REvil ransomware gang is disintegrating, slowly but surely. Their network was compromised, then one of their key figures deanonymized, and now the affiliates’ heads are falling. Seems that law enforcement who perform this operation have a pleasure to mock the cybercriminals in that way.
Europol arrested REvil affiliates in November 2021
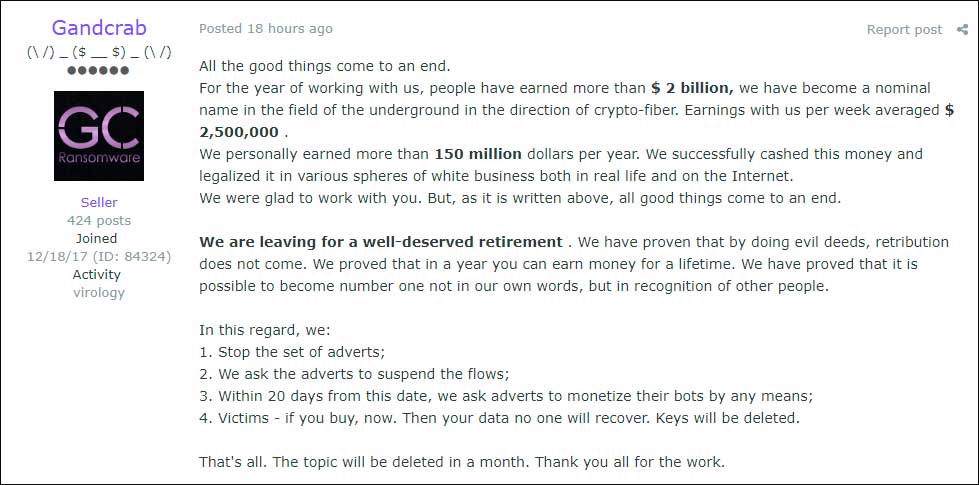
The overall campaign of law enforcements from the US and Europe against the REvil group has been held since 2019. At that point, their name was Sodinokibi. Some of the analysts also link the REvil/Sodinokibi group to GandCrab – another infamous ransomware gang. They are famous as the first group that claimed the voluntary shutdown. As they said at the end of 2018, “we got over two billion dollars, which will be enough even for our grandchildren”. Possibly, they discovered that this sum is way too little.
In 2019 the FBI and Europol paid attention to that group for the first time. Since that time, they captured 5 people who got their accusations for acting as REvil/Sodinokibi affiliates. Europol reported about capturing another two just several days ago. On November 4th, Kuwaiti authorities arrested two affiliates who had been with this “family” since GandCrab times.
GoldDust operation
GoldDust is a codename of an anti-ransomware operation that was started in Romania. Besides Romanian law enforcement, FBI and Europol, the local authorities of France, Germany and Ukraine joined in the process. Exactly, this operation is not just a “global” anti-ransomware – it aims at the Sodinokibi/REvil group. Together with the NoMoreRansom project, the aforementioned authorities captured 7 affiliates, saved over 49 thousand systems and €60 million that were about to be paid as ransom.
The last of the REvil affiliates the GoldDust actors have captured was a Ukrainian citizen, who took part in the cyberattack on Kaseya. The downtime of this MSP provider affected almost 1500 companies that interact with Kaseya. By the way, some analysts count the beginning of the end of the REvil group exactly from this cyberattack. During it, their operator made a very silly mistake, which led to the servers compromising and losing the potential ransom of €70 million.
Overall picture. REvil has one leg in the grave
In fact, analysts considered the REvil “dead” in mid-October, when one of their operators uncovered the fact of network compromising and decided to shut down the Darknet facilities. Earlier, they had a two-month shutdown after their failure with the Kaseya attack. The FBI started some serious actions against REvil a bit earlier – in March 2021. The reason for that interest is pretty simple – the attack on Acer Corporation. Acer paid $50 million, which is currently the highest ransom ever.
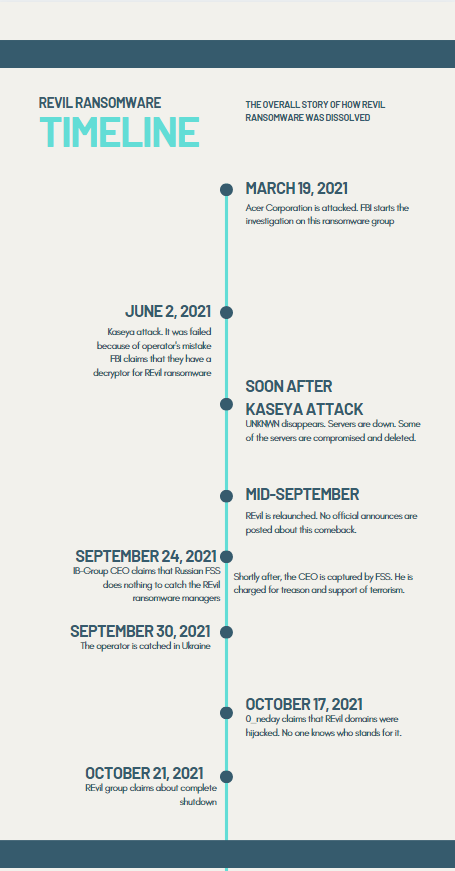
The timeline of the things happened to REvil group in 2021
Cybersecurity analysts divide at what will happen to REvil in future. After such an unprecedented deanonymization, compromising the darknet facilities, nuking the image and capturing one affiliate after another, the only visible way is to go away from the ransomware market. Earlier, other ransomware gangs committed shutdowns even having fewer problems than REvil has now. But even reborn under the other name, as they did earlier, will likely be useless at throwing off the tail from the FBI. They have too much to rebuild to avoid being recognized, even with other group names.
User Review
( votes)


