What is Trojan:Win32/Tnega!ml infection?
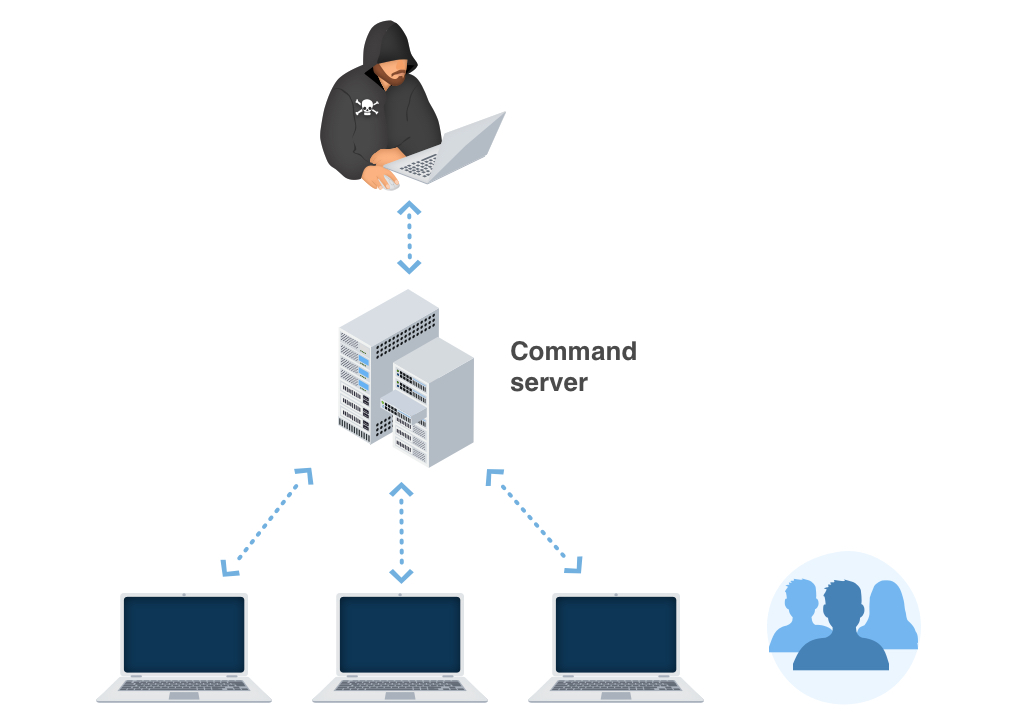
In this post, I am going to explain you the meaning of Trojan:Win32/Tnega!ml and its unpleasant impact on your computer. This malware is known for downloading other malware to your computer. To make the malware injection easier, Trojan:Win32/Tnega!ml changes several system settings.
Most of the cases, Trojan:Win32/Tnega!ml will not show any visible signs of activity. This is what makes it so dangerous. You simply cannot say if the Tnega trojan is active unless it is too late and you system is full of malware.
Trojan:Win32/Tnega!ml Summary
This virus performs the next actions after being injected:
- Reads data out of its own binary image. The trick that allows the malware to read data out of your computer’s memory.
Everything you run, type, or click on your computer goes through the memory. This includes passwords, bank account numbers, emails, and other confidential information. With this vulnerability, there is the potential for a malicious program to read that data.
- Network activity detected but not expressed in API logs. Microsoft built an API solution right into its Windows operating system it reveals network activity for all apps and programs that ran on the computer in the past 30-days. This malware hides network activity.
- Changes the networking settings, in particular, HOSTS file
- Disables the Microsoft Defender
Trojan:Win32/Tnega!ml distribution methods
The most regular networks through which Trojan:Win32/Tnega!ml Trojans are injected are:
- Email spamming;
- Unlicensed software usage
- Malvertising on the Internet;
Email spam became a very popular malware distribution method, since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One which is send by a cybercriminals has a strange sender address – something like [email protected], while the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Malicious advertisements on the web, however, is an old-timer of malware distribution. And the advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads on the Internet. You can also install ad blocking plugins for your web browser – they will deal with any kind of ads. However, if they are generated by adware which is already present on your PC, ad blockers will be useless.
Trojan:Win32/Tnega!ml effects.
As it was mentioned, Trojan:Script/Tnega!ml acts as a downloader for other viruses, preparing the “comfortable” environment for the arriving malware. Changing the networking settings can lead to problems with connecting to some websites or servers. Disabling the Windows Defender is much easier to discover, but a lot of users do not use this antivirus tool. Hence, the chance that the virus activity will stay undetected until the additional malware is downloaded is very high. Fortunately, the Tnega virus waits a bit before injecting the additional malware. You prevent all bad consequences of its activity, especially if you make use of GridinSoft Anti-Malware. Read the removal guide below.
Technical details
File Info:
crc32: 9A00430Fmd5: 9d6a9da6a79c6b4c9049e43e7b0d5c92name: upload_filesha1: e3e00a6a3cfa3035551ea880ece3607c0cd52b95sha256: bb1d54a5907bd2d043bdb8c31d9c171636ca4f76d5af4eed0b99061072dbb8bbsha512: 3ecb90032d231fa2f692caa76766ed01787ef8742646924e049441ecdf05b68a5d1d496519da7018add277a11a9b1675abb380fb87ee016f85d8ef989ac82002ssdeep: 12288:898nAWgFbHHOiZkGXN186nx3KcK0XSww+MxTy/Nyhh9aAwGR:KggxTs6nFO0ijwNy7type: RAR archive data, v1d, os: Win32Version Info:
0: [No Data]
Trojan:Win32/Tnega!ml also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Malwarebytes | Ransom.HiddenTear |
| Sangfor | Malware |
| Arcabit | Trojan.Strictor.D14AD4 |
| Invincea | Mal/DrodZp-A |
| ESET-NOD32 | a variant of MSIL/GenKryptik.EURE |
| Cynet | Malicious (score: 70) |
| BitDefender | Gen:Variant.Strictor.84692 |
| MicroWorld-eScan | Gen:Variant.Strictor.84692 |
| Tencent | Win32.Trojan.Worm.Hvta |
| Emsisoft | Gen:Variant.Strictor.84692 (B) |
| Comodo | Heur.Dual.Extensions@1z141z3 |
| F-Secure | Heuristic.HIDDENEXT/Worm.Gen |
| TrendMicro | HEUR_NAMETRICK.A |
| FireEye | Gen:Variant.Strictor.84692 |
| Sophos | Mal/DrodZp-A |
| Avira | HIDDENEXT/Worm.Gen |
| Microsoft | Trojan:Win32/Tnega!ml |
| GData | Gen:Variant.Strictor.84692 |
| AhnLab-V3 | Trojan/Win32.Fsysna.C4207429 |
| BitDefenderTheta | AI:Packer.07F716F420 |
| ALYac | Gen:Variant.Strictor.84692 |
| MAX | malware (ai score=85) |
| Fortinet | MSIL/GenKryptik.EREI!tr |
How to remove Trojan:Win32/Tnega!ml virus?
Tnega virus is able to infect your system with various dangerous malware. It is recommended to remove it as soon as possible.
Reasons why I would recommend GridinSoft1
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Trojan:Win32/Tnega!ml files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
If the guide doesn’t help you to remove Trojan:Win32/Tnega!ml you can always ask me in the comments for getting help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison



Before downloading anything just try Scanner
Good Luck