XMRig is a legitimate cryptocurrency mining tool that was developed by the same-named team. It is designed to mine Monero (XMR) cryptocurrency, using the hardware of your computer. By design, it is 100% safe and does not violate your security in any way. But there are a lot of cases when cybercriminals hijack this program or its name for outlaw purposes.
Is XMRig a virus?
XMRig is a legitimate program, but cybercriminals sometimes use it for malevolent purposes.
Is XMRig a virus? – It is hard to say clearly without checking the details. The easiest situation is when you have never touched crypto mining, and suddenly discover an instance of XMRig running on your computer. It cannot appear out of the blue, and Windows does not carry one in the standard distribution. Hence, if you know that no mining tools like the XMRig miner can be present – you definitely have a deal with a virus.
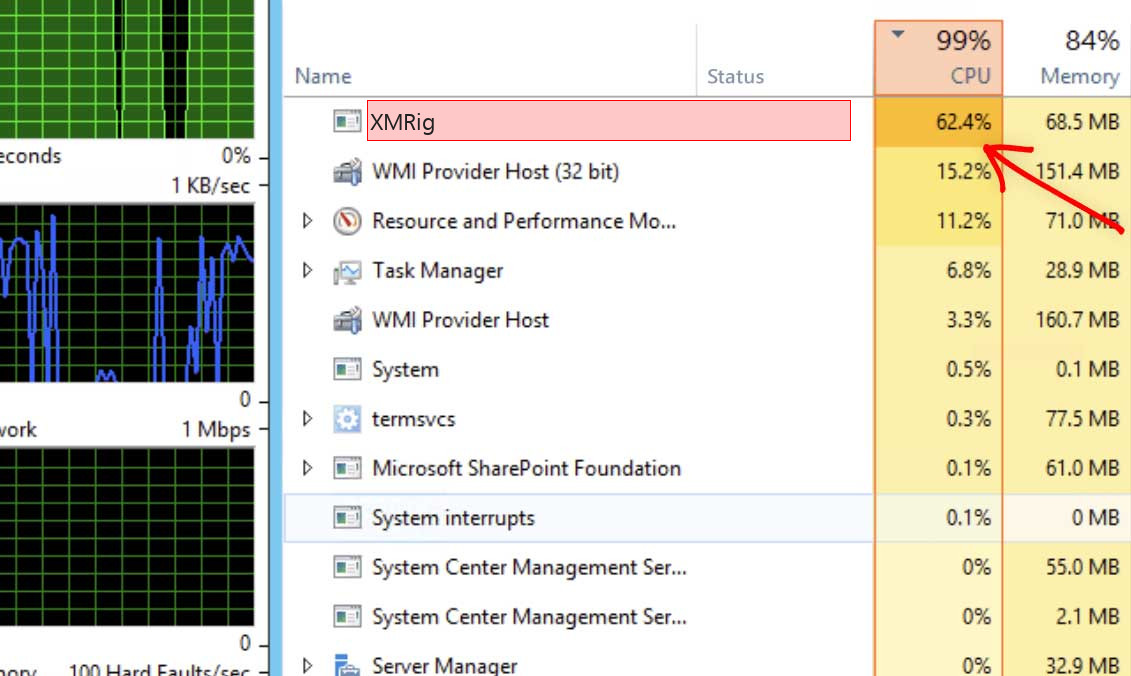
One more sign of a malicious variant of XMRig is CPU consumption. For sure, it will consume your CPU power even when it is legit. However, the legit program does not take a lot of processor power by default. Meanwhile, the virus does not think about your comfort – and takes up to 90%, making your system impossible to use.
XMRig is a particularly popular form of malware among cybercriminals due to the anonymity and privacy features of Monero, which makes it more difficult to track and trace the flow of funds. Additionally, XMRig is often used in cryptojacking attacks, where the malware is installed on multiple computers to mine Monero on a large scale, generating significant profits for the attackers.
If you suspect your computer may be infected with XMRig malware, it is recommended that you run a malware scan using reputable antivirus software and take steps to remove the malware from your system.
How XMRig malware typically works?
- Infection: XMRig malware typically infects a victim’s computer through a variety of methods, such as phishing emails, malicious websites, or software exploits.
- Installation: Once the malware infects the victim’s computer, it installs itself on the system without the user’s knowledge or consent.
- Mining: XMRig malware runs in the background, using the victim’s CPU or GPU to perform complex calculations to mine Monero.
- Communication with Command and Control (C2) Server: XMRig malware communicates with a Command and Control (C2) server, which is controlled by the attacker. The C2 server provides the malware with the configuration settings for mining and receives updates on the mining progress and any mined cryptocurrencies.
- Evasion: XMRig malware typically uses various techniques to evade detection and removal by the cybersecurity software, such as hiding its processes, modifying system files, and disabling security software.
- Profit: The attacker earns a profit from the mined Monero, which is sent to their Monero wallet.
How do I know if XMRig is legit?
There are several ways of checking the legitimacy of this process – naming, file location, and certain symptoms.
In all cases it requires a bit more precise check-up. First of all, it is important to check if the process you spectate in your Task Manager is legit at all. The original XMRig process has the name “xmrig” and a specific logo. Fraudulent processes can also be called the same, but will likely have no logo. But the more often case is when the process has just a similar name, not the same. Here are the most typical names of the malicious copies:
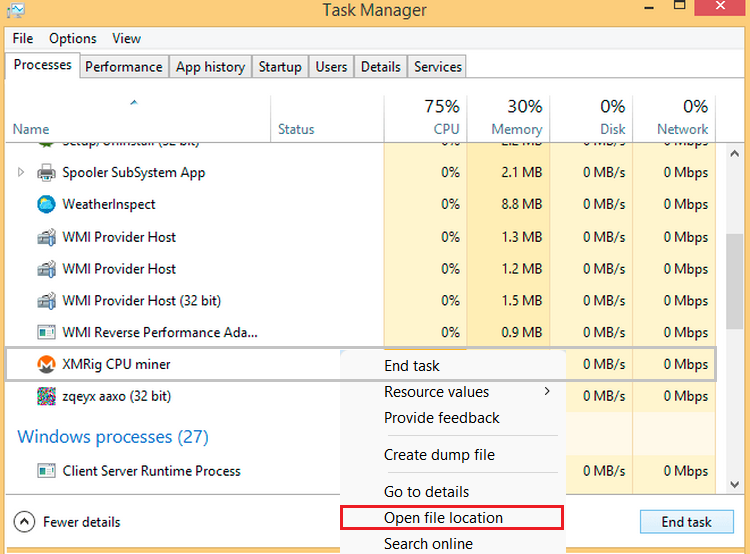
Checking the file location
If you are not certain about the file name of the file you see, check its location on your disk. For this purpose, click it in the Task Manager with a right mouse button, then choose “Open file location”. The directory that appears after this action is, exactly, the place where this file is stored. If it lies somewhere in C:\Users\%your_username%\temp, it is likely a virus1. Overall, seeing it away from C:\Program Files is suspicious, excepting the cases when you installed it into another directory by yourself.
What is crypto mining?
Cryptomining is a process of calculating the cryptocurrency transaction hash. Certain amounts of the transactions (differs from one cryptocurrency to another) form the block – a structured part of the blockchain. Calculating the hash is not an easy task – it requires serious multi-thread calculating power. And the result (mining premium) depends on the speed of your calculations. That’s why professional miners almost exclusively use so-called crypto mining farms – dozens of computer systems with a specific – ideal for mining – configuration.2
Fraudsters, on the other hand, decided not to spend thousands of dollars purchasing these mining computers. Their idea is to infect hundreds and thousands of computers with mining software, connect them to a single network, and receive all of the profit from this operation. Monero is one of the best coins for fraudsters, because of the calculation simplicity and relatively high price. XMRig, correspondingly, is just a suitable tool for this purpose. They can take any other program which can mine Monero, or develop their own.
How could I get the XMRig malware?
XMRig cannot appear on your PC autonomously. If you did not get it manually, there are several ways you downloaded it unintentionally.
If you have never touched crypto mining before, there is no way to get this program in a normal way. Downloading it from the official website, or from GitHub, must be 100% intended. Meanwhile, there are tons of different ways of illegal installation of that program on your PC. Generally, the most popular ways to spread malicious miners are online banners, email spam, and pirated applications.

Example of malvertising
Online banners, exactly, their variants that sometimes are called “malvertising”, have the biggest share of coin miners spreading. Disgusting blinking ads with dubious content will likely force you to search the “X” to close it, but this crossing can be just absent. In rare cases, you can just misclick, and malware will be downloaded to your PC. This or another way, it is always better to avoid interacting with ads on the Internet.
Email spam messages, together with pirated programs, contain the virus inside of the file. In the case of email, the file is attached to the message. To say clearly, you receive not the exact malware, but a script, which then downloads the malware. But this is too long to explain there. And what is the difference, if you still get your hardware overloaded?
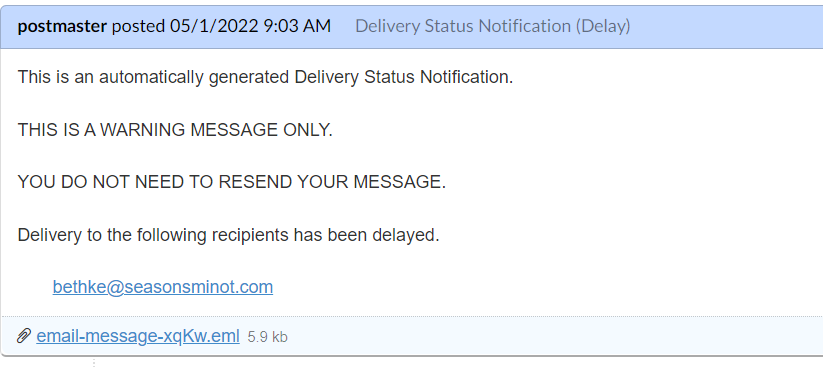
The typical example of a bait email
How do I remove XMRig from my PC?
GridinSoft Anti-Malware3 will be the best solution for the unwanted XMRig miner removal.
That’s no matter how it appears on your PC if you still do not want it to exist in your system. High CPU usage makes your computer impossible to use for any other task, so removing it with a proper tool is the best choice. GridinSoft Anti-Malware is the one that will easily wipe out the miner and fix the software changes it did to your OS.
Why GridinSoft Anti-Malware? Microsoft Defender is rather good at scanning, but is almost useless for malware removal. Because of the bugs in its code, it sometimes even struggles to start an on-demand scanning. That’s why it is better to have a third-party and workable solution than to rely on the Defender.
Removing the threat with GridinSoft Anti-Malware
- Run the setup file.
- An User Account Control asking you about allowing GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
- Press the “Install” button.
- Once installed, Anti-Malware will automatically run.
- Wait for the Anti-Malware scan to complete.
- Click on “Clean Now”.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.




GridinSoft Anti-Malware will automatically start scanning your system for XMRig files and other malicious programs. This process can take 20-30 minutes, so I suggest you periodically check on the status of the scan process.

When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in the right corner.

If the guide doesn’t help you to remove XMRig infection, please download the GridinSoft Anti-Malware that I recommended. Also, you can always ask me in the comments to get help. Good luck!
User Review
( votes)References
- Read why malware developers “love” the temp folder so much.
- More information about cryptocurrency mining on Investopedia.
- Read why do I recommend you to use GridinSoft Anti-Malware.
![]() German
German ![]() Japanese
Japanese ![]() Spanish
Spanish ![]() Portuguese (Brazil)
Portuguese (Brazil) ![]() French
French ![]() Turkish
Turkish ![]() Chinese (Traditional)
Chinese (Traditional) ![]() Korean
Korean ![]() Indonesian
Indonesian ![]() Hindi
Hindi ![]() Italian
Italian