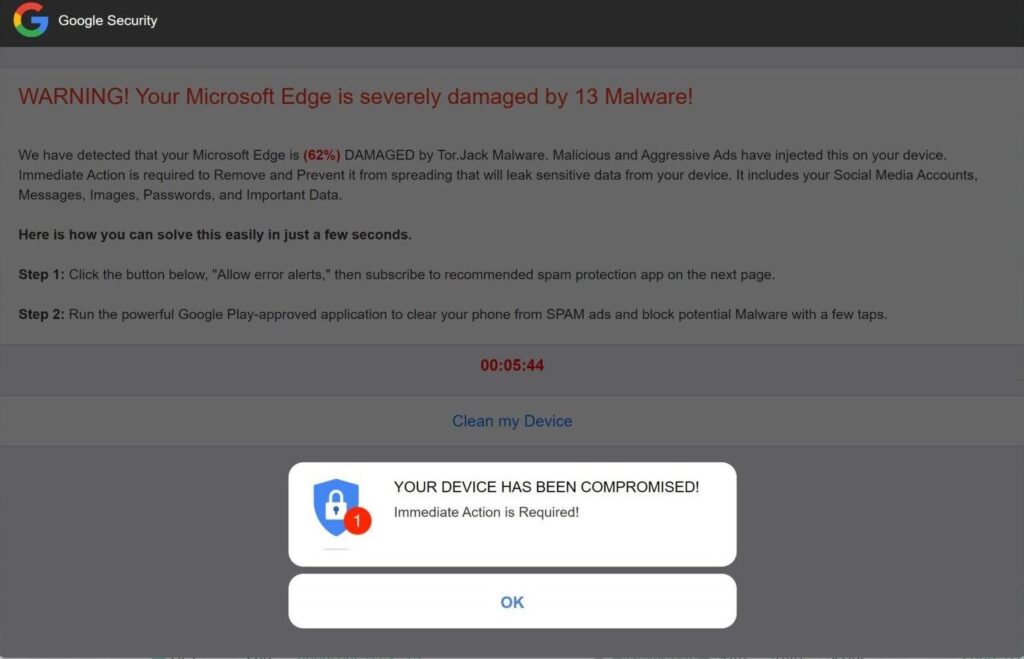
Screen of Scam Alerts
To counter this threat, users must exercise caution when encountering unfamiliar links, maintain up-to-date software, and adopt a critical approach when evaluating error messages or alerts. Furthermore, these measures are essential to protect against the technically sophisticated “Your browser is (62%) DAMAGED by Tor.Jack Malware” scam.
| Name | “Your Browser Is (62%) DAMAGED By Tor.Jack Malware” |
| Threat Type | Phishing, Pop-up Scam, Social Engineering, Fraud |
| Symptoms | Fake error messages, fake system warnings, pop-up errors, hoax computer scan. |
| Distribution methods | Compromised websites, rogue online pop-up ads, potentially unwanted applications. |
| Similar Behavior | “Avast – Your PC Is Infected With 5 Viruses!”, “Virus Has Been Detected On Your Device”, “Your computer is disabled. Please call Microsoft.” |
| Damage | Loss of sensitive private information, monetary loss, identity theft, possible malware infections. |
How does “Your Browser Is (62%) DAMAGED By Tor.Jack Malware” Scam work?
The malicious software can alter browser settings, changing the user’s homepage or search engine. It can also insert unwanted browser extensions. There is potential for data theft, including the capture of sensitive information like login credentials or financial data. The scam’s adaptability is a significant challenge. Furthermore, scammers frequently change tactics and use different payloads, making it challenging for security measures to keep up.
How serious is this?
The “Your browser is (62%) DAMAGED by Tor.Jack Malware” scam is a serious threat, but its impact can vary depending on how users respond to it and their level of security awareness. Here are some factors that determine the seriousness of this scam:
- If users fall for the scam and download the malicious software, there is a significant risk of personal information theft. Also, this could include login credentials, financial data, and other sensitive information.
- The scam can alter browser settings and insert unwanted extensions, leading to a degraded browsing experience. While this may not have severe consequences, it can be frustrating and intrusive.
- In some cases, the scam may lead to financial losses, especially if users are tricked into purchasing fake security software or services to “fix” the non-existent issue.
- If the scam manages to install malicious software on a user’s device, it can be used as a platform to spread other malware, potentially infecting other systems and contributing to a broader security threat.
- Falling victim to this scam can also result in reputation damage, especially if personal or sensitive information is compromised.
In summary, while this scam doesn’t pose immediate physical harm, it can have serious consequences, including financial loss and compromised personal information. Its seriousness is primarily dependent on users’ actions and their level of protection and awareness.


Leave a Comment