The Trojan:PowerShell/InvokeObfuscation notification means that your computer has a problem. Allowing it to run may lead to really bad consequences.
Invoke Obfuscation is a malware that aims at opening your system to further threats. The majority of the modern virus samples are complex, and can download other viruses. Being infected with the Trojan:PowerShell/InvokeObfuscation virus often means getting a thing which can act like spyware or stealer, downloader, and a backdoor. Spectating this detection means that you must to perform the removal as fast as you can.
Trojan:PowerShell/InvokeObfuscation Detection Overview
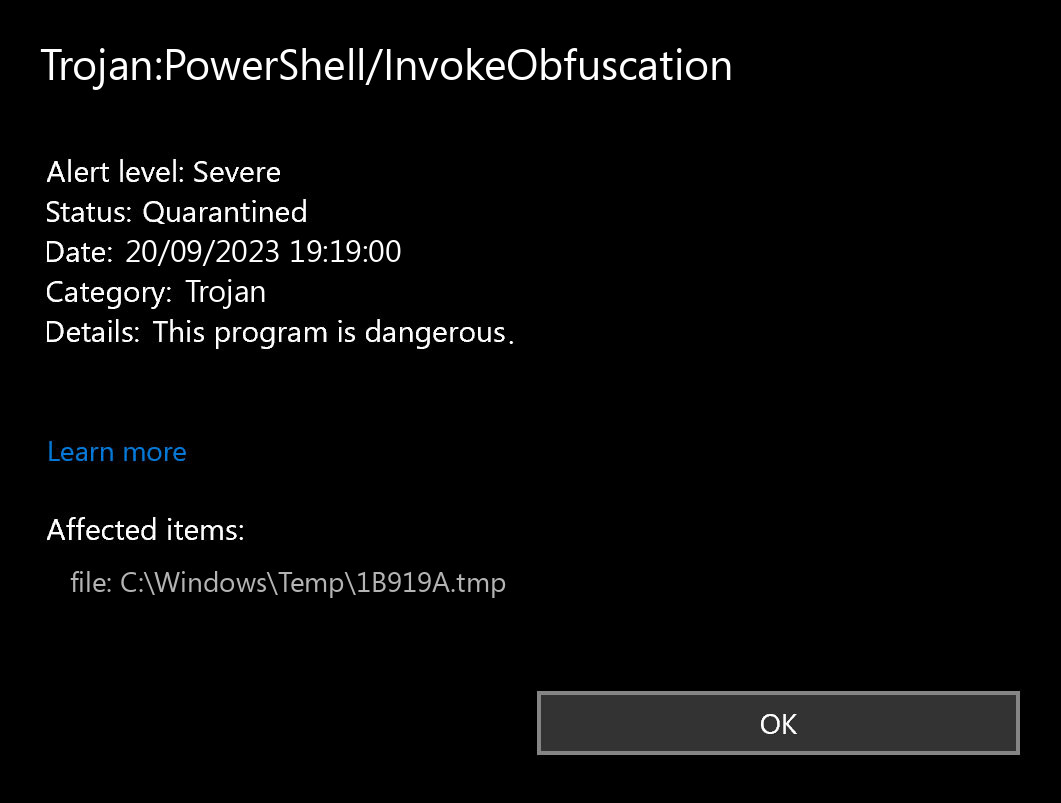
The Trojan:PowerShell/InvokeObfuscation detection you can see in the lower right corner is shown to you by Microsoft Defender. That anti-malware software is good at scanning, however, prone to be generally unstable. It is unprotected to malware invasions, it has a glitchy user interface and problematic malware removal capabilities. Hence, the pop-up which states concerning the Invoke Obfuscation is just a notification that Defender has detected it. To remove it, you will likely need to use another anti-malware program.
The exact Trojan:PowerShell/InvokeObfuscation virus is a very undesirable thing. It sits inside of your system under the guise of something normal, or as a piece of the app you downloaded at a forum. Then, it makes all possible steps to weaken your system. At the end of this “party”, it injects other malicious things – ones which are choosen by cyber burglars who control this malware. Hence, it is impossible to predict the effects from Invoke Obfuscation actions. And the unpredictability is one of the most upleasant things when it comes to malware. That’s why it is better not to choose at all, and don’t let the malware to complete its task.
Threat Summary:
| Name | Invoke Obfuscation Trojan |
| Detection | Trojan:PowerShell/InvokeObfuscation |
| Details | Invoke Obfuscation tool that looks legitimate but can take control of your computer. |
| Fix Tool | See If Your System Has Been Affected by Invoke Obfuscation Trojan |
Is Trojan:PowerShell/InvokeObfuscation dangerous?
As I have specified , non-harmful malware does not exist. And Trojan:PowerShell/InvokeObfuscation is not an exclusion. This virus modifies the system settings, alters the Group Policies and Windows registry. All of these elements are crucial for correct system functioning, even in case when we are not talking about system safety. Therefore, the virus which Invoke Obfuscation carries, or which it will download later, will try to get maximum revenue from you. Crooks can steal your personal data, and then sell it on the Darknet. Using adware and browser hijacker functionality, embedded in Trojan:PowerShell/InvokeObfuscation malware, they can make profit by showing you the banners. Each view gives them a penny, but 100 views per day = $1. 1000 victims who watch 100 banners per day – $1000. Easy math, but sad conclusions. It is a bad choice to be a donkey for crooks.
How did I get this virus?
It is difficult to trace the sources of malware on your computer. Nowadays, things are mixed, and spreading tactics chosen by adware 5 years ago may be utilized by spyware nowadays. But if we abstract from the exact distribution way and will think about why it has success, the answer will be quite basic – low level of cybersecurity understanding. Individuals click on promotions on odd sites, click the pop-ups they get in their web browsers, call the “Microsoft tech support” thinking that the weird banner that states about malware is true. It is essential to understand what is legitimate – to avoid misunderstandings when attempting to find out a virus.
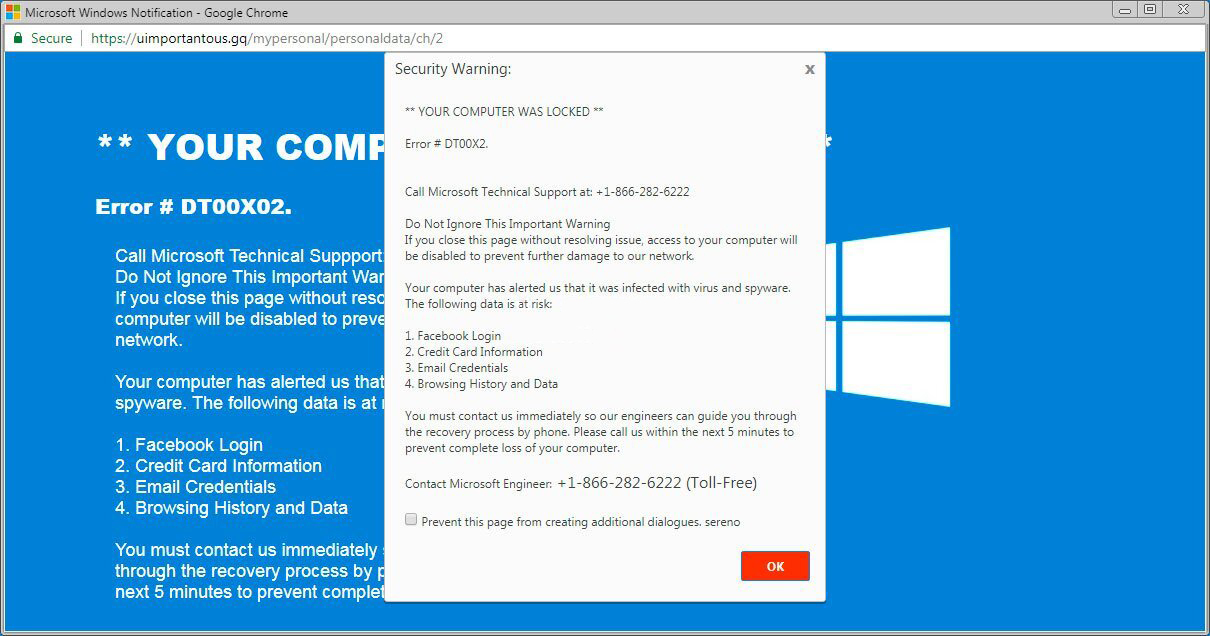
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common ways of malware distribution – bait e-mails and injection into a hacked program. While the first one is not so easy to stay away from – you should know a lot to understand a fake – the second one is simple to get rid of: just do not utilize hacked applications. Torrent-trackers and other sources of “free” applications (which are, exactly, paid, but with a disabled license checking) are really a giveaway place of malware. And Trojan:PowerShell/InvokeObfuscation is just within them.
Remove Invoke Obfuscation with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Trojans as shown from our tests with the software, and we assure you that it can remove Invoke Obfuscation as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2.Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3.Follow the installation setup wizard's instructions diligently.

4. Access the "Scan Tab" on the application's start screen and launch a comprehensive "Full Scan" to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer's hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the "Clean Now" button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer's security without any financial commitment.
Trojan Killer for “Invoke Obfuscation” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft - Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the "removable drive" following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click "Update" icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on "Full Scan" to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on "Cure PC!" to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on "Restart PC" to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing Invoke Obfuscation and the concealed threats from your computer! You can now have peace of mind, knowing that they won't resurface again. Thanks to Gridinsoft's capabilities and commitment to cybersecurity, your system is now protected.
What is Trojan:PowerShell/InvokeObfuscation Virus?
Name: Trojan:PowerShell/InvokeObfuscation
Description: If you have seen a message showing the “Trojan:PowerShell/InvokeObfuscation found”, it seems that your system is in trouble. The Invoke Obfuscation virus was detected, but to remove it, you need to use a security tool. Windows Defender, which has shown you this message, has detected the malware. However, Defender is not a reliable thing - it is prone to malfunction when it comes to malware removal. Getting the Trojan:PowerShell/InvokeObfuscation malware on your PC is an unpleasant thing, and removing it as soon as possible must be your primary task.
Operating System: Windows
Application Category: Trojan