On February 9, 2022, amazing news appeared for the victims of Maze, Sekhmet and Egregor ransomware. The master decryption key was released by the developer of both malicious groups, which changed each other through time. About...
Maze, Egregor ransomware decryption keys released by the developer
Maze and Egregor ransomware operators earned more than $75 million in bitcoins
Analyst1 security researchers have calculated that the hackers behind the Maze and Egregor ransomware have already earned more than $75 million in ransoms from their victims. The company’s data is based on transactions that...
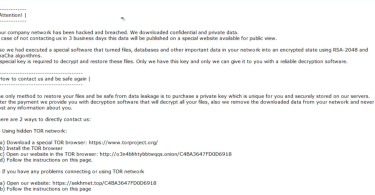
Ransom:Win32/Egregor.XX!MTB
What is Ransom:Win32/Egregor.XX!MTB infection? In this post you will find regarding the definition of Ransom:Win32/Egregor.XX!MTB and its adverse impact on your computer. Such ransomware are a type of malware that is specified by...
Ransom:Win32/Egregor.BM!MSR
What is Ransom:Win32/Egregor.BM!MSR infection? In this short article you will find regarding the meaning of Ransom:Win32/Egregor.BM!MSR and also its unfavorable impact on your computer. Such ransomware are a form of malware that...
Egregor ransomware attack disrupted public transport in Vancouver
ZDNet reports that the Egregor ransomware attack disrupted the work of TransLick, a public transport operator in Vancouver, Canada. incident occurred this week, December 1, 2020, and as a result, Vancouver residents were unable...
Ransom:Win32/Egregor.A!MTB
What is Ransom:Win32/Egregor.A!MTB infection? In this short article you will certainly discover concerning the meaning of Ransom:Win32/Egregor.A!MTB and also its unfavorable influence on your computer. Such ransomware are a form...
Ransom:Win32/Egregor!MSR
What is Ransom:Win32/Egregor!MSR infection? In this post you will certainly locate about the definition of Ransom:Win32/Egregor!MSR as well as its adverse influence on your computer system. Such ransomware are a type of malware...
Egregor ransomware attacked largest Chilian retailer Cencosud
Bleeping Computer reports that the Egregor ransomware attacked the Chilean company Cencosud, one of the largest retailers in South America. me remind you that Egregor began its activity quite recently – in early September...



![What is the Win32:Evo-gen [Trj] virus?](https://howtofix.guide/wp-content/uploads/2019/11/trojan-ransom-375x195.jpg)


