PEZI Virus
Pezi is a DJVU family of ransomware-type infections1. This infection encrypts your private files (video, photos, documents). The infected files can be tracked by specific “.pezi” extension. So, you can’t use them at all.
In this article I will try to help you remove Pezi virus for free. Also I will assist you in decoding your encrypted files.
What is “Pezi”?
Pezi can be correctly identify as a ransomware infection.
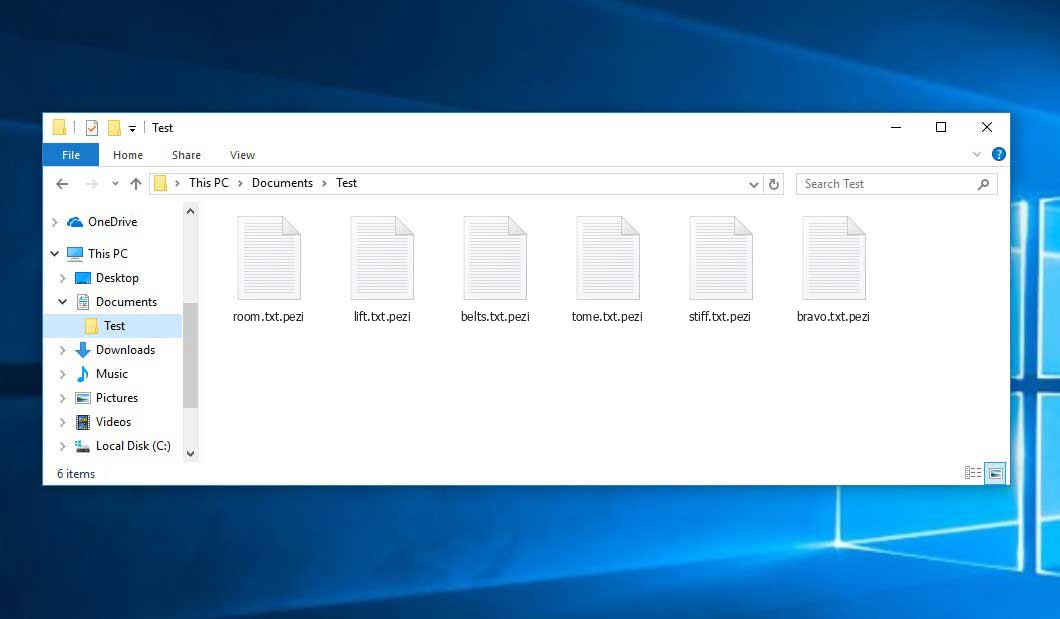
Ransomware is a kind of virus that encrypted your documents and then forces you to pay to restore them. DJVU (aka STOP) ransomware family was first revealed and discovered by virus analyst Michael Gillespie2.Pezi is basically similar to other ransomware like: Covm, Koti, Mzlq. Pezi encrypted all common file types. Hence, you cannot open the own documents or photos. Pezi adds its particular “.pezi” extension into all files. For example, the file “video.avi”, will be amended into “video.avi.pezi”. As soon as the encryption is accomplished, Pezi creates a specific file “_readme.txt” and adds it into all folders that contain the modified files.
Here is a short info for the Pezi virus:
| Ransomware family3 | DJVU/STOP4 ransomware |
| Extension | .pezi |
| Ransomware note | _readme.txt |
| Ransom | From $490 to $980 (in Bitcoins) |
| Contact | [email protected], [email protected] |
| Detection | Win32/GameHack.F potentially unsafe, Strictor.191993, Trojan-Ransom.Win32.Encoder.bll |
| Symptoms | Your files (photos, videos, documents) have a .pezi extension and you can’t open it |
| Fix Tool | See If Your System Has Been Affected by .pezi file virus |
This text asking payment is for get files back via decryption key:
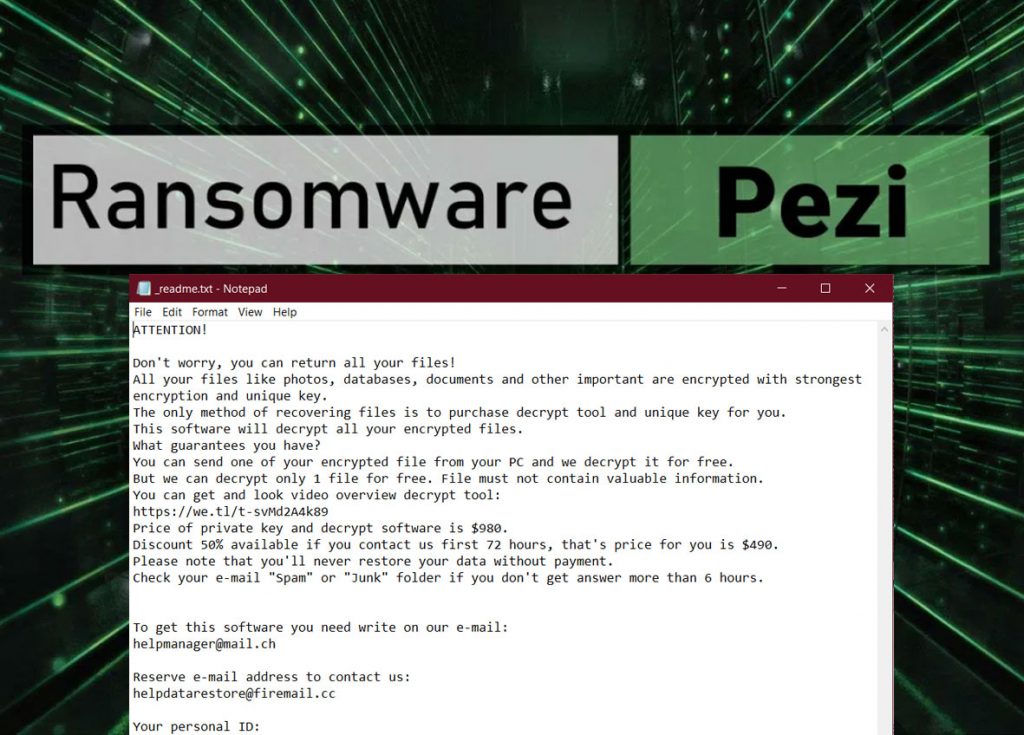
The scary alert demanding from users to pay the ransom to decrypt the compromised data contains these frustrating warnings
The cryptography algorithm used by Pezi is AES-256. So, if your files got encrypted with a specific decryption key, which is totally unique and there are no other copies. The sad reality is that it is impossible to recover the information without the unique key available.
In case if Pezi worked in online mode, it is impossible for you to gain access to the AES-256 key. It is stored on a distant server owned by the criminals who promote the Pezi infection.
For receiving decryption key the payment should be $980. To obtain the payment details, the victims are encouraged by the message to contact the frauds by email ([email protected]), or via Telegram.
Do not pay for Pezi!
Please, try to use the available backups, or Decrypter tool
_readme.txt file also indicates that the computer owners must get in touch with the Pezi representatives during 72 hours starting from the moment of files where encrypted. On the condition of getting in touch within 72 hours, users will be granted a 50% rebate. Thus the ransom amount will be minimized down to $490). Yet, stay away from paying the ransom!
I certainly advise that you do not contact these crooks and do not pay. The one of the most real working solution to recover the lost data – just using the available backups, or use Decrypter tool.
Since the ransomware distributors has the only target – your money – they will do everything to force you to pay them. At first, they may be gentle and offer you to decrypt 2-3 of your files. They really have a decryptor, exactly, so you will get your decrypted files back. But no one can force them to give you the decryption key after you’ve paid them!
And the popular practice that is done by ransomware distributors is database collection&sell-off. Every e-mail which contacted them is added to such database, and then sold to someone. Then, your e-mail will be spammed with ads, pseudo-invites and so on.
The peculiarity of all such viruses apply a similar set of actions for generating the unique decryption key to recover the ciphered data.
Thus, unless the ransomware is still under the stage of development or possesses some hard-to-track flaws, manually recovering the ciphered data is a thing you can’t perform. The only solution to prevent the loss of your valuable data is to regularly make backups of your crucial files.
Note that even if you do maintain such backups regularly, they ought to be put into a specific location without loitering, not being connected to your main workstation.
Such caution is needed because Pezi ransomware is able to encrypt your backups or inject your own .exe file. Anyway, all this action is needed to make your backup useless for the system restoration.
In case of the backup, created with built-in Windows tools, things maybe got even worse. According to several reports, Pezi ransomware is able to disable or even delete the backups created in such a way. The best solution is to use another backup creation tool.
The OneDrive backups can also be useless for system restoration. It starts the backup creation process without any notification and overwrites an existing backup with a new one. Hence, your normal files may be replaced by encrypted ones, and it’s very hard to control it.
For instance, the backup may be kept on the USB flash drive or some alternative external hard drive storage. Optionally, you may refer to the help of online (cloud) information storage.
Be careful while using USB-drives. Pezi ransomware can encrypt the files contained on this USB, or inject own .exe file to this USB-drive. Hence, your removable drive can become a source for ransomware infiltration to the plenty of computers.
Needless to mention, when you maintain your backup data on your common device, it may be similarly ciphered as well as other data.
For this reason, locating the backup on your main PC is surely not a wise idea.
How I was infected?
Pezi has a various methods to built into your system. But it doesn’t really matter what method was used in your case.
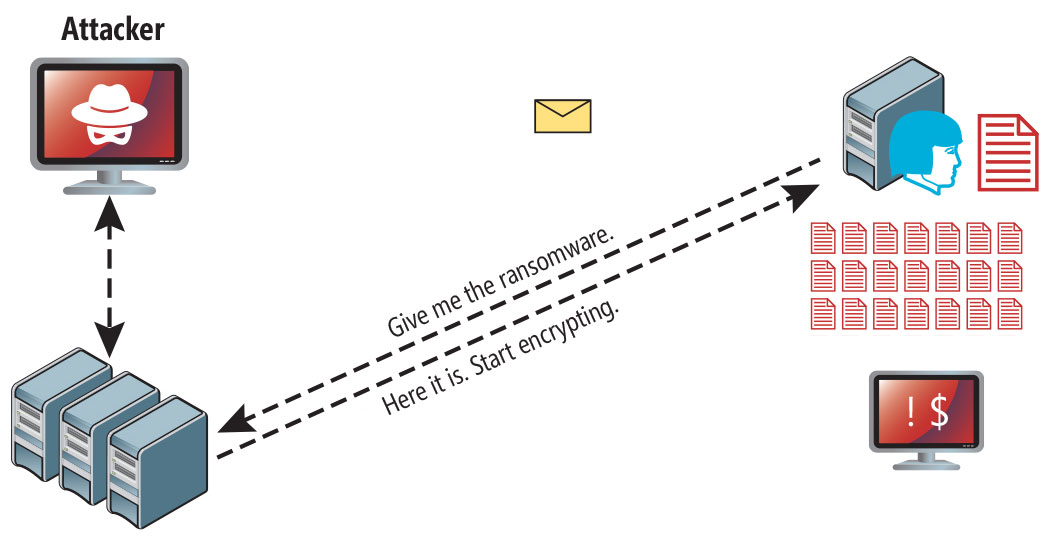
Pezi attack following a successful phishing attempt.
- hidden installation along with other apps, especially the utilities that work as freeware or shareware;
- dubious link in spam emails leading to the Pezi installer
- online free hosting resources;
- using illegal peer-to-peer (P2P) resources for downloading pirated software.
There were cases when the Pezi virus was disguised as some legitimate tool, for example, in the messages demanding to initiate some unwanted software or browser updates. This is typically the way how some online frauds aim to force you into installing the Pezi ransomware manually, by actually making you directly participate in this process.
Surely, the bogus update alert will not indicate that you are going to actually inject the Pezi ransomware. This installation will be concealed under some alert mentioning that allegedly you should update Adobe Flash Player or some other dubious program whatsoever.
You can meet a lot of users in the Internet who are offering you a help with ransomware decryption. No one can warrant their intensions and the real result. They can both help you and make your things even worse. Be very careful and caution when claiming such help.
Of course, the cracked apps represent the damage too. Using P2P is both illegal and may result in the injection of serious malware, including the Pezi ransomware.
Besides the cracked apps, the cracking facilities may also be dangerous. Different keygens, or any other software that helps the user to evade the license checking process. The majority of such software loses their ability to crack the programs till the first month of its existence, but they still can be downloaded. And such “dead” keygens and crackers are the perfect carrier for different malware, including Pezi ransomware.
To sum up, what can you do to avoid the injection of the Pezi ransomware into your device? Even though there is no 100% guarantee to prevent your PC from getting damaged, there are certain tips I want to give you to prevent the Pezi penetration. You must be cautious while installing free software today.
Make sure you always read what the installers offer in addition to the main free program. Stay away from opening dubious email attachments. Do not open files from the unknown addressees. Of course, your current security program must always be updated.
The malware does not speak openly about itself. It will not be mentioned in the list of your available programs. However, it will be masked under some malicious process running regularly in the background, starting from the moment when you launch your PC.
The message by the Pezi ransomware states the following frustrating information:
ATTENTION! Don't worry, you can return all your files! All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: https://we.tl/t-WJa63R98Ku Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that's price for you is $490. Please note that you'll never restore your data without payment. Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours. To get this software you need write on our e-mail: [email protected] Reserve e-mail address to contact us: [email protected] Your personal ID: XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
The image below gives a clear vision of how the files with “.pezi” extension look like:
How to remove Pezi virus?
In addition to encode a victim’s files, the Pezi virus has also started to install the Azorult Spyware on PC to steal account credentials, cryptocurrency wallets, desktop files, and more.
Reasons why I would recommend GridinSoft5
Download Removal Tool.
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

How to decrypt .pezi files?
Restore solution for big “.pezi files“
Try removing .pezi extension on a few BIG files and opening them. Either the Pezi ransomware read and did not encrypt the file, or it bugged and did not add the filemarker. If your files are very large (2GB+), the latter is most likely. Please, let me know in comments if that will work for you.
The newest extensions released around the end of August 2019 after the criminals made changes. This includes Sqpc, Mpal, Qewe, etc.
As a result of the changes made by the criminals, STOPDecrypter is no longer supported. It has been removed and replaced with the Emsisoft Decryptor for STOP Djvu Ransomware developed by Emsisoft and Michael Gillespie.
You can download free decryption tool here: Decryptor for STOP Djvu.
Download and run decryption tool.
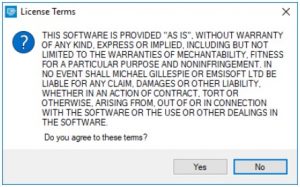
Make sure to launch the decryption utility as an administrator. You need to agree with the license terms that will come up. For this purpose, click on the “Yes” button:
As soon as you accept the license terms, the main decryptor user interface comes up:
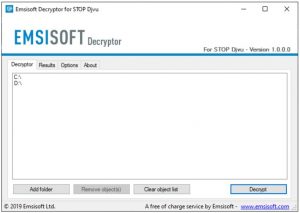
Select folders for decryption.
Based on the default settings, the decryptor will automatically populate the available locations in order to decrypt the currently available drives (the connected ones), including the network drives. Extra (optional) locations can be selected with the help of the “Add” button.
Decryptors normally suggest several options considering the specific malware family. The current possible options are presented in the Options tab and can be activated or deactivated there. You may locate a detailed list of the currently active Options below.
Click on the “Decrypt” button.
As soon as yo add all the desired locations for decryption into the list, click on the “Decrypt” button in order to initiate the decryption procedure.
Note that the main screen may turn you to a status view, letting you know of the active process and the decryption statistics of your data:
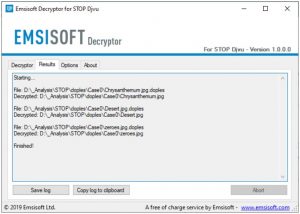
The decryptor will notify you as soon as the decryption procedure is completed. If you need the report for your personal papers, you can save it by choosing the “Save log” button. Note that it is also possible to copy it directly to your clipboard and to paste it into emails or forum messages if you need to do so.
Frequently Asked Questions
Video Guide
It’s my favorite video tutorial: How to use GridinSoft Anti-Malware and Emsisoft Decryptor for fix ransomware infections.
I need your help to share this article.
It is your turn to help other people. I have written this guide to help users like you. You can use buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Ransomware-type infection: https://en.wikipedia.org/wiki/Ransomware
- Twitter: https://twitter.com/demonslay335
- My files are encrypted by ransomware, what should I do now?
- About DJVU (STOP) Ransomware.
![]() German
German ![]() Japanese
Japanese ![]() Spanish
Spanish ![]() Portuguese (Brazil)
Portuguese (Brazil) ![]() French
French ![]() Turkish
Turkish ![]() Chinese (Traditional)
Chinese (Traditional) ![]() Korean
Korean


Hi, I have a few questions. Can I please ask them bit by bit? Please bare with me?
1. How long does it usually take to find a decryptor? Especially for a new virus?
Cause I bought the GridinSoft software. It cleaned my PC but all my files are still decrypted.
I was also infected with the PEZI ransomware on the 30th May, 2020. All my files are currently encrypted.
I tried using the EMSISOFT Decryptor but unfortunately it showed that the the key for it is unavailable yet with the line “No key for New Variant online ID: 7XneuDyvOJpYq1Nlvi2e3nBiSojvIgYZcbryZerQ
Notice: this ID appears to be an online ID, decryption is impossible”
I’m hoping it would be updated soon in the days to come.
same with me just got attacked by the virus 3 days ago and the online key variant is not yet found and im fucked up