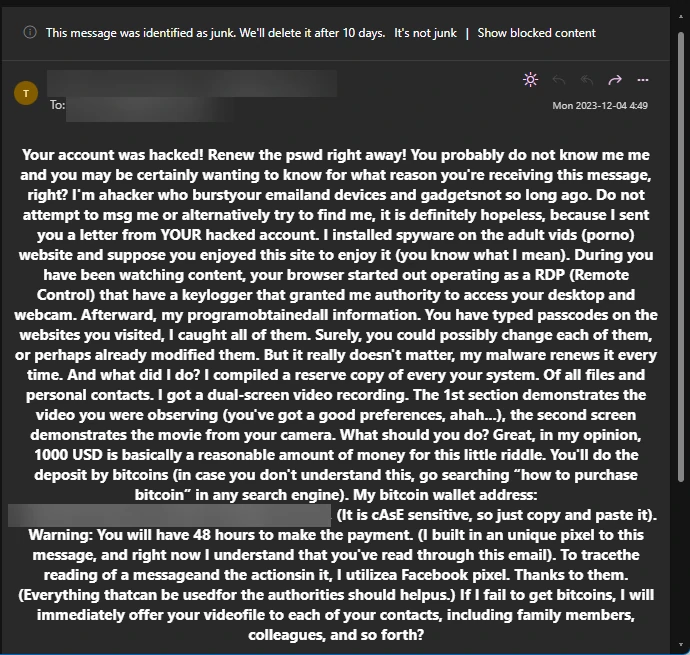
“Your Account Was Hacked” is a scam disseminated through spam campaigns that pose a fake email. It claims the hacker has hacked the recipient’s email account.
Crooks use “spoofing” to forge sender addresses. Thus, they allege the installation of a Trojan via an adult website visit, enabling remote access to the victim’s desktop and webcam. The crux involves a false video claim, pressuring victims to pay $1000 in Bitcoin within 48 hours to prevent its release. While widespread, users are urged to ignore these deceptive emails to thwart potential financial and emotional harm.
What Is “Your Account Was Hacked” Email Scam?
A “Your Account Was Hacked” scam represents one among various spam campaigns designed to deceive individuals into making payments to cyber criminals. In this scenario, scammers deploy an email asserting that the recipient’s computer harbors a malicious program, enabling the unauthorized recording of a compromising video.
The fraudulent communication further alleges the theft of personal data and details. But, the primary objective of this email is to coerce individuals into paying cybercriminals who threaten to disseminate the incriminating video if their stipulated demands are not met within the specified deadline. It is crucial to note that emails of this nature should be disregarded.”
“Your Account Was Hacked” Email Scam
| Name | Your Account Was Hacked Email Scam |
| Threat Type | Phishing, Scam, Social Engineering |
| Distribution methods | This scam is spread wide via spam email campaigns. |
| Damage | Monetary loss – completely unnecessary payments for fake claims about hacking and in reality non-existent video recordings. |
| Similar Behavitor | “Professional Hacker” Email Scam, “Professional Hacker Managed To Hack Your Operating System” Email Scam |
| Fix Tool | See If Your System Has Been Affected by Your Account Was Hacked Virus |
How Does “Your Account Was Hacked” Scam Work?
The “Your Account Was Hacked” email scam manifests in two versions, which are fundamentally identical. The fraudulent communication asserts that the user’s email account has been compromised. To lend credibility to their claim, scammers employ the spoofing method, allowing them to forge email addresses. In this instance, cybercriminals utilize the recipient’s email address, creating the illusion that the recipient is also the sender. Additionally, they assert that the computer has been infected with a Trojan, functioning as a remote access tool.
According to the scammers, this unwarranted installation occurred when the recipient visited an adult website, enabling the remote access tool to infiltrate the user’s desktop and webcam. Furthermore, the cybercriminals allege the theft of various passwords and contacts. The crux of the email is the assertion that the criminals have recorded a video of the recipient engaging with adult content. To prevent the dissemination of this video to all the recipient’s contacts, they demand a $1000 payment in Bitcoins, providing Bitcoin wallet addresses for the transaction.
Scammers prompt the victim to remit the payment within 48 hours, threatening to release the video if the deadline is not met. It is imperative to note that no such video exists, and this is merely a scam designed to exploit the vulnerability of some users. Receiving this email likely means you are one among numerous recipients. In such instances, disregarding the emails is the most prudent course of action.
Is It Dangerous?
The email is not dangerous if you don’t do what it says. The only risk is financial loss and an increase in similar scams in the future. Since the scammers were able to fool the victim once, they will obviously try to do it again.
As we wrote above, the only correct solution is to ignore the email. Alternatively, you can mark it as spam and block the sender. This way, you will help improve your anti-spam filters. Besides, the scammers will likely realize that it doesn’t work with your mailbox and stop bothering you.
Remove Your Account Was Hacked with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Stealers as shown from our tests with the software, and we assure you that it can remove Your Account Was Hacked as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “Your Account Was Hacked” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing Your Account Was Hacked and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
Frequently Asked Questions (FAQ)
The only risk of this email is financial loss and an increase in similar scams in the future.
The chance of threats being true is minimal. They are often scammers trying to fool naive users. Search for the scam text on Google – you will see info about thousands of same spam messages. There is no way someone can have that much compromising materials.
Ignore, or even delete in from the inbox. Never reply scam messages, regardless of their contents. By replying to a message, you confirm that your mailbox is valid. Even if the current scam is unsuccessful, the scammers will know that this address is “live” and try to pull off other schemes.
How to Remove Your Account Was Hacked Malware
Name: Your Account Was Hacked
Description: "Your Account Was Hacked" is a scam disseminated through spam campaigns that pose a fake email. It claims the hacker has hacked the recipient's email account. Crooks use "spoofing" to forge sender addresses. Thus, they allege the installation of a Trojan via an adult website visit, enabling remote access to the victim’s desktop and webcam. The crux involves a false video claim, pressuring victims to pay $1000 in Bitcoin within 48 hours to prevent its release. While widespread, users are urged to ignore these deceptive emails to thwart potential financial and emotional harm.
Operating System: Windows
Application Category: Malware

