The Trojan:MSIL/Redline.CBYZ!MTB notification means that your computer has a problem. Allowing it to keep running may lead to some really bad consequences. This malware targets on stealing different categories of information from your computer.
Redline applies a lot of stunts to avoid malware detection, and uses protected connections to send data to the command server. The activity of this malware commonly results in losing access to your accounts, and exposing your identity. Moreover, certain samples are also able to deliver other malware to the system.
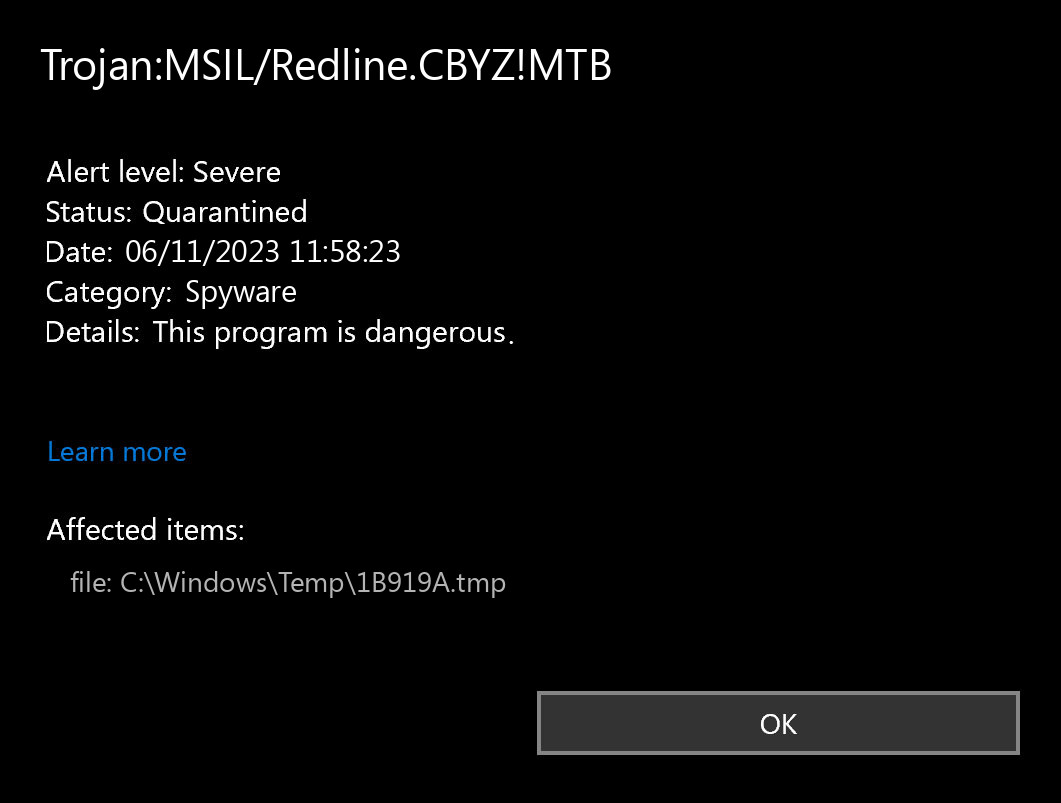
Trojan:MSIL/Redline.CBYZ!MTB Detection Overview
The Trojan:MSIL/Redline.CBYZ!MTB detection you can see in the lower right side is demonstrated to you by Microsoft Defender. That anti-malware application is quite OK at scanning, however, prone to be mainly unreliable. It is vulnerable to malware invasions, it has a glitchy interface and bugged malware removal capabilities. For this reason, the pop-up which states about the Redline is just an alert that Defender has spotted it. To remove it, you will likely need to make use of another anti-malware program.
Having Trojan:MSIL/Redline.CBYZ!MTB malware in your system is not a pleasant thing from any perspective. The worst problem is that you will barely see anything wrong. Key feature of any spyware is being as stealthy as possible. Some Redline samples also can perform self-removal after gathering all the valuable info present on the PC. Then, it will be nearly impossible to uncover the flow of events and understand how your accounts were hacked. Variants of spyware that aim at long-term action can target the specific folder in the system or file type. After that, files grabbed in that way will be put for sale on the Darknet – at one of its numerous forums with stolen data.
Spyware Summary:
| Name | Redline Spyware |
| Detection | Trojan:MSIL/Redline.CBYZ!MTB |
| Damage | Steal personal data contained in the attacked system. |
| Fix Tool | See If Your System Has Been Affected by Redline Spyware |
Is Trojan:MSIL/Redline.CBYZ!MTB dangerous?
As I have pointed out earlier, any malware is dangerous. And Trojan:MSIL/Redline.CBYZ!MTB is not even close to making more disturbance than real damage. The most misleading quality of this malware is the fact you cannot spectate its activity in any way, other than with the use of anti-malware software scanning. And while you are having no clue, fraudsters who delivered their nasty thing to your system are starting to count the money. Darknet offers numerous opportunities to sell spyware logs for a hefty sum – especially when these logs are newly-collected. And you’d better not imagine what will happen to your accounts when other crooks will put their hands on your credentials.
However, things may have much faster turnover. In some cases, crooks are delivering their virus precisely to the user they are going to rob. Spyware is priceless when it comes to grabbing credentials, and some samples target precisely at online banking accounts or cryprocurrency wallets. One may say, giving spyware a run is the same as sending all your money to fraudsters.


Leave a Comment