Xeno RAT is a pernicious malware that infiltrates systems through phishing, exploiting software vulnerabilities, and dubious downloads from compromised websites or P2P networks.
Its extensive control features stand out, including surveillance capabilities like webcam and microphone access, keystroke logging, and system manipulation. This malware exemplifies the sophisticated blend of stealthy infiltration and comprehensive control in modern cyber threats.
Xeno RAT Overview
Xeno is a Remote Access Trojan (RAT) that enables threat actors to control computers remotely. It is written in the C# programming language, ensuring it operates seamlessly on Windows 10 and 11 operating systems. To mitigate risks, victims must promptly remove Xeno from any infected systems.
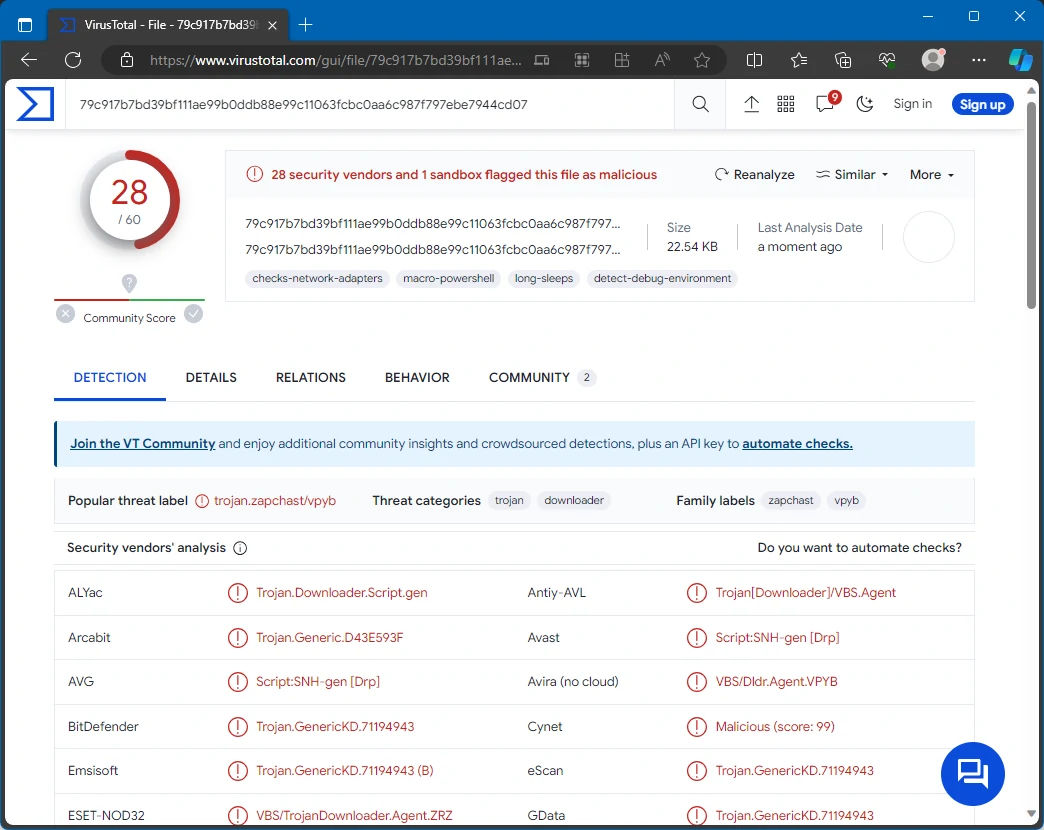
Xeno Malware on VirusTotal
| Name | Xeno |
| Threat Type | Remote Administration Trojan |
| Detection | VBS/TrojanDownloader.Agent.ZRZ |
| Damage | Stolen passwords and banking information, identity theft, additional infections, monetary loss, stolen personal accounts, system crashes, and more. |
| Similar Behavitor | SparkRAT, JanelaRAT |
Technical Analysis
Xeno RAT has a chat function, enabling direct communication between the attacker and the victim. It also features a Bluescreen (BSoD) function, allowing attackers to trigger system crashes, adding a disruptive twist. The malware’s message box function displays dialog boxes, such as pop-up windows, to the victim. Attackers can playfully assert control by toggling the monitor on/off and opening/closing the CD tray.
Xeno’s surveillance capabilities are extensive. It uses Hidden Virtual Network Computing (HVNC) for covert observation and control of the victim’s desktop. The webcam feature remotely activates the target’s camera, and the live microphone function allows for real-time audio monitoring. The RAT includes key logger and offline key logger features, capturing keystrokes and logging sensitive information for later retrieval. Its screen control feature enables manipulation and observation of the victim’s display.
An information-grabbing feature extracts sensitive data like cookies and passwords, which is crucial for attackers aiming to compromise user credentials. Its startup function ensures persistence, keeping the RAT active even after the system reboots. Xeno RAT can bypass User Account Control (UAC) using techniques like Cmstp, Windir, and Disk Cleanup, elevating privileges and sidestepping security measures. Client-oriented features control the RAT’s activity and presence, including close, relaunch, and uninstall options. Moreover, shutdown and restart functionalities give attackers control over the system’s operational state.
Spreading Methods
Your computer might have been infected with Xeno RAT through several deceptive tactics commonly used by cybercriminals. Phishing is a frequent method where attackers send convincing emails or messages with malicious links or attachments. When you unknowingly click on these links or open the attachments, the malware is downloaded and executed on your system.
Cybercriminals also exploit software vulnerabilities. They target outdated or unpatched software, using security flaws to gain unauthorized access and plant malware. Infections can also arise from pirated software, cracking tools, or encountering malicious advertisements. Other standard infiltration methods include drive-by downloads from compromised or untrustworthy websites, files from peer-to-peer (P2P) networks, third-party downloaders, and similar sources.
How To Remove Xeno RAT
While removing the threat manually is technically possible, I advise against it. Malware, aiming for persistence, multiplies its instances, making complete tracing challenging. Manual removals are often time-consuming and inefficient.


Leave a Comment